IDP and Event Logs Management: Understanding the Importance and Best Practices
Introduction
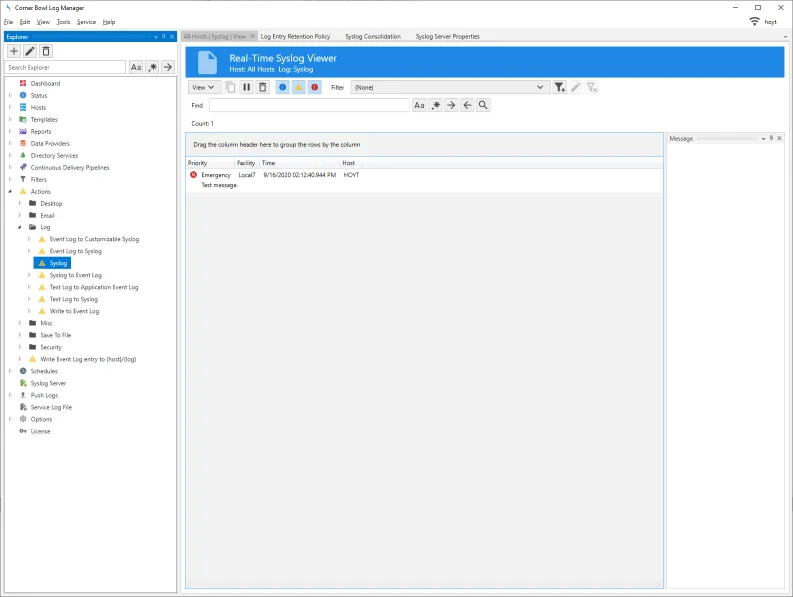
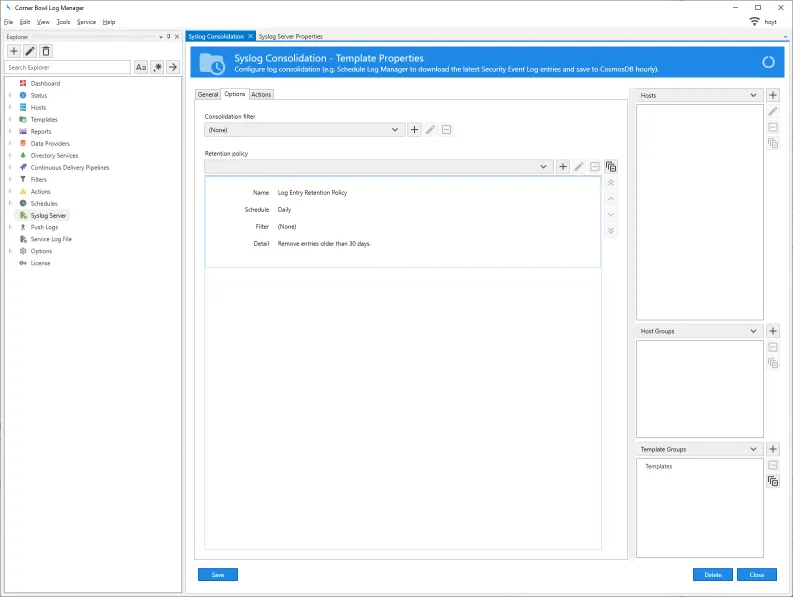
