How to Protect Data from Insider Threats: A Comprehensive Guide
Insider threats are a growing concern for organizations, and with the increasing amount of sensitive data being stored and shared, it's essential to have effective strategies in place to protect against these types of threats. In this article, we'll explore the different types of insider threats, their impact on organizations, and provide actionable tips on how to protect data from insider threats.
Insider threats refer to risks posed by individuals who have legitimate access to systems, data, or networks. These insiders may act maliciously, such as stealing intellectual property or selling confidential data to competitors. They may also act negligently, such as misconfiguring a database, falling for phishing attacks, or sharing sensitive data with unauthorized parties.
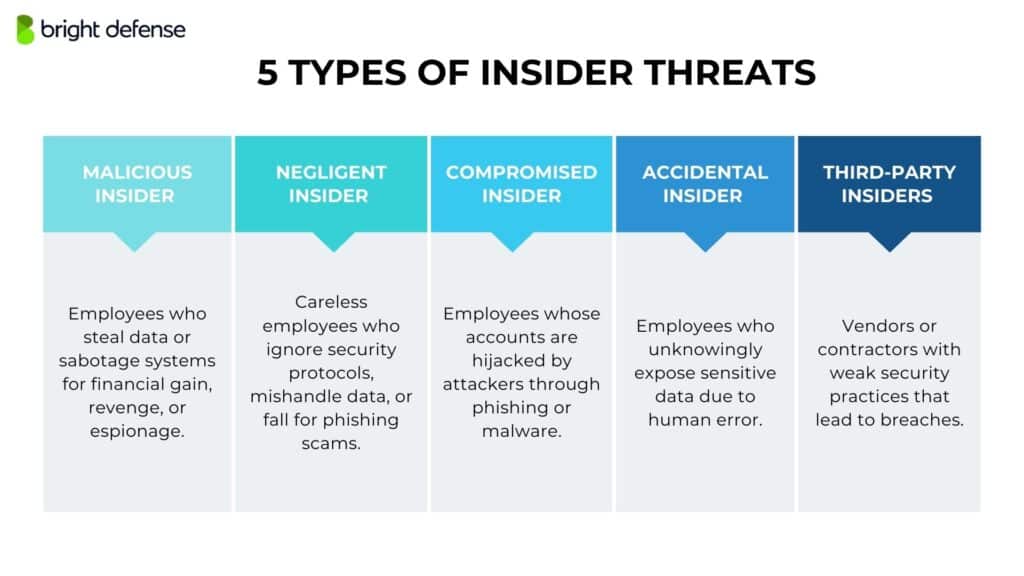
Types of Insider Threats
There are several types of insider threats, including:
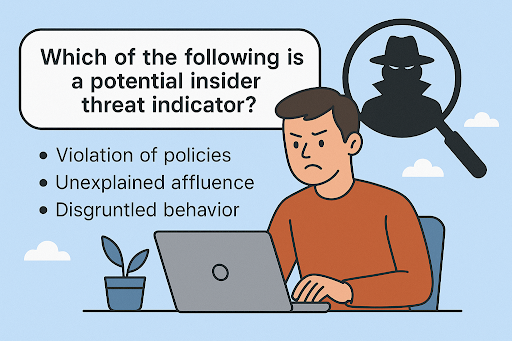
- Malicious insiders: These are individuals who intentionally attempt to harm the organization by stealing data, disrupting operations, or compromising security.
- Negligent insiders: These are individuals who inadvertently compromise security due to a lack of knowledge, training, or oversight.
- Compromised insiders: These are individuals who have been compromised by external threats, such as phishing or malware, and are used as a means to gain access to sensitive data.
The Impact of Insider Threats
Insider threats can have devastating consequences for organizations, including financial loss, reputational damage, and regulatory non-compliance. According to a report by the Ponemon Institute, the average cost of a data breach caused by an insider is $7.8 million.
How to Protect Data from Insider Threats
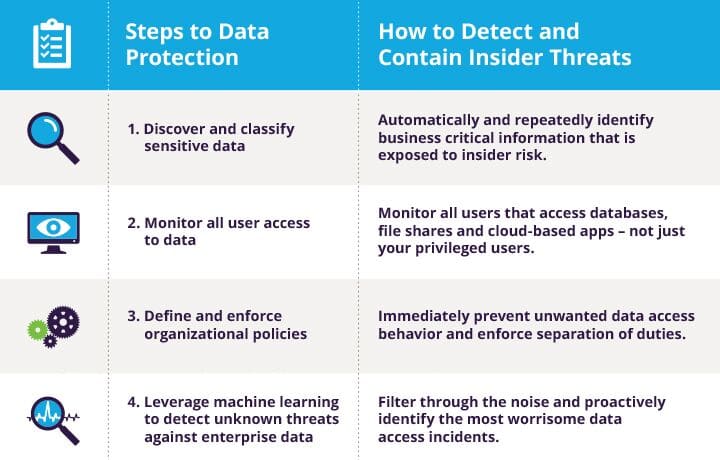
To protect data from insider threats, organizations should implement a combination of technical, procedural, and administrative controls. Here are some actionable tips:
1. Implement Role-Based Access Control
2. Conduct Regular Security Training
Provide regular security training to employees to educate them on security best practices, phishing attacks