Malware Protection for Cloud Computing Security: Your Ultimate Guide to Safeguarding Data and Applications
Cloud computing has revolutionized the way businesses operate, providing unparalleled flexibility and scalability. However, it also presents significant security challenges, particularly when it comes to malware attacks. In this article, we'll explore the importance of malware protection for cloud computing security and provide actionable insights to help you safeguard your data and applications.
Why Malware Protection is Crucial for Cloud Computing Security
Malware attacks are becoming increasingly sophisticated, and cloud-based systems are no exception. These malicious attacks can compromise your data, applications, and infrastructure, leading to serious repercussions like data breaches, unauthorized system access, and identity theft. According to IBM, the global demand for cybersecurity professionals is set to surge by 6 million, highlighting the need for robust security measures.
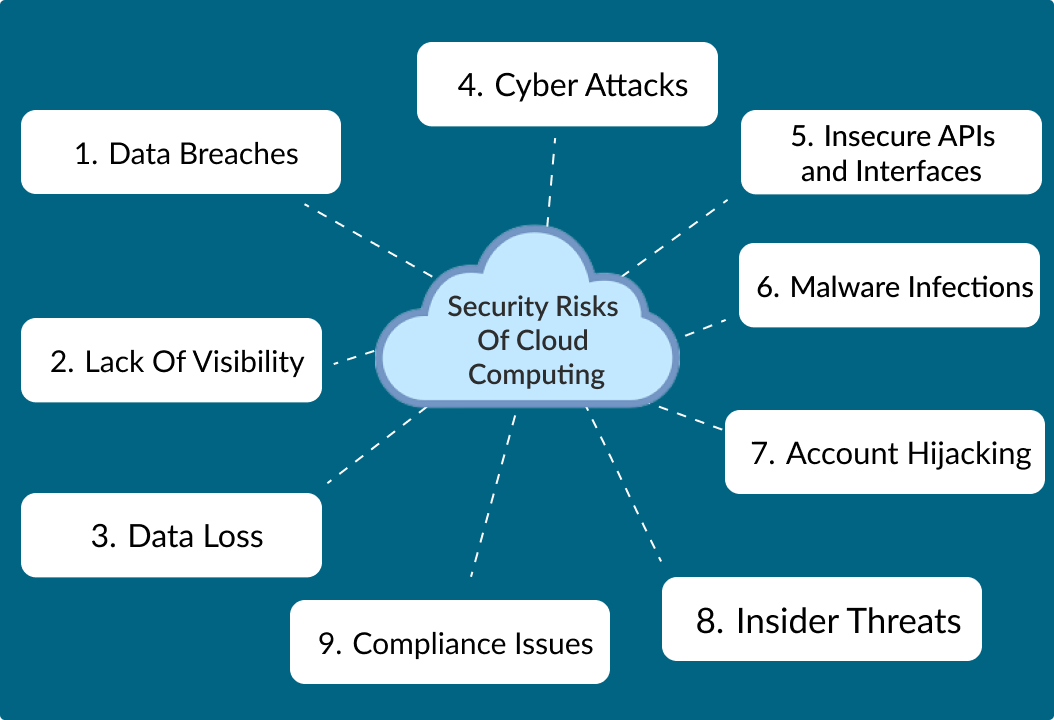
The Consequences of Malware Attacks on Cloud Computing

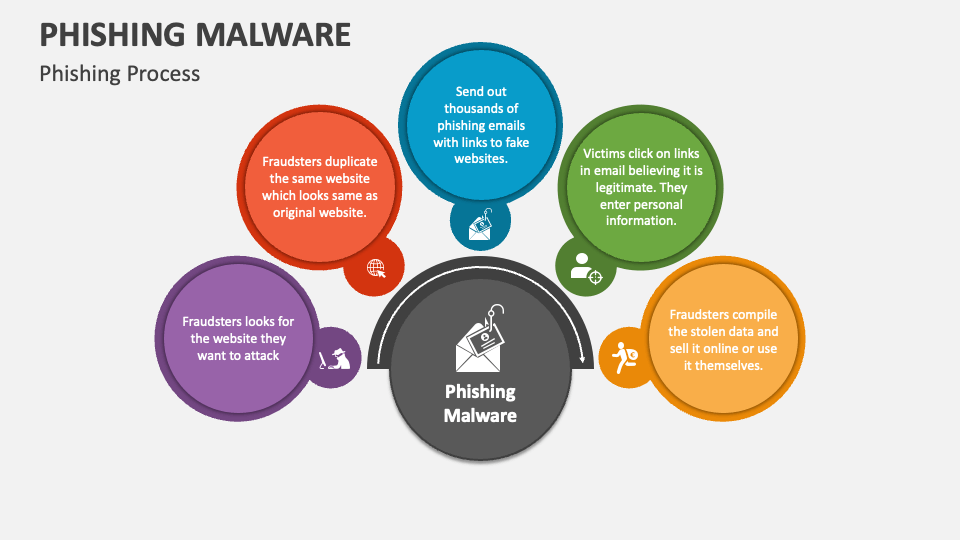
As we can see from the illustration, Malware Protection For Cloud Computing Security has many fascinating aspects to explore.
- Data breaches: Malware attacks can compromise sensitive information, leading to data breaches and unauthorized access.
- Unplanned downtime: Malware can cause systems to crash, leading to unplanned downtime and significant financial losses.
- Financial loss: Malware attacks can result in significant financial losses, as businesses may need to replace compromised systems or pay ransom demands.
- Reputation damage: A malware attack can damage your organization's reputation, leading to loss of customer trust and loyalty.
Types of Malware Threats in Cloud Computing
- File-based malware: Malware that attacks files on a system, such as ransomware or Trojan horses.
- Network-based malware: Malware that attacks network traffic, such as botnets or DDoS attacks.
- Cloud-based malware: Malware that targets cloud-based services, such as S3 buckets or cloud storage.
Best Practices for Malware Protection in Cloud Computing

This particular example perfectly highlights why Malware Protection For Cloud Computing Security is so captivating.
Implement a Multi-Layered Approach
Implementing a multi-layered approach to malware protection involves combining traditional security controls with cloud-specific measures. This includes implementing firewalls, intrusion detection systems, and antivirus software, as well as using cloud-specific security measures like cloud-based malware detection and cloud-based backup and recovery solutions.
Use Machine Learning and Artificial Intelligence
Machine learning and artificial intelligence (AI) can be used to detect and prevent malware attacks in cloud computing. AI-powered tools can analyze system behavior, detect anomalies, and prevent attacks before they occur.
Regularly Update and Patch Systems
Regularly updating and patching systems is critical to reducing the risk of malware attacks.PATCH systems with the latest security patches, and ensure that all software and applications are up-to-date.
Monitoring system activity is crucial to detecting and preventing malware attacks. Use system monitoring tools to track system activity, detect anomalies, and prevent attacks before they occur.
Conclusion
Malware protection for cloud computing security is critical to safeguarding your data and applications. By understanding the types of malware threats in cloud computing, implementing a multi-layered approach, using machine learning and AI, regularly updating and patching systems, and monitoring system activity, you can reduce the risk of malware attacks and ensure the security and reliability of your cloud-based systems. Remember, a robust malware protection strategy is essential to protecting your organization's online assets and preventing cyber threats.










![Free Cybersecurity Courses & Certificates [2026] | Coursera View of Free Cybersecurity Courses & Certificates [2026] | Coursera](https://images.ctfassets.net/5natoedl294r/3Bi1Gco22NtX2DuE64LoE7/440772e67fc1f021550aadec9dacddbb/Cloud_application_security_threats_1400x1235.png?w=1366&h=1205&q=50&fm=png)