Ways to Secure WiFi Network Using User Role
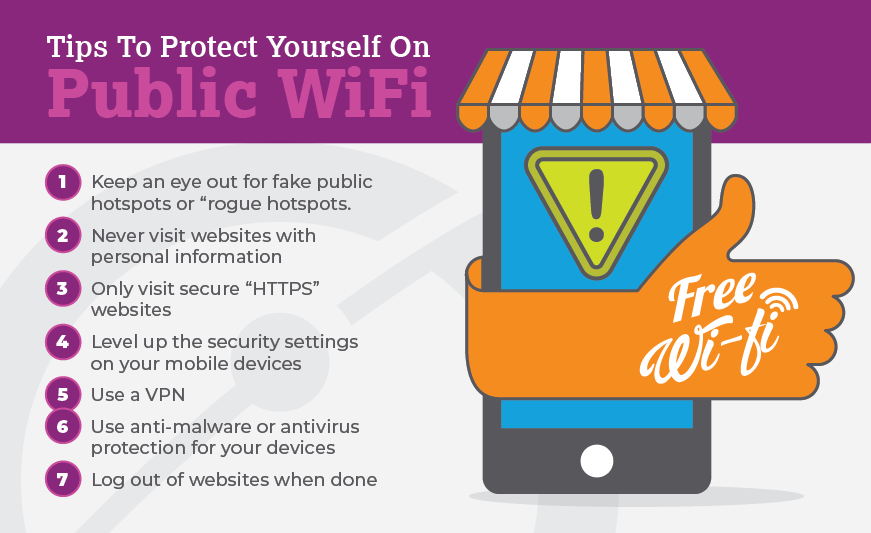
Securing your WiFi network is a top priority in today's digital age. With the increasing number of devices connected to the internet, it's not uncommon for hackers to target vulnerable networks to steal sensitive information or disrupt operations. In this article, we'll explore the ways to secure your WiFi network using user role, providing you with the necessary tools to protect your network from unauthorized access.
Understanding User Role in WiFi Security
User role is a security feature that assigns different levels of access to network users based on their roles or privileges. By defining user roles, you can restrict access to sensitive areas of your network and ensure that only authorized users can perform specific actions. This approach not only enhances security but also streamlines network management and reduces the risk of data breaches.
Benefits of Using User Role in WiFi Security
- Improved Security:** User role-based access control ensures that sensitive areas of your network are protected from unauthorized access.
- Reduced Risks:** By limiting access to specific users, you reduce the risk of data breaches and cyber attacks.
- Simplified Network Management:** User role-based access control streamlines network management by allowing you to easily assign and revoke access rights.
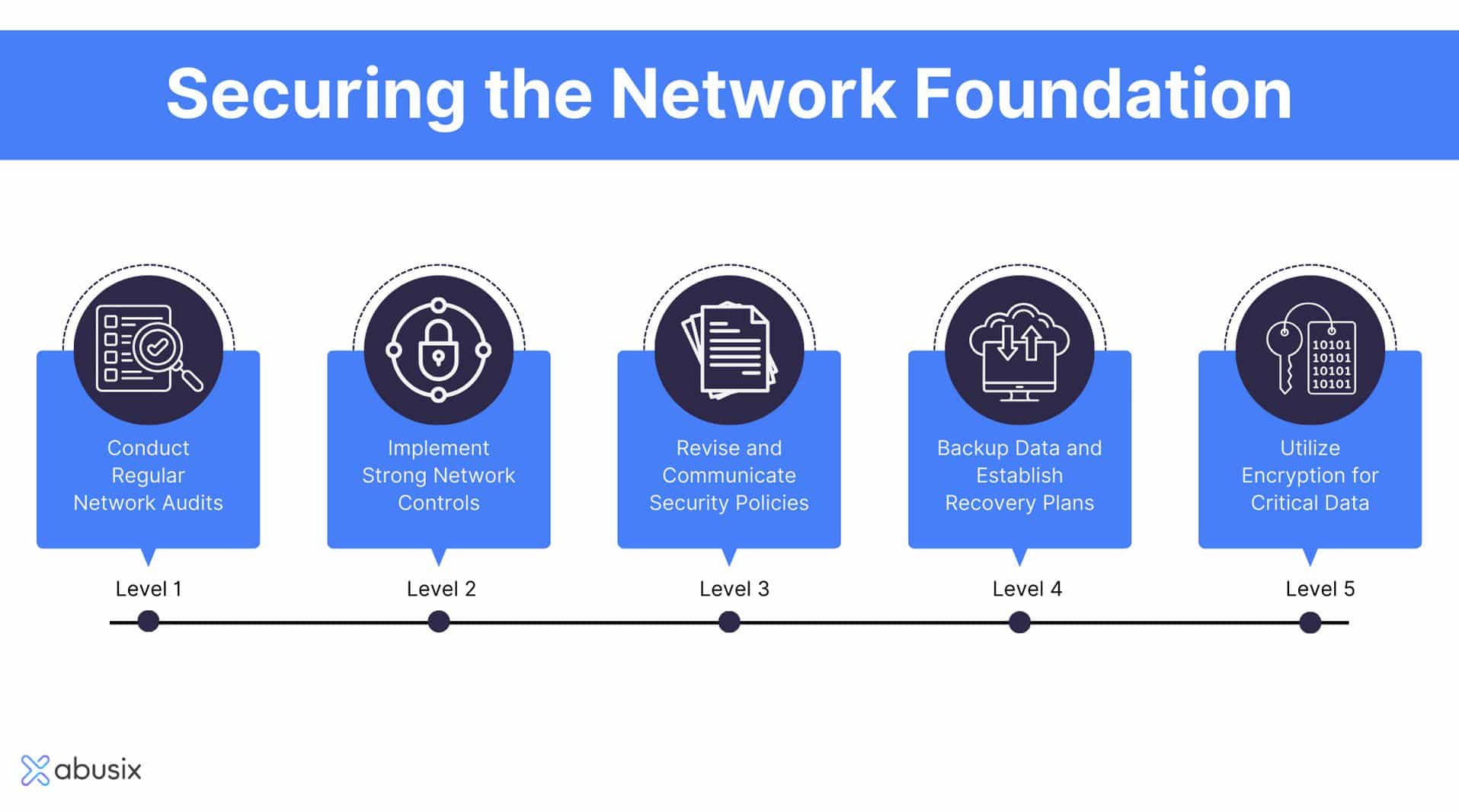
Ways to Secure WiFi Network Using User Role
Here are some ways to secure your WiFi network using user role:

This particular example perfectly highlights why Ways To Secure Wifi Network Using User Role is so captivating.
1. Implement Role-Based Access Control
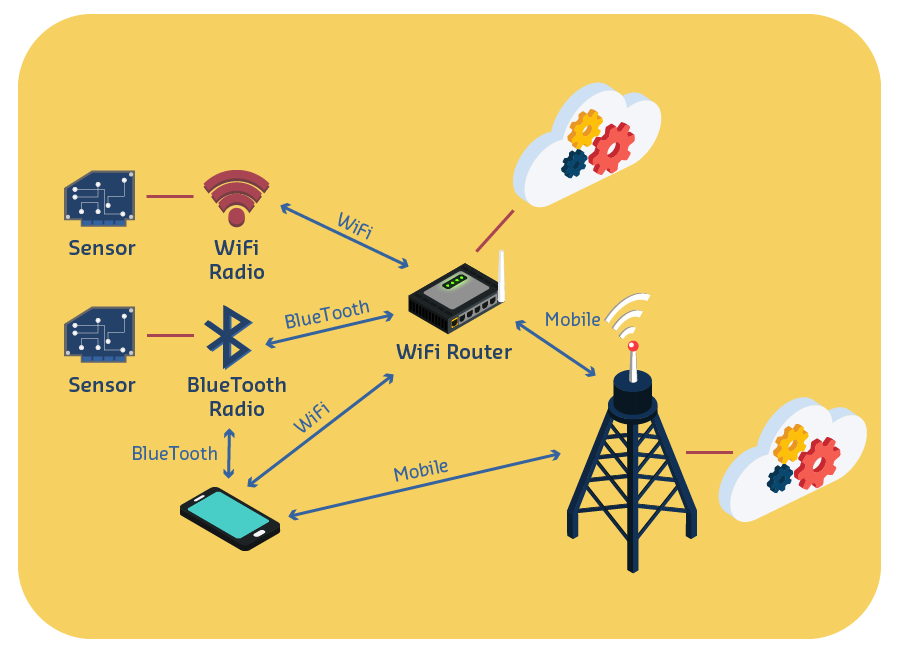
Role-based access control (RBAC) is a security feature that assigns different levels of access to network users based on their roles or privileges. By defining user roles, you can restrict access to sensitive areas of your network and ensure that only authorized users can perform specific actions.
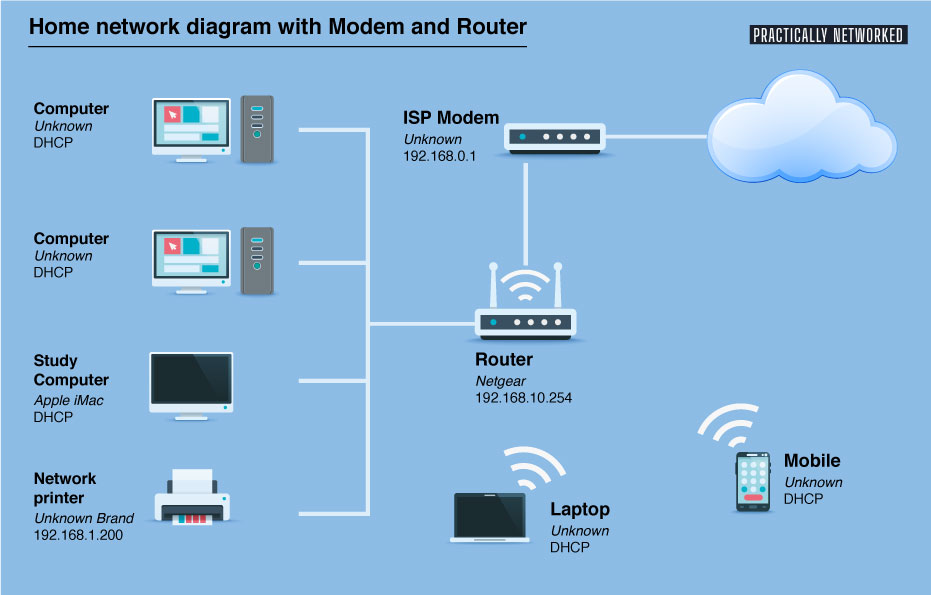
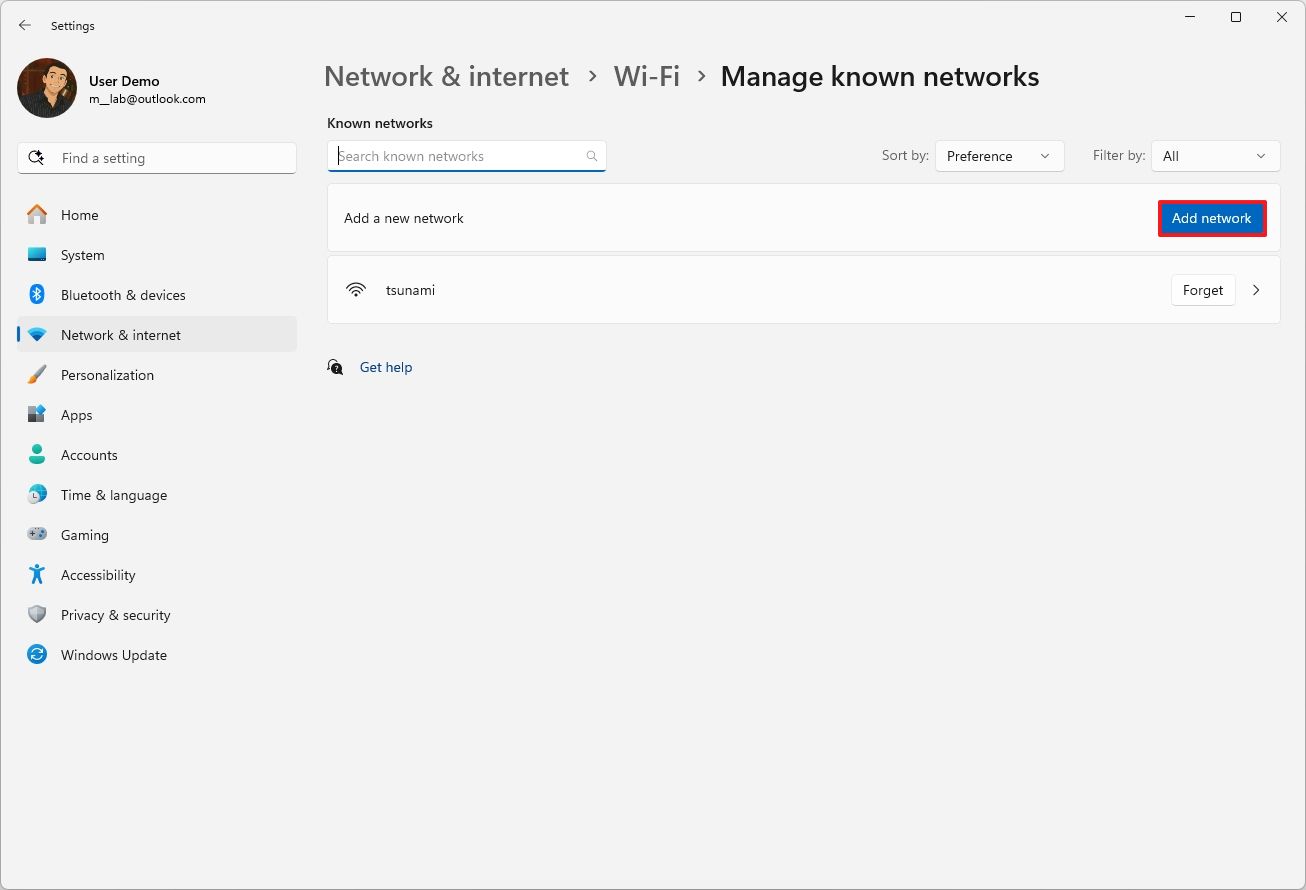
Integrating your WiFi network with Active Directory can help you manage user roles and access rights more efficiently. Active Directory provides a centralized platform for managing user accounts, groups, and permissions, making it easier to implement role-based access control.
3. Leverage RADIUS Server Configuration
A RADIUS (Remote Authentication Dial-In User Service) server is a network security feature that provides a centralized platform for authenticating and authorizing users. By configuring your RADIUS server to use user role-based access control, you can ensure that only authorized users can access your network.
4. Implement Certificate-Based Authentication
Certificate-based authentication is a security feature that uses digital certificates to verify users and devices before granting network access. By implementing certificate-based authentication, you can ensure that only authorized users and devices can access your network.
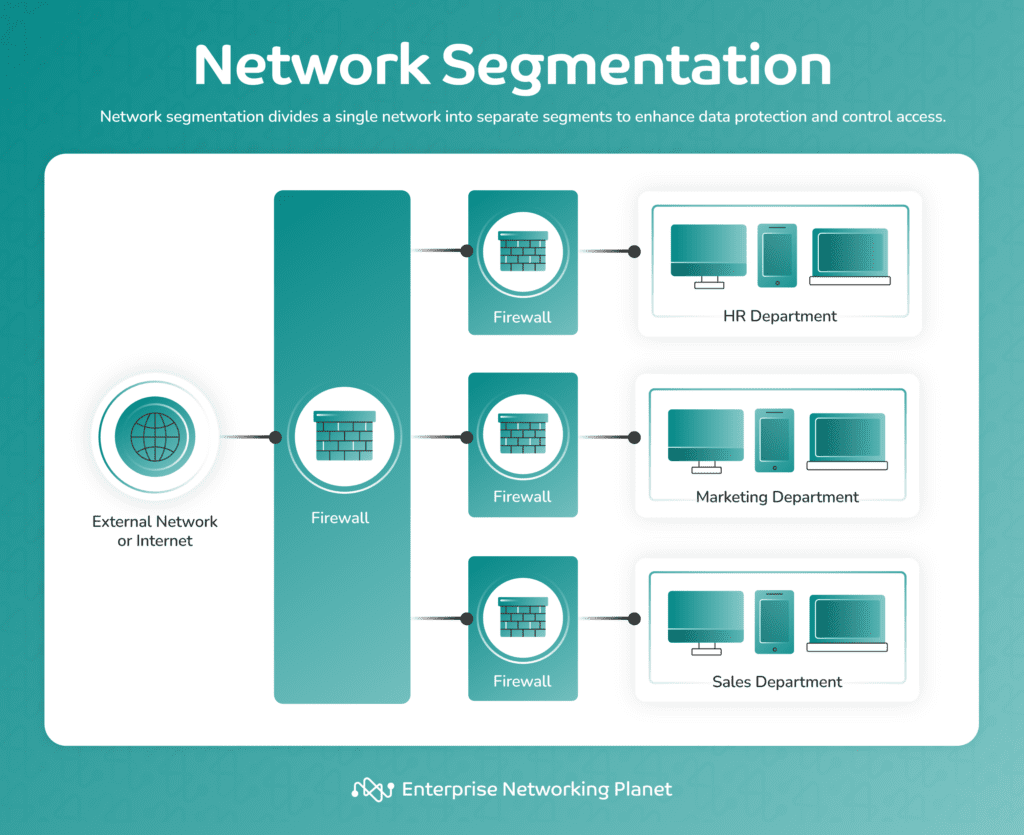
5. Use Network Segmentation
Network segmentation involves dividing your network into smaller, isolated segments to reduce the attack surface. By implementing network segmentation, you can restrict access to sensitive areas of your network and ensure that only authorized users can access specific resources.
Conclusion
Securing your WiFi network using user role is a critical aspect of network security. By implementing role-based access control, Active Directory integration, RADIUS server configuration, certificate-based authentication, and network segmentation, you can protect your network from unauthorized access and ensure the confidentiality, integrity, and availability of your data. Remember, security is a continuous process that requires regular monitoring and maintenance to stay ahead of emerging threats.
Additional Resources
- Cisco Meraki:** A cloud-managed networking platform that provides robust security features, including user role-based access control.
- Ubiquiti UniFi:** A wireless network platform that offers robust security features, including user role-based access control and RADIUS server configuration.
- IBM Security:** A comprehensive security platform that provides robust features, including user role-based access control, certificate-based authentication, and network segmentation.