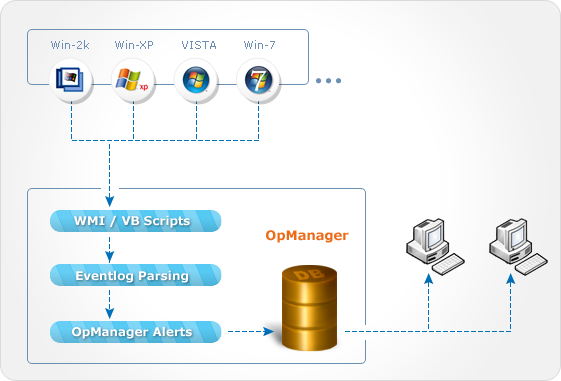
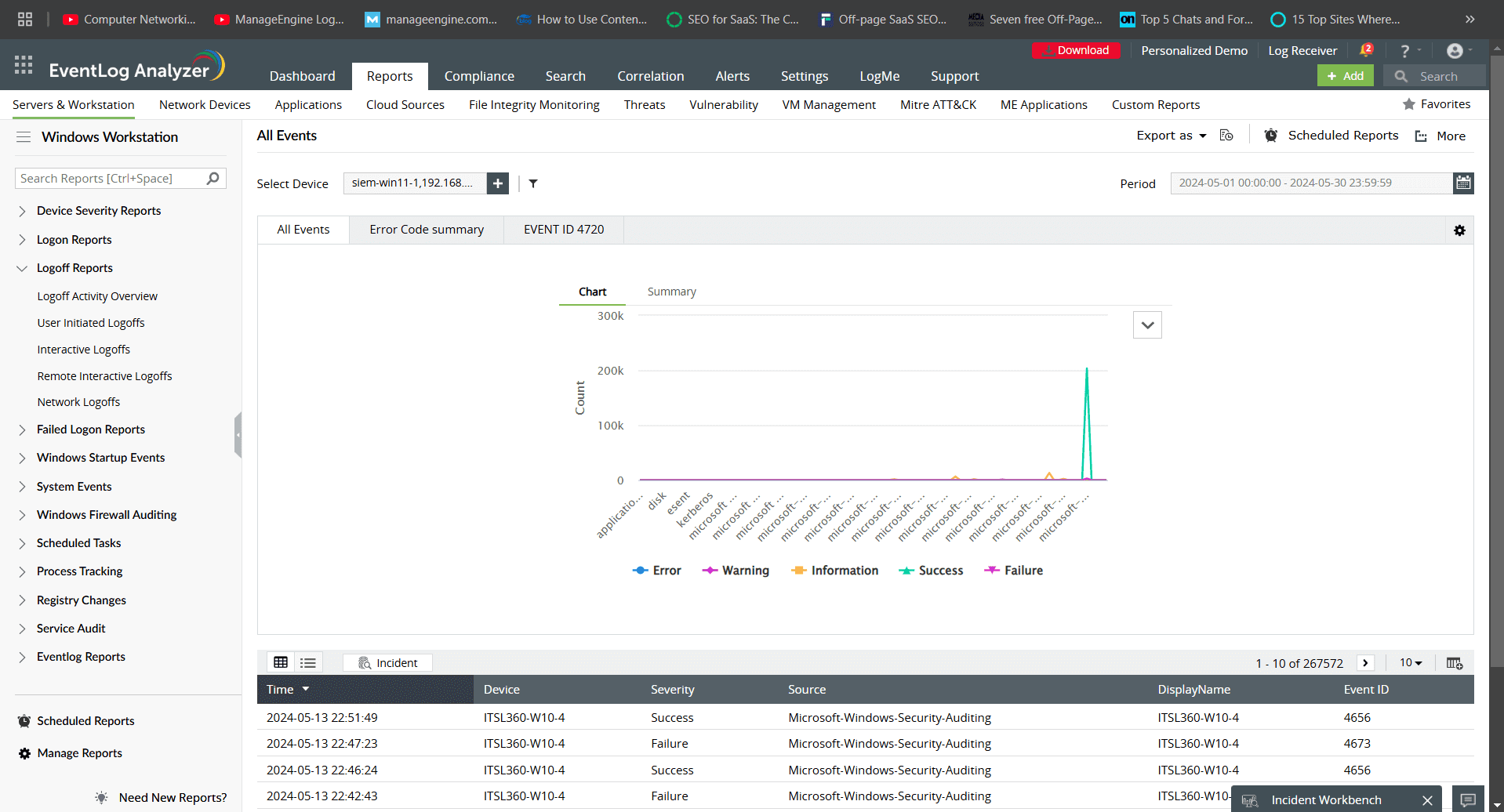
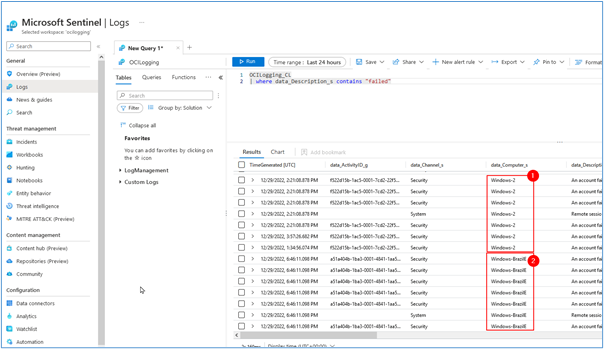
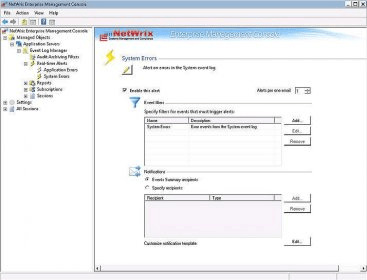
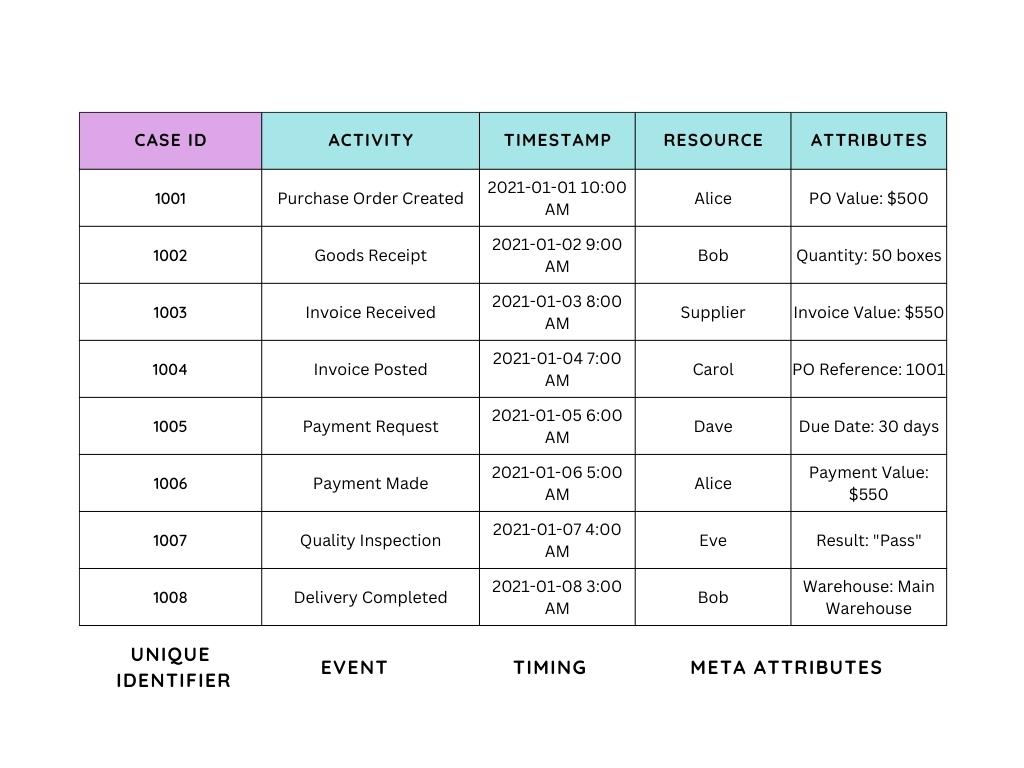
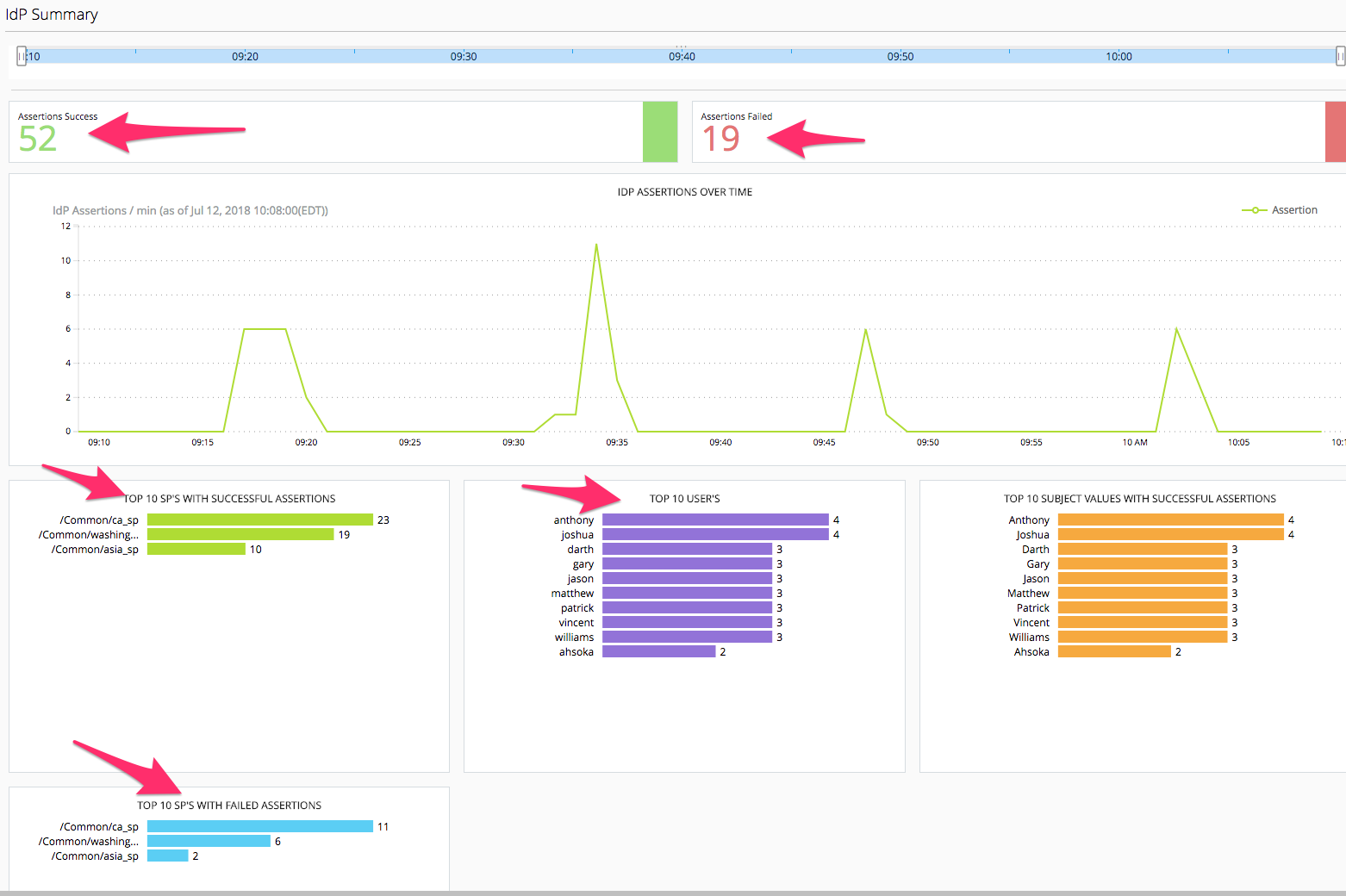
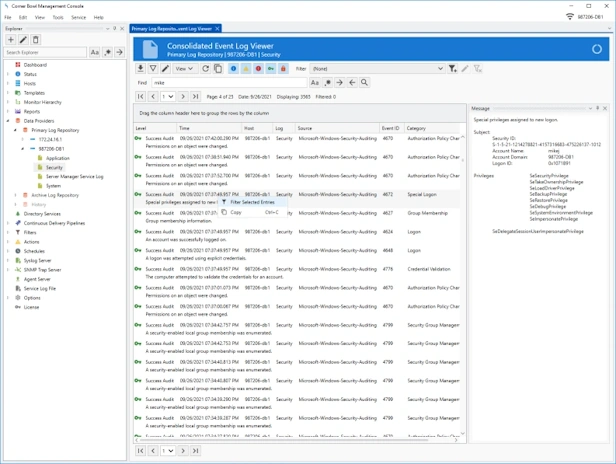
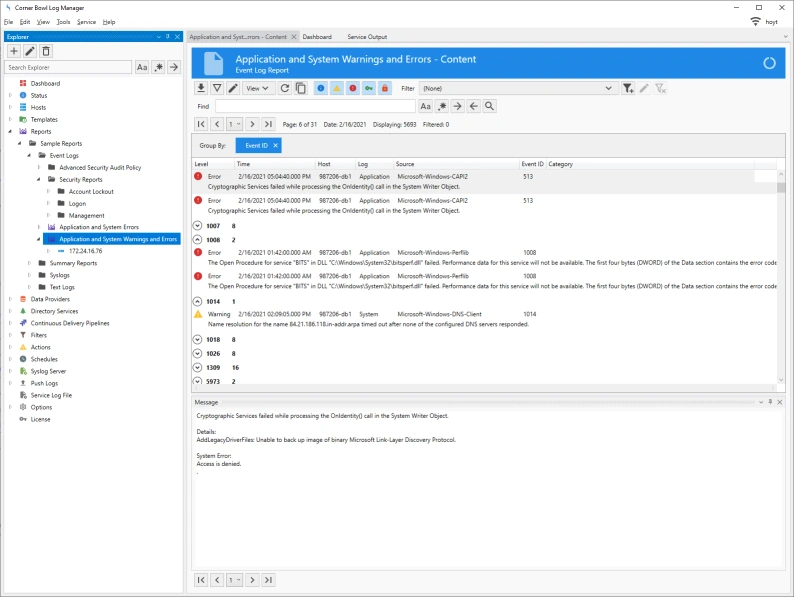
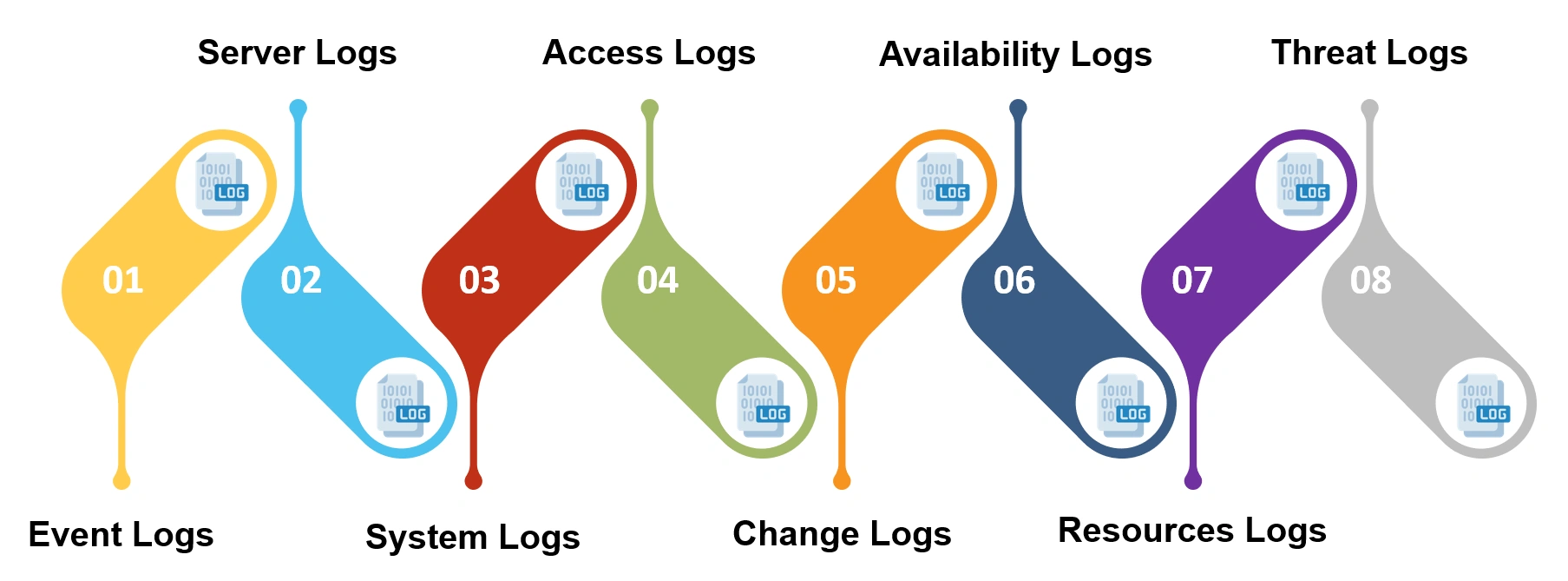
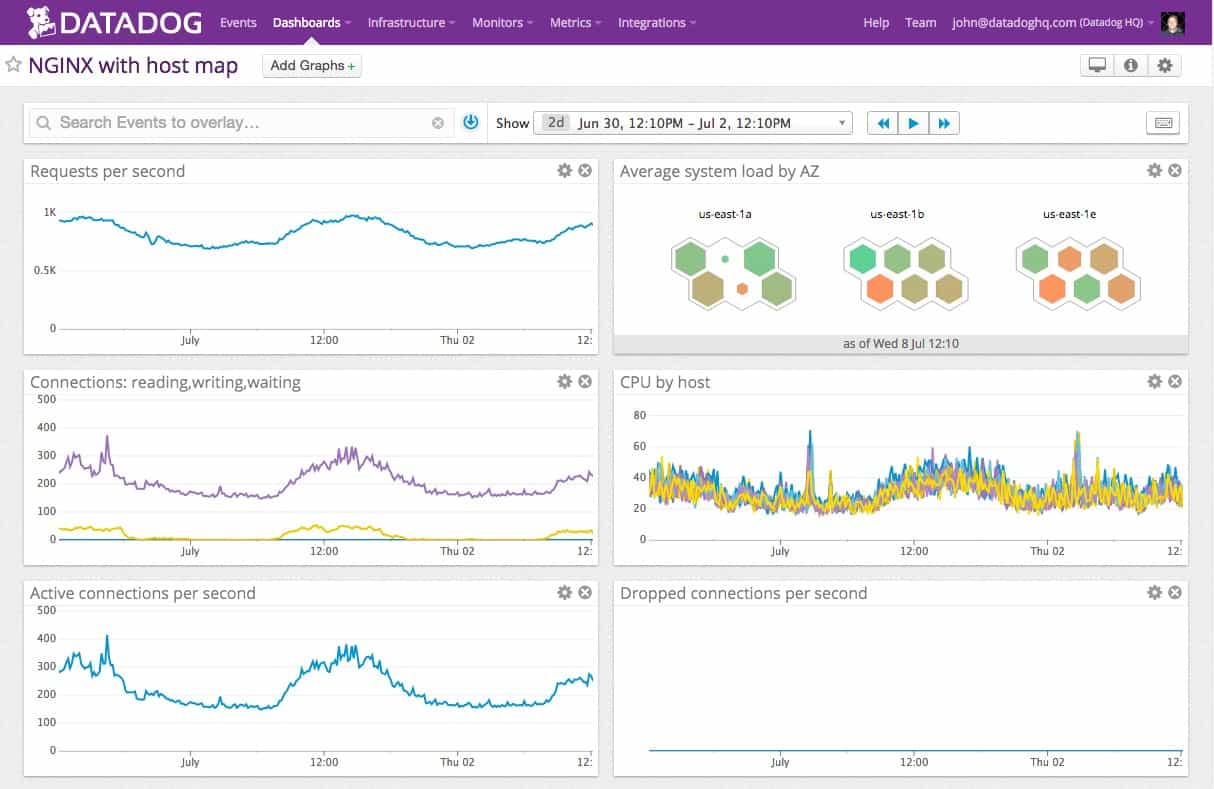
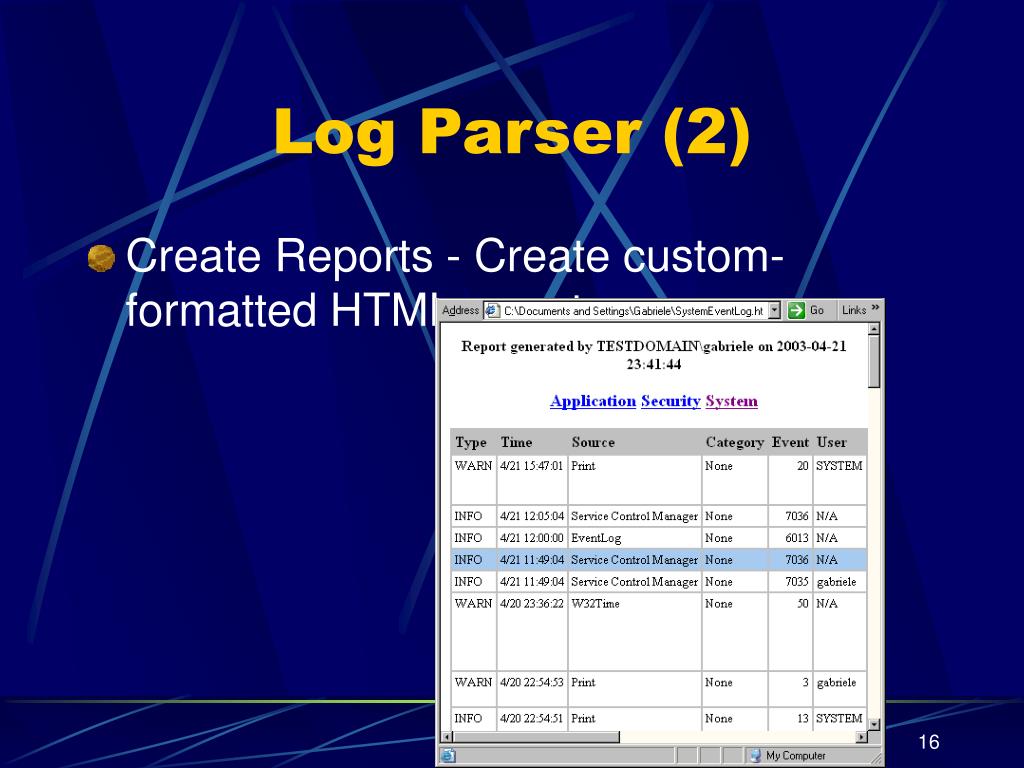
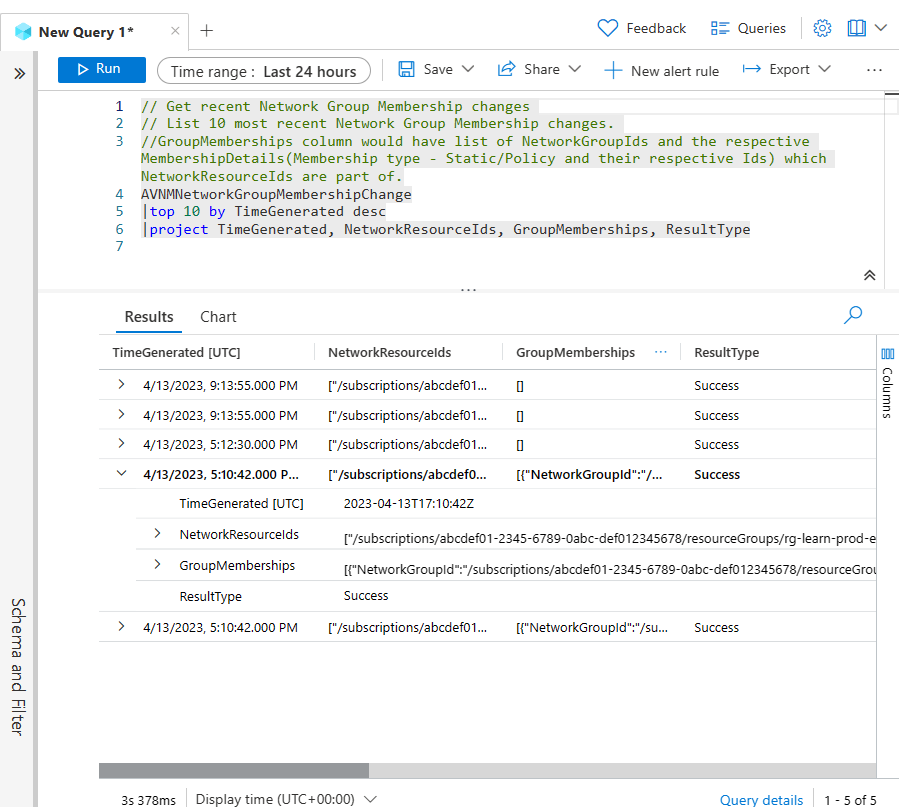
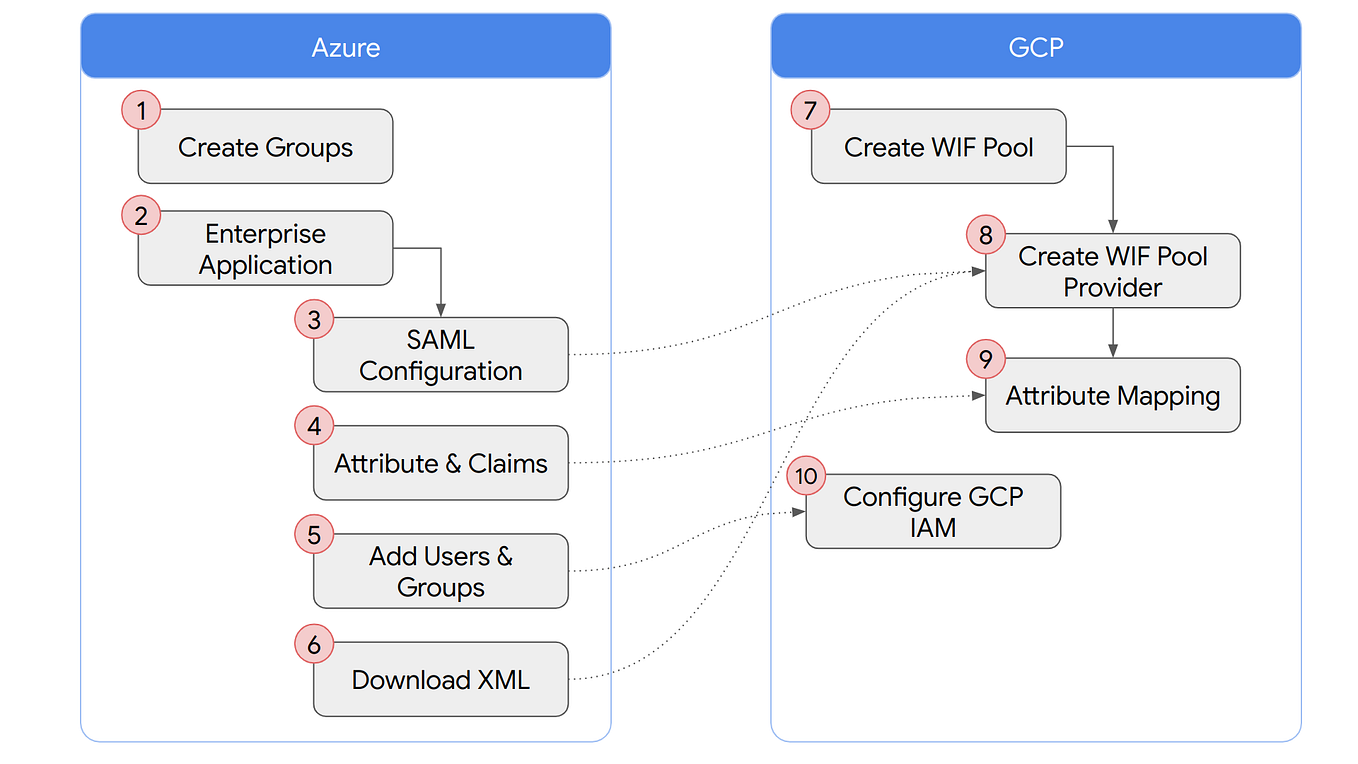
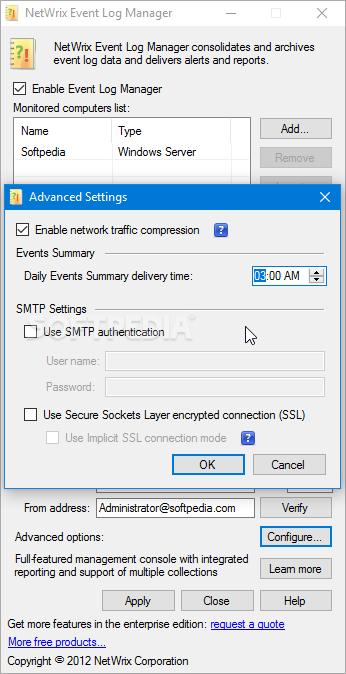
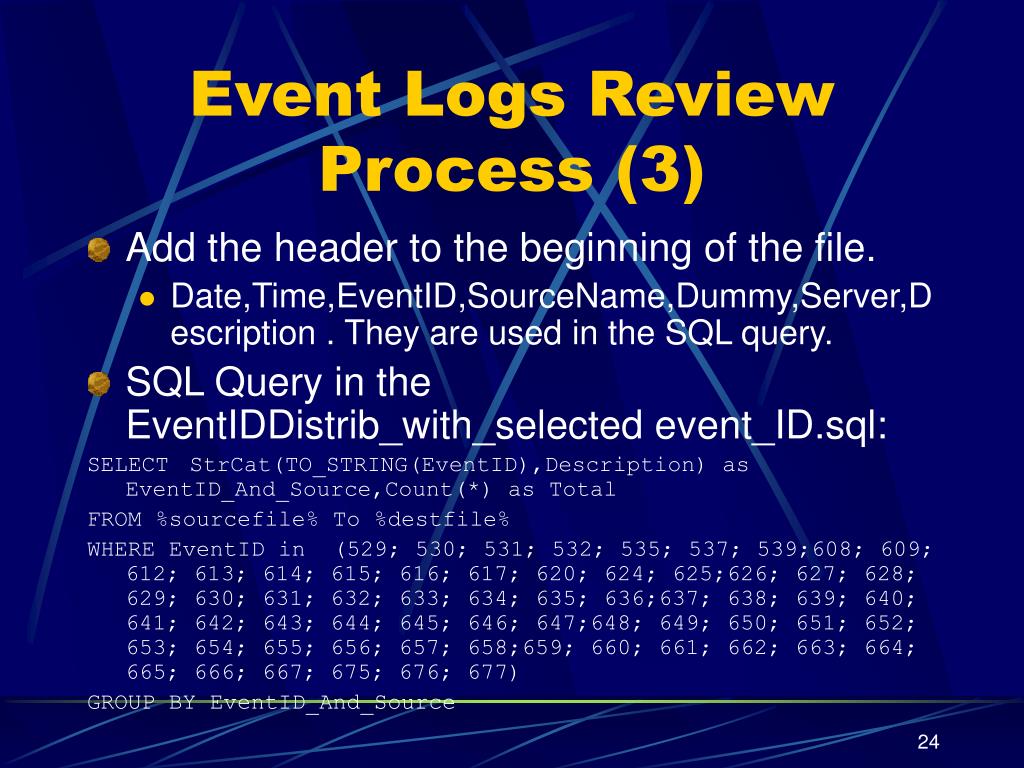
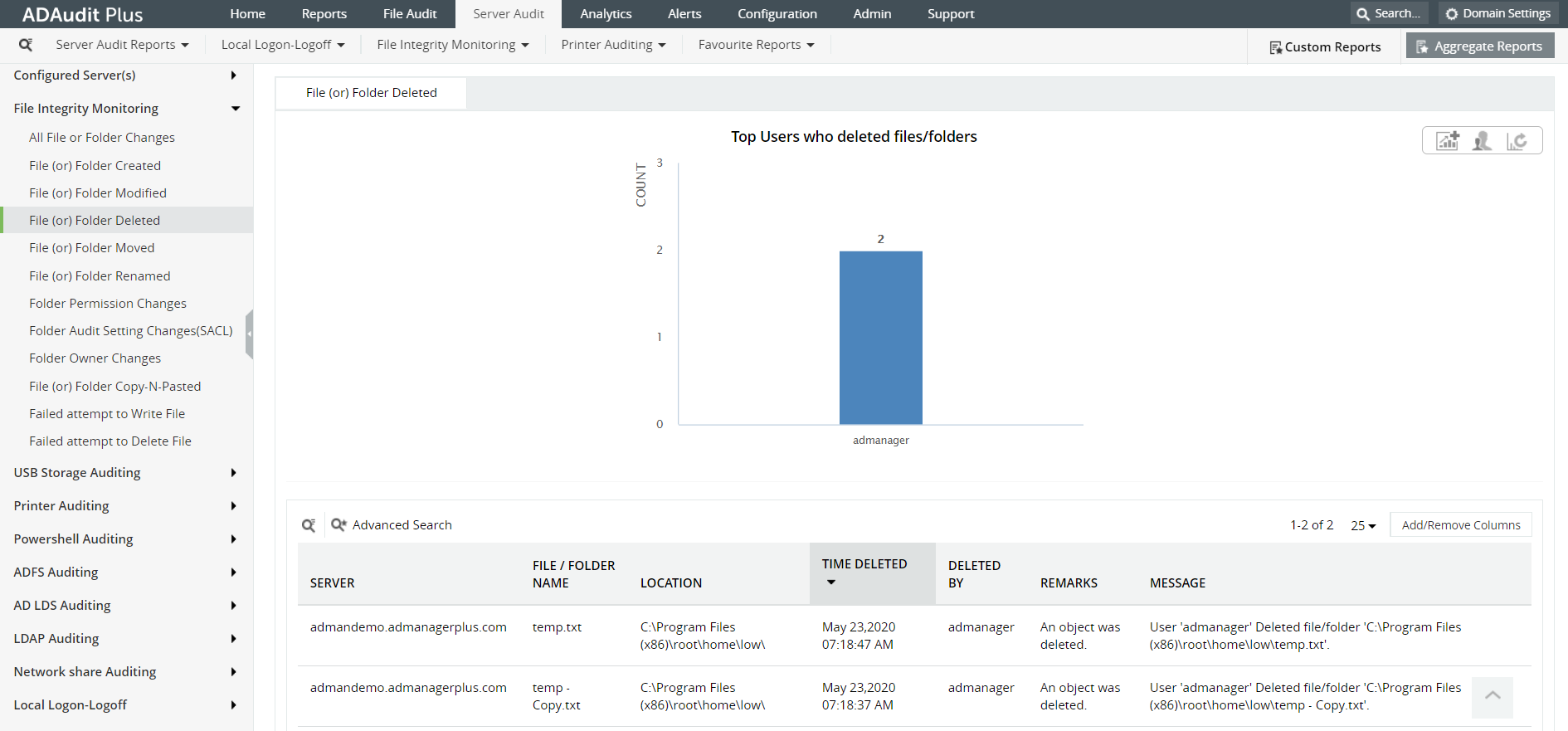
