How to Protect Identity from Cyber Attacks:
As technology advances, cyber threats have become increasingly sophisticated, putting individuals and organizations at risk of identity theft, financial loss, and reputational damage. Protecting your identity from cyber attacks requires a multi-faceted approach that involves being proactive, vigilant, and informed. In this article, we will discuss the importance of identity protection, common cyber threats, and provide effective tips on how to safeguard your identity from cyber attacks.
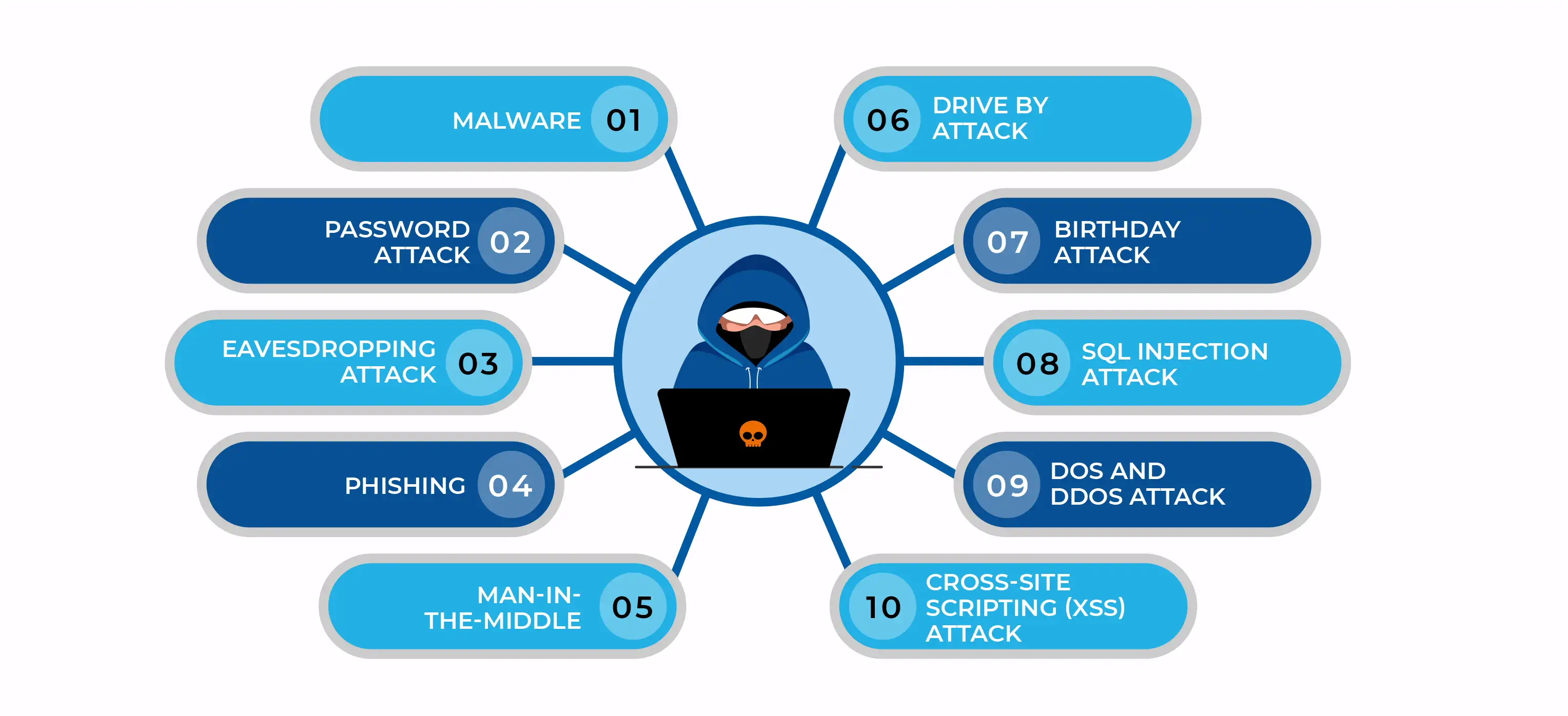
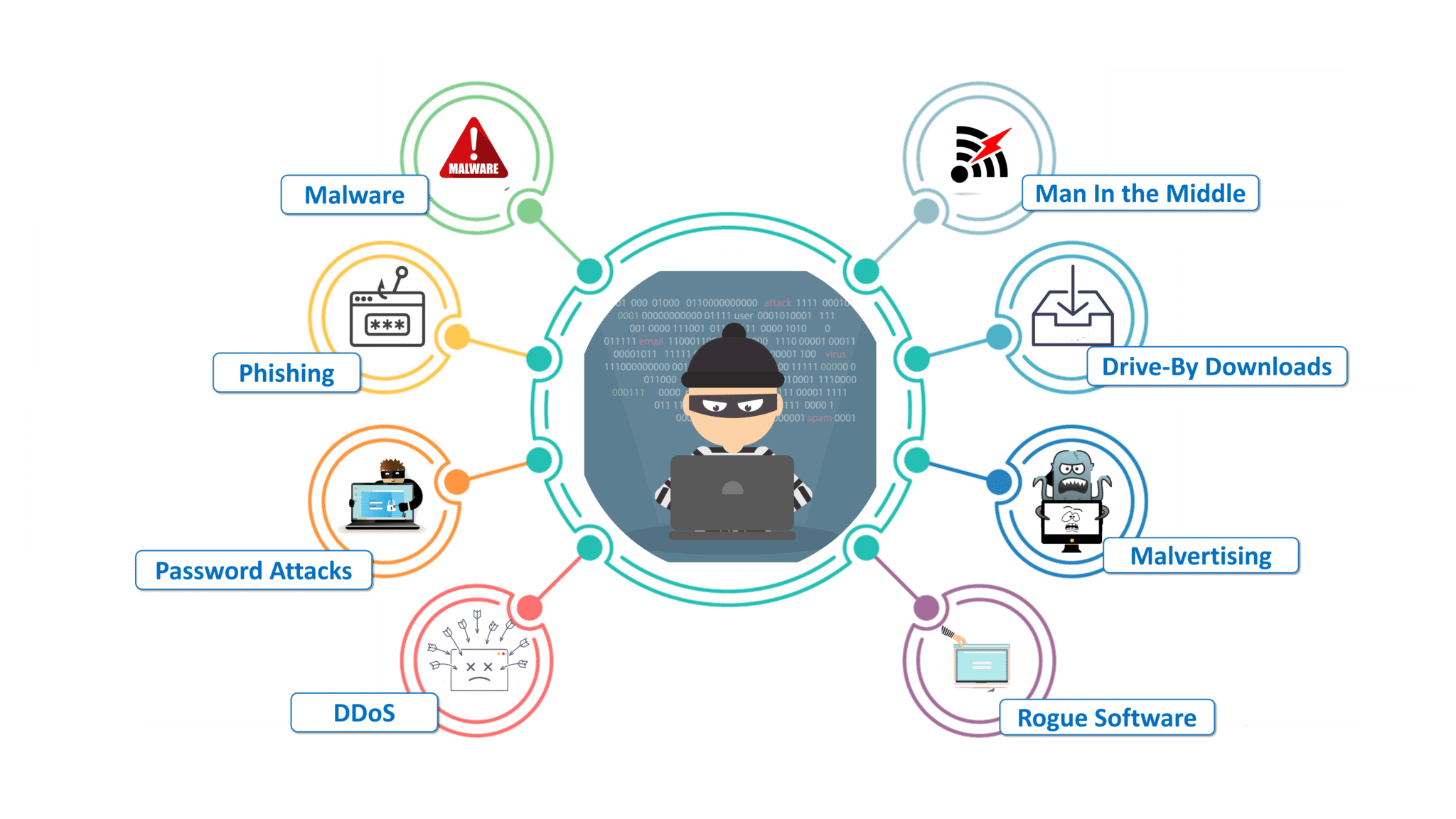
Understanding Cyber Attacks
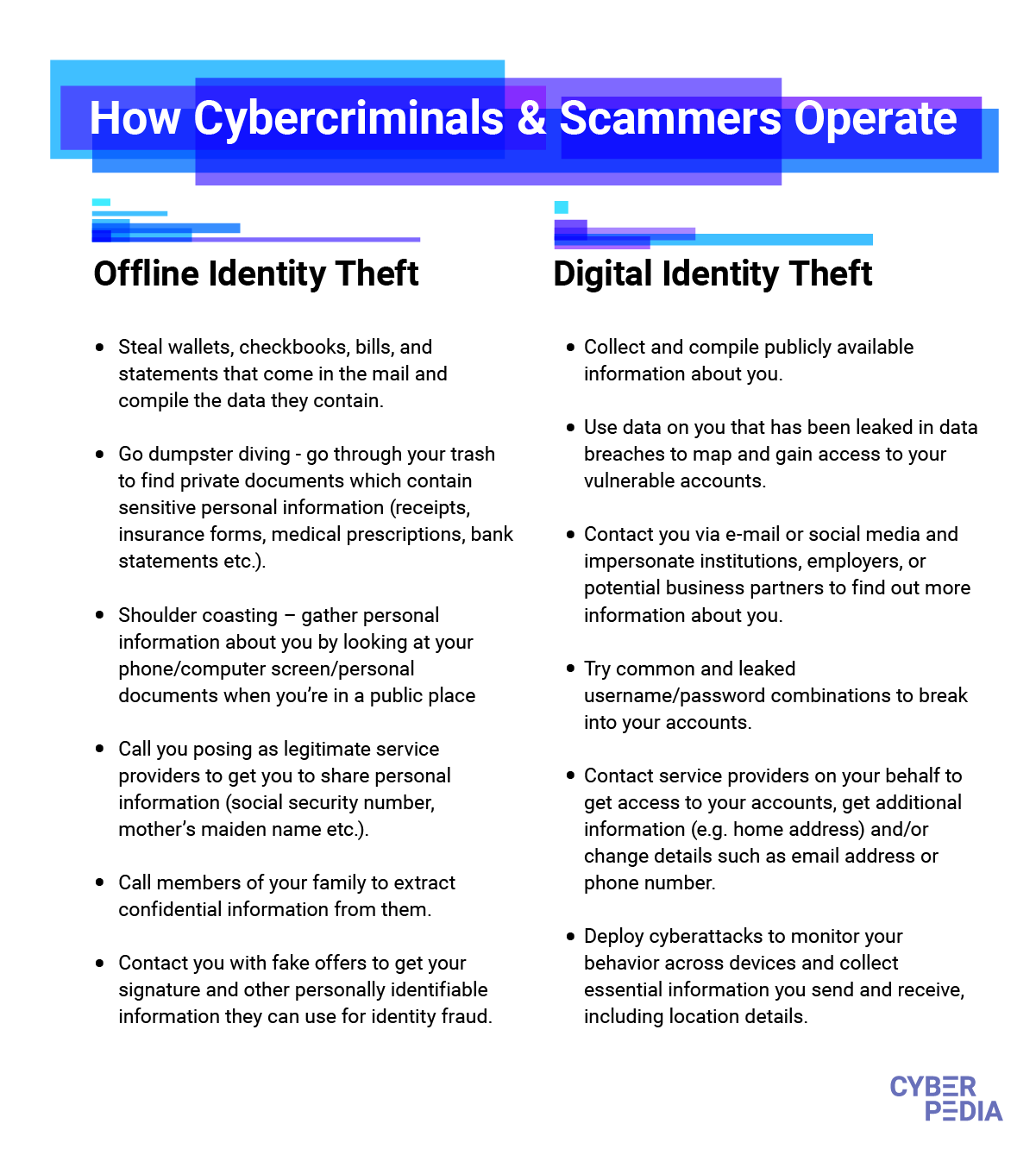
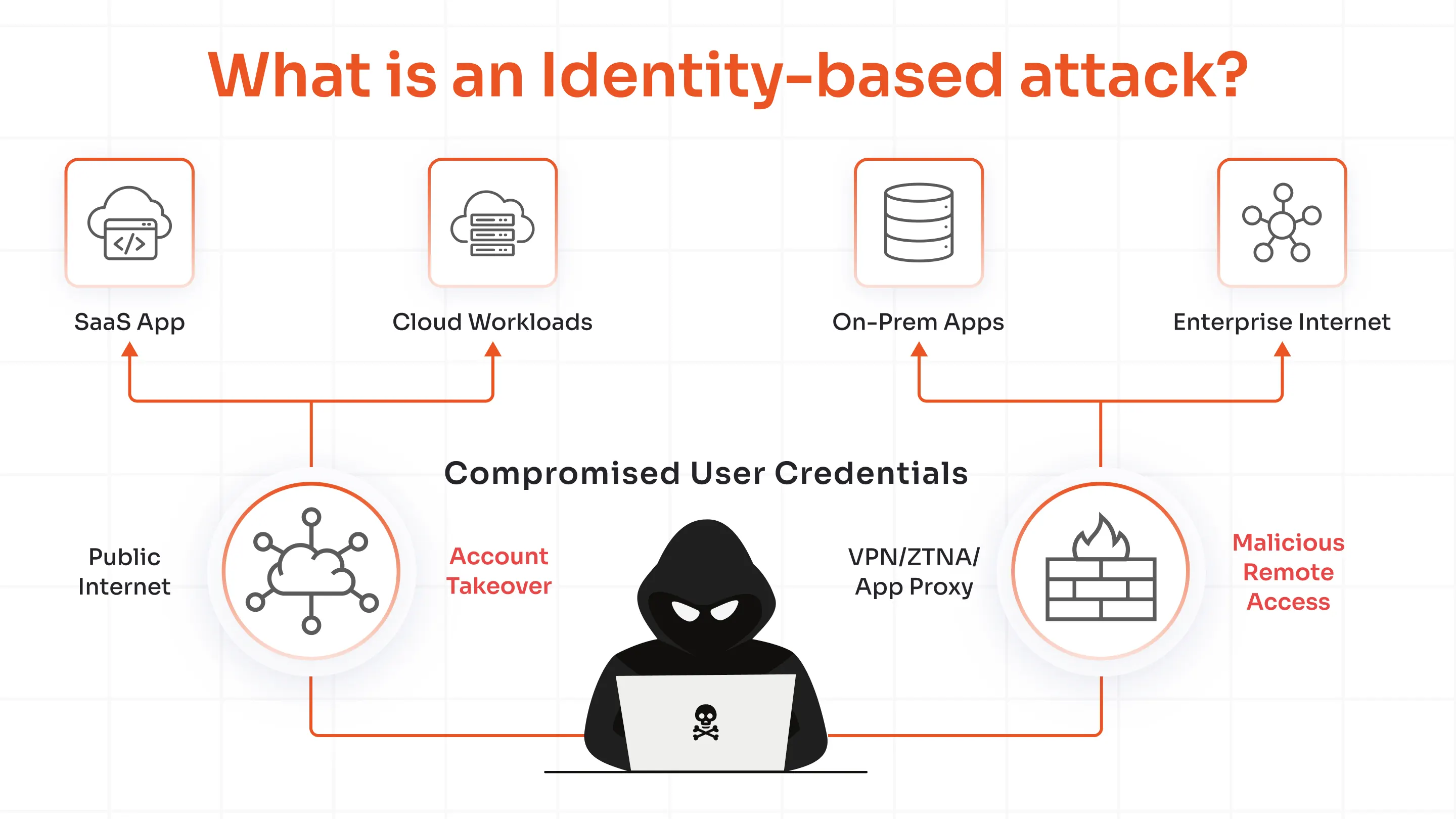
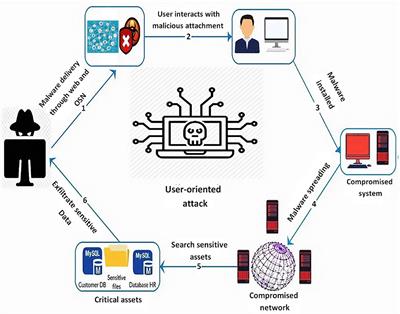
A cyber attack refers to any malicious activity that targets computer systems, networks, and devices with the intention of causing harm, stealing sensitive data, or disrupting normal operations. These attacks can take many forms, including ransomware, phishing, malware, and denial-of-service attacks. To protect