Preventing Ransomware On Server: A Comprehensive Guide
Ransomware attacks have become a significant threat to organizations worldwide, with Windows servers being a common target. Protecting your Windows server from ransomware involves implementing proactive security practices, regular system updates, robust backup solutions, and user education. In this article, we will explore the best practices for preventing ransomware attacks on Windows servers, ensuring that your organization is well-equipped to prevent, detect, and respond to potential attacks.
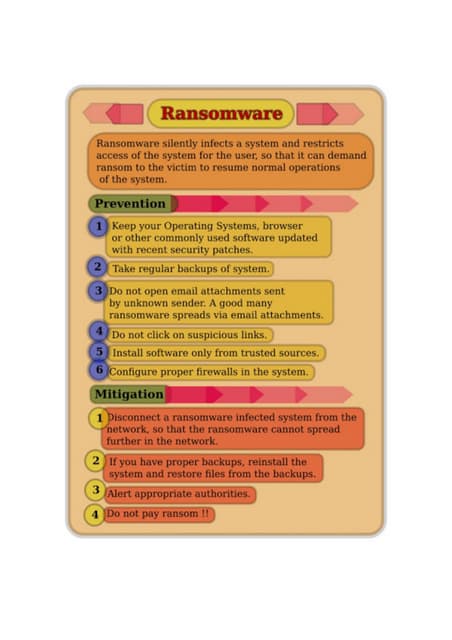
Understanding Ransomware
Such details provide a deeper understanding and appreciation for Preventing Ransomware On Server.
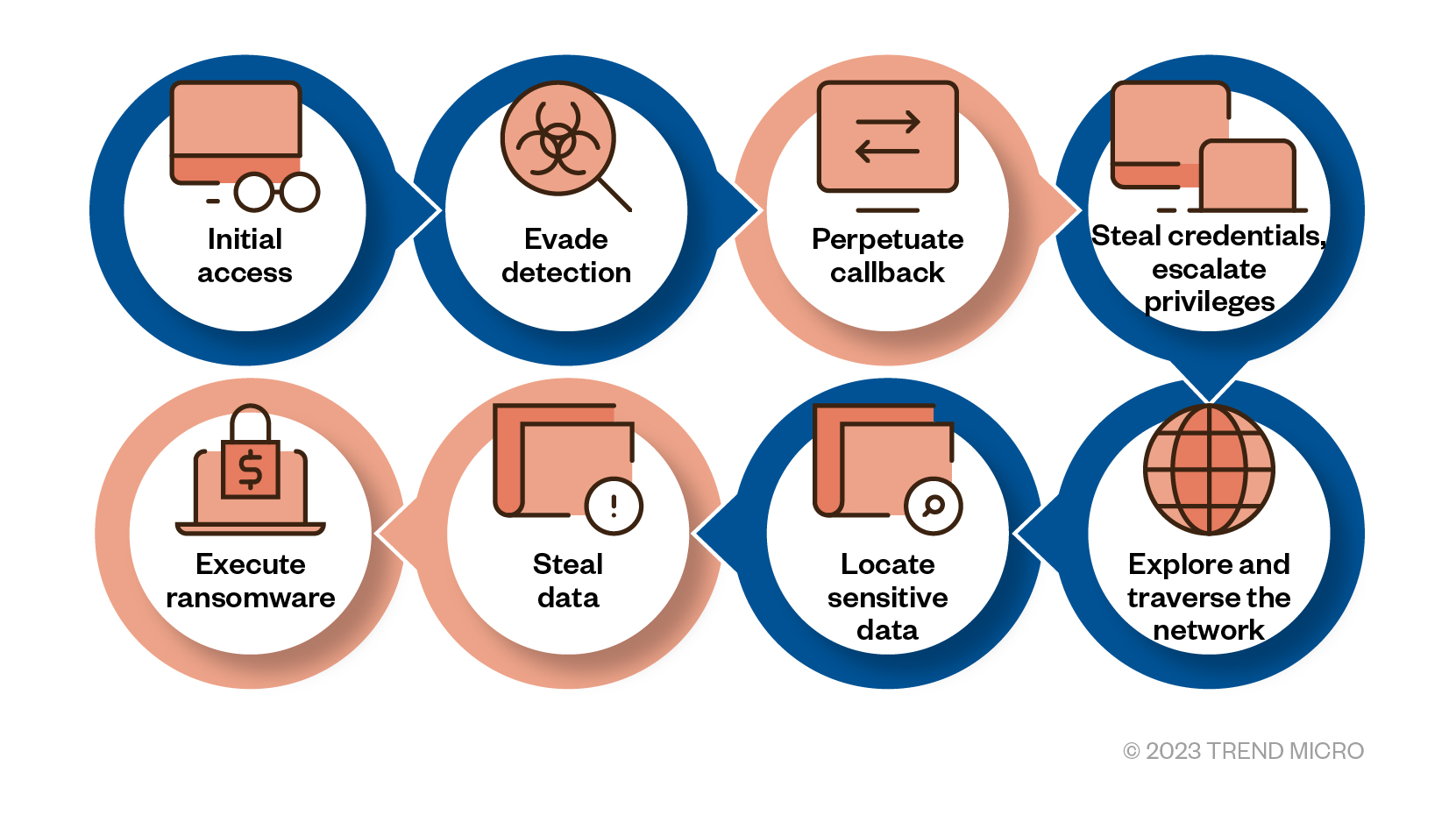
Ransomware is a type of malware that encrypts files on a system or device in an attempt to coerce the victim to pay a ransom. It usually does this by exploiting vulnerabilities in software or operating systems, or through phishing attacks. Once a system is infected, the malware encrypts files, making them unusable, and demands payment in exchange for the decryption key.
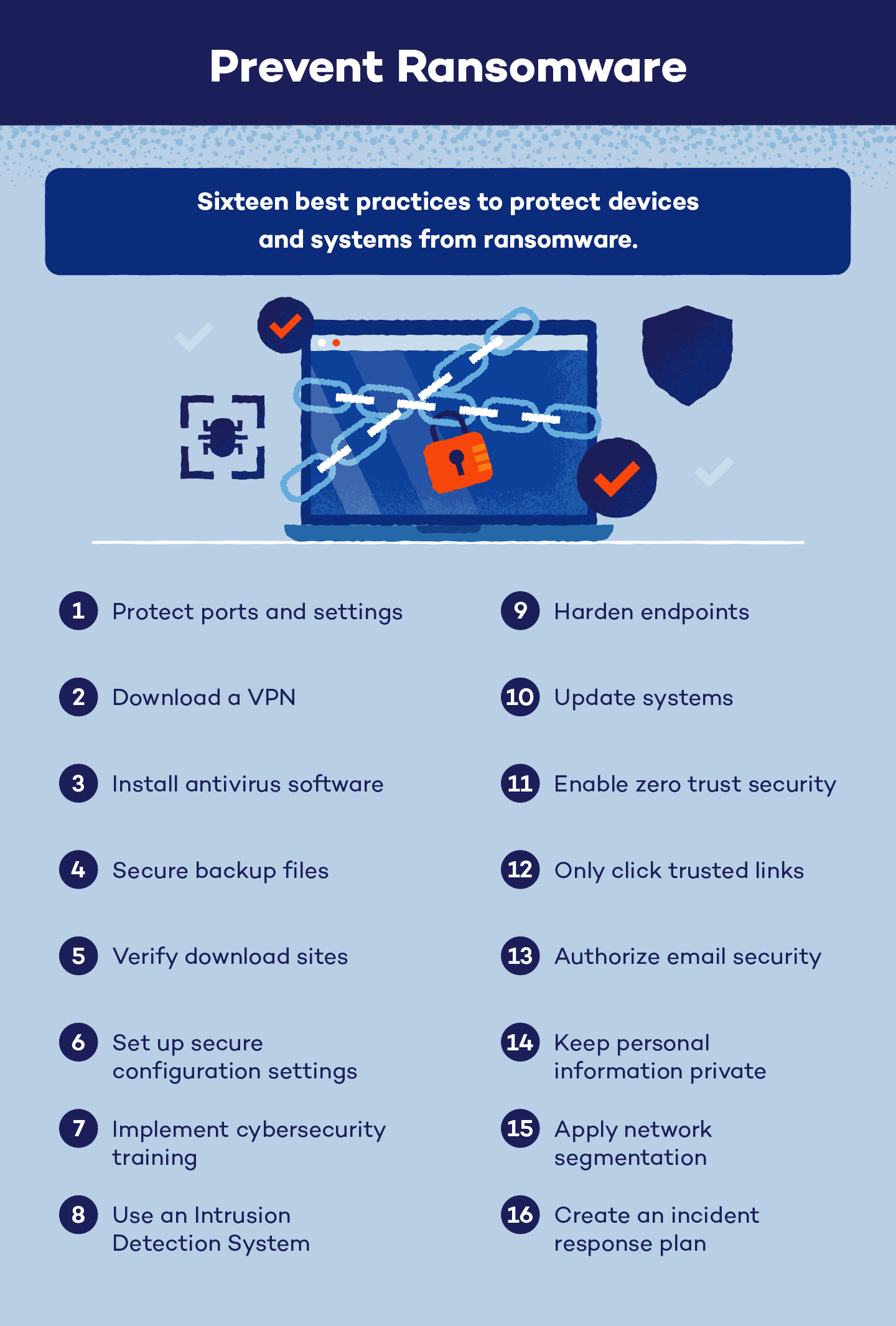
Best Practices for Preventing Ransomware Attacks on Windows Servers
- Regular System Updates and Patches: Ensure that your Windows server is running the latest version of the operating system and apply all available security patches. This will help protect against known vulnerabilities and prevent attackers from exploiting them.
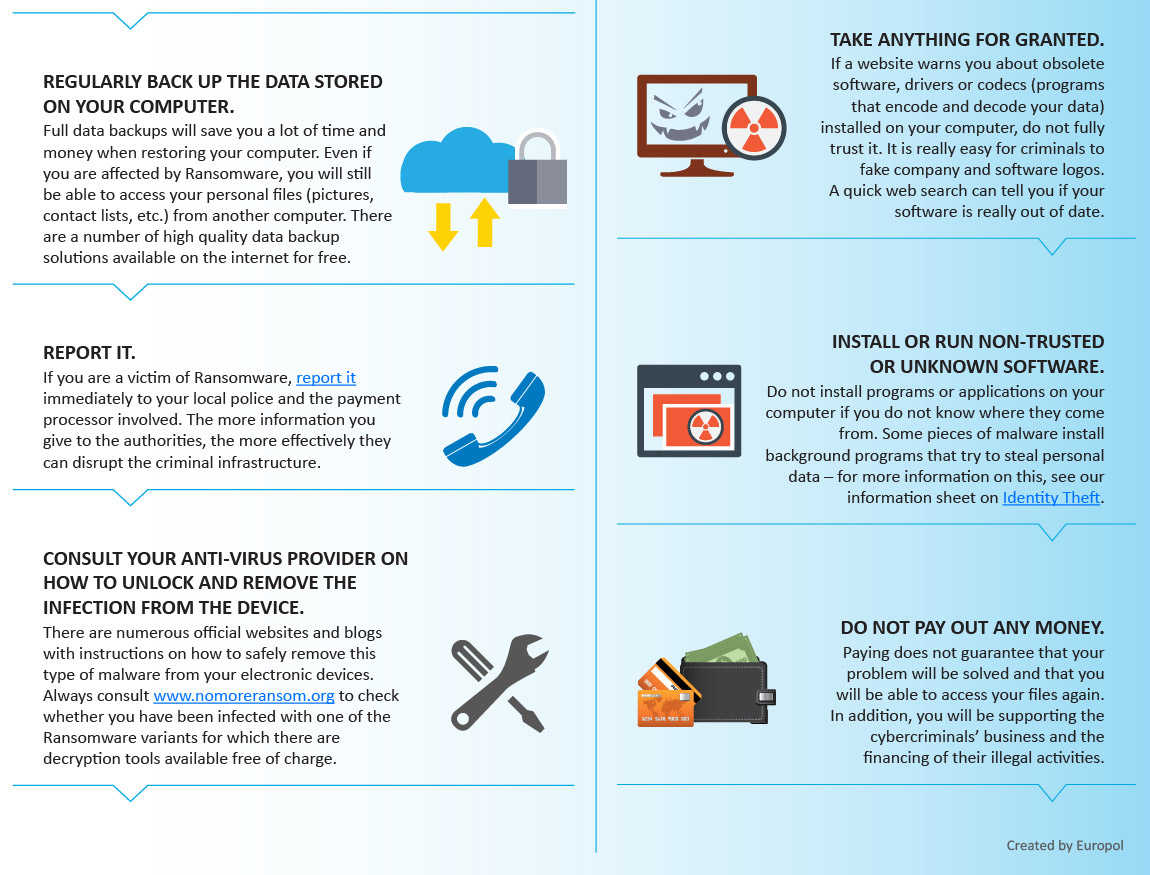
- Robust Backup Solutions: Implement a robust backup solution that includes both full and incremental backups. This will ensure that your data is safe in case of a ransomware attack, and you can restore it quickly without having to pay the ransom.
- User Education: Educate your users about the risks of ransomware and provide them with guidelines on how to avoid falling victim to phishing attacks. This includes avoiding suspicious emails, not clicking on unknown links, and keeping software and operating systems up to date.
- Network Segmentation: Segment your network to limit the spread of ransomware attacks. This includes configuring firewalls, implementing access controls, and segmenting critical systems from the rest of the network.
- Least Privilege Access: Implement least privilege access to ensure that users and applications have the minimum level of access required to perform their tasks. This will limit the damage caused by a ransomware attack and make it easier to detect and respond to threats.
- Continuous Monitoring: Implement continuous monitoring to detect and respond to ransomware attacks quickly. This includes configuring security information and event management (SIEM) systems, implementing threat intelligence feeds, and performing regular security audits.
- Secure Configuration: Ensure that your Windows server is configured securely, including disabling unnecessary services, configuring firewall rules, and implementing access controls.
- Incident Response Plan: Develop and implement an incident response plan to respond quickly and effectively in case of a ransomware attack. This includes identifying key stakeholders, establishing communication channels, and defining roles and responsibilities.
- Backup and Recovery Plan: Develop and implement a backup and recovery plan to ensure that your data is safe and can be restored quickly in case of a disaster.
Conclusion
By following these guidelines, you can protect your Windows server from ransomware and ensure the availability and integrity of your data.