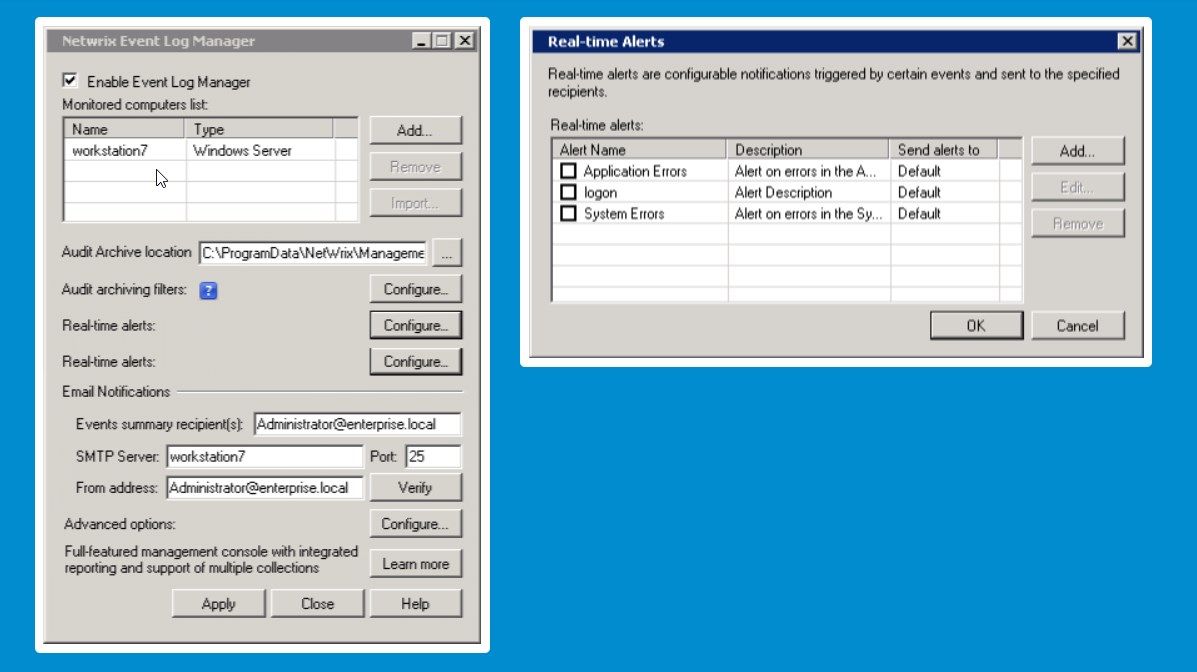
As we can see from the illustration, Idp And Event Logs Management has many fascinating aspects to explore.
In today's digital landscape, organizations are increasingly relying on identity providers (IdPs) to securely manage user identities and access to various applications and services. However, with the rise of cybersecurity threats, it's essential to have a comprehensive understanding of IDP and event logs management to ensure that security posture is maintained. In this article, we will explore the importance of IDP and event logs management and discuss the best practices for implementing this critical security measure.The Role of IDP in Event Logs Management
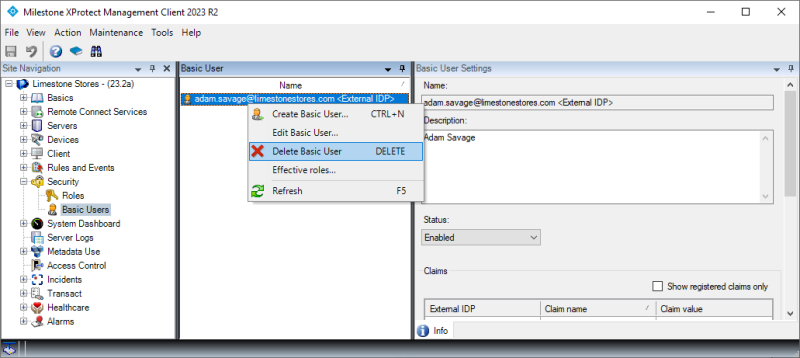
As we can see from the illustration, Idp And Event Logs Management has many fascinating aspects to explore.
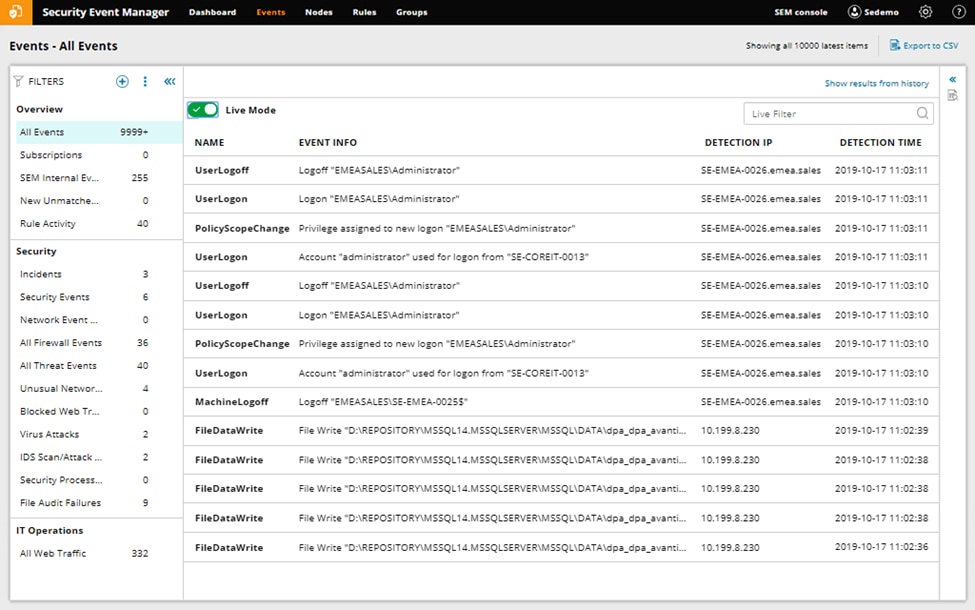
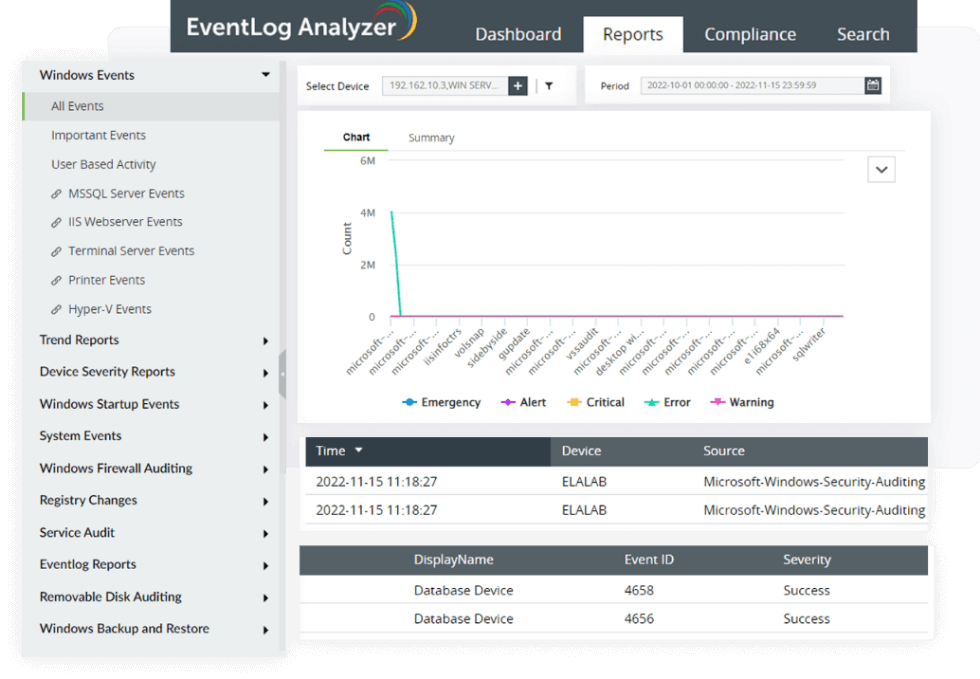
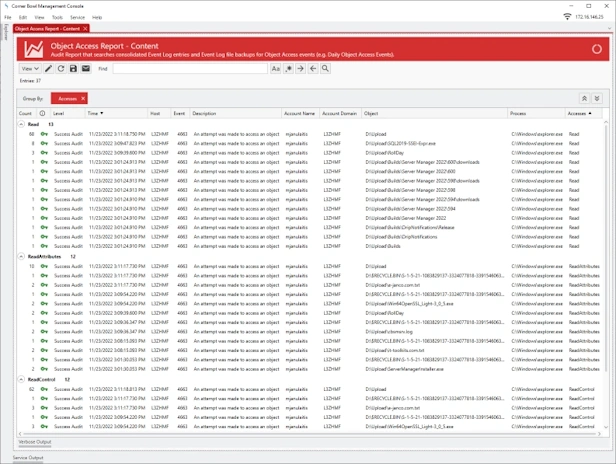
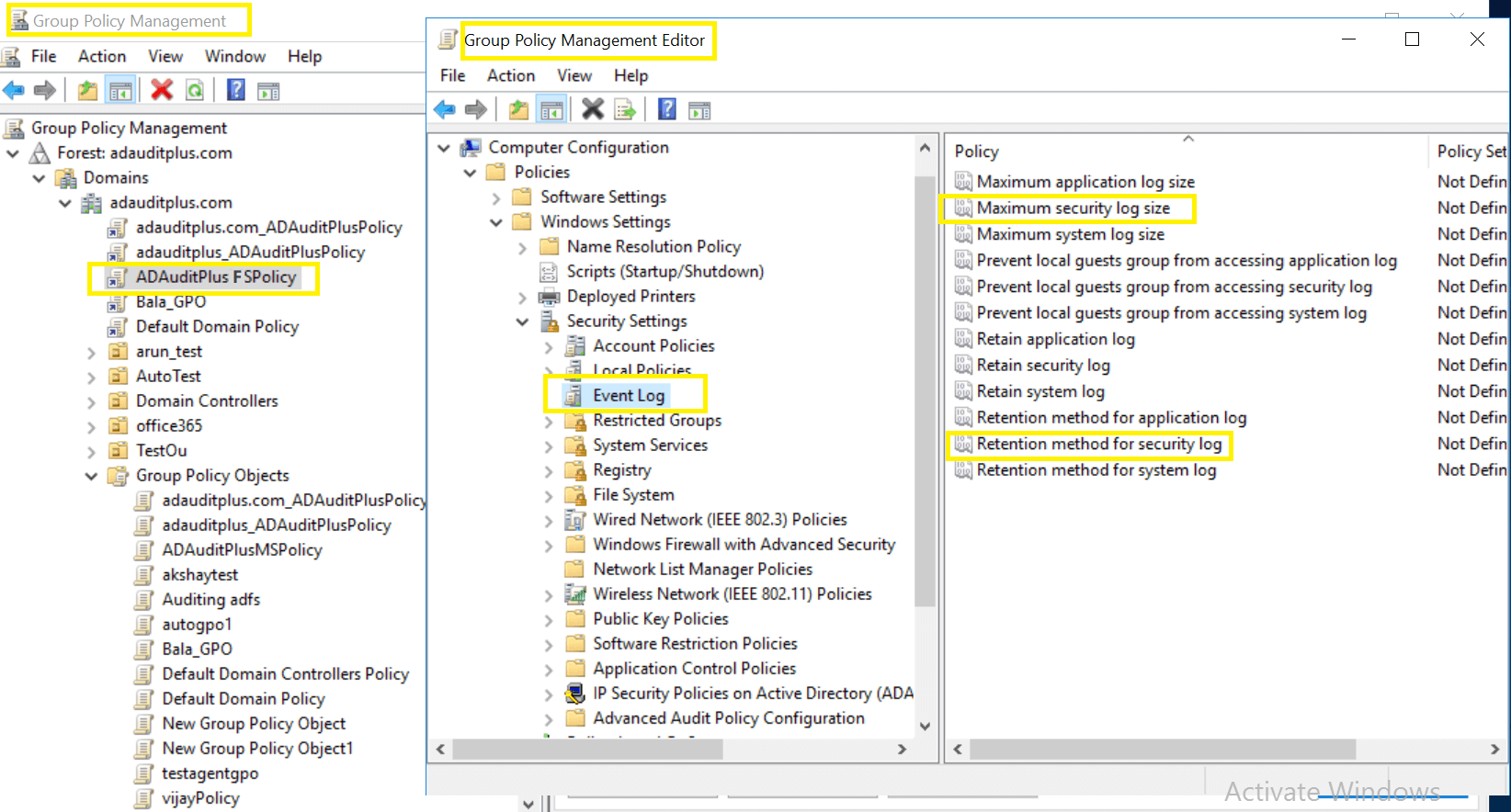
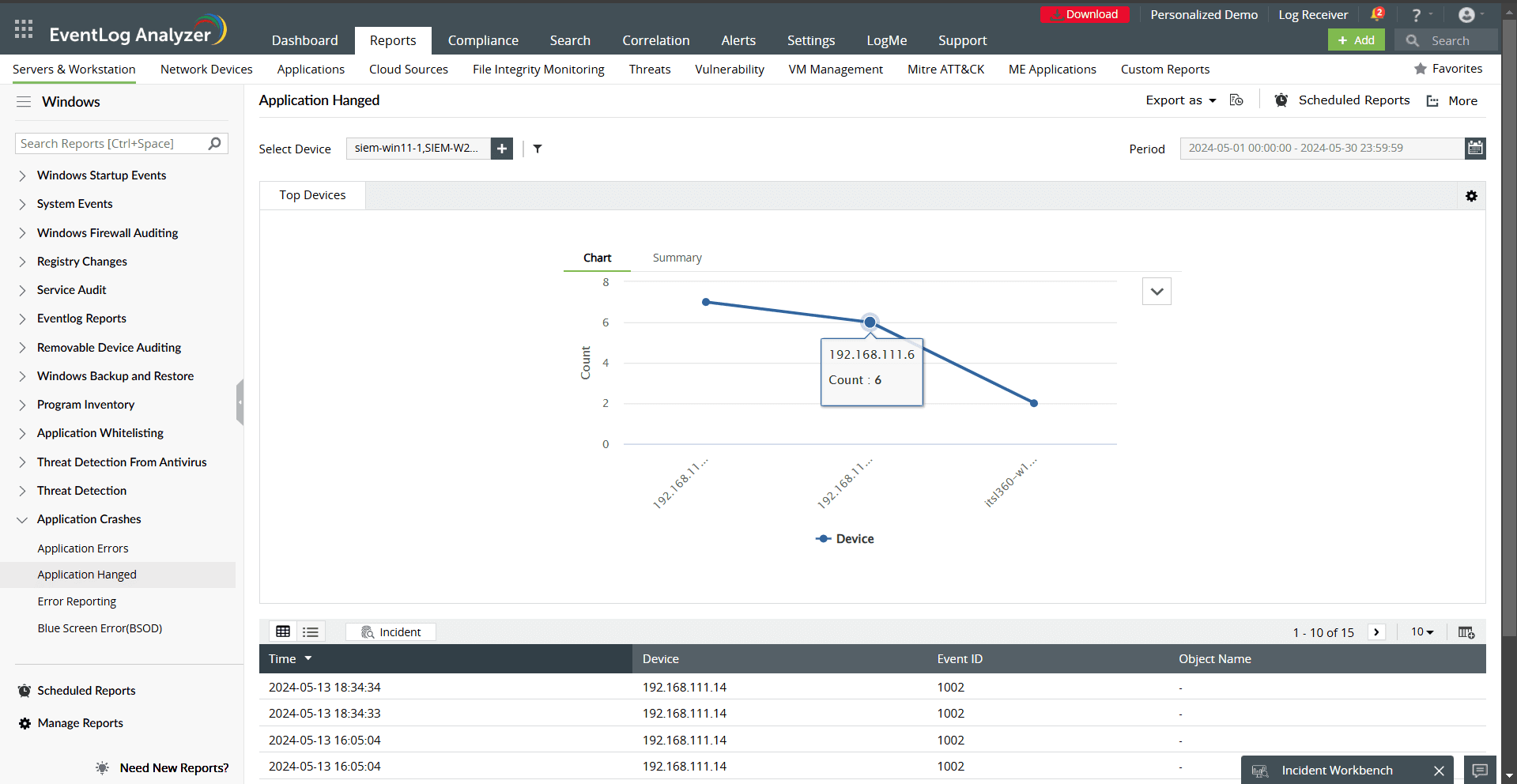
An IDP plays a vital role in managing user identities and ensuring secure access to applications and services. To enable this, an IDP needs to track various events and logs, such as login attempts, access attempts, and system configuration changes. Event logs are records of security-related activities captured by systems, applications, and devices, providing valuable insights into potential security threats. Implementing an IDP and managing event logs offers numerous benefits, including: * **Improved security posture**: Monitoring and analyzing event logs help identify potential security threats and anomalies, enabling organizations to take proactive measures to prevent unauthorized access and data breaches. * **Compliance and regulatory adherence**: Centralized event logging and analysis help organizations comply with various regulatory requirements, such as GDPR, HIPAA, and PCI-DSS. * **Enhanced threat detection and response**: Advanced threat detection and response capabilities enable organizations to quickly identify and respond to security threats, minimizing the impact of cyber attacks.