yourself from cyber attacks, it's essential to understand that they can happen to anyone, regardless of their technical expertise or the size of their organization.
Types of Cyber Attacks
- Ransomware: A type of malware that encrypts your files and demands a ransom in exchange for the decryption key.
- Phishing: A tactic used by scammers to trick individuals into revealing sensitive information, such as passwords or credit card numbers.
- Malware: Software that is designed to harm or exploit a computer system.
- Denial-of-Service (DoS): A type of attack that floods a system with traffic to make it unavailable to users.
Protecting Your Identity from Cyber Attacks
To protect your identity from cyber attacks, follow these effective tips:
1. Use Strong and Unique Passwords
2. Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone or a fingerprint scan, in addition to your password.
3. Install Anti-Virus Software
Anti-virus software helps detect and remove malware that can compromise your identity. Ensure you install a reputable anti-virus software and keep it updated.
4. Monitor Your Credit Report
Regularly reviewing your credit report helps you detect any suspicious activity that may indicate identity theft. You can request a free credit report from each of the three major credit bureaus once a year.

5. Be Cautious of Phishing Attacks
Phishing attacks often involve emails or messages that appear to be legitimate but are designed to trick you into revealing sensitive information. Be cautious of links and attachments from unknown sources, and never provide sensitive information via email or text message.
A VPN helps encrypt your internet traffic, making it more difficult for hackers to intercept your data. Use a reputable VPN service when using public Wi-Fi or accessing sensitive information online.
7. Keep Your Devices and Software Updated
Ensure your devices, operating system, and software are up-to-date with the latest security patches and updates. This helps protect against known vulnerabilities and potential attacks.
8. Use a Password Manager
A password manager helps generate and store unique, complex passwords for all your online accounts. Consider using a reputable password manager to streamline your password management.

As we can see from the illustration, How To Protect Identity From Cyber Attacks has many fascinating aspects to explore.
9. Be Aware of Public Wi-Fi
Public Wi-Fi networks may be compromised, allowing hackers to intercept your data. Use a VPN or avoid accessing sensitive information when connected to public Wi-Fi.
10. Educate Yourself
Stay informed about common cyber threats and best practices for protecting your identity. Continuously update your knowledge to stay ahead of evolving cyber threats.
Conclusion
Protecting your identity from cyber attacks requires a proactive and informed approach. By following these tips and staying vigilant, you can significantly reduce the risk of identity theft, financial loss, and reputational damage. Remember, safeguarding your identity is a continuous process that requires ongoing attention and improvement.
Additional Resources
For more information on cybersecurity and identity protection, consider visiting the following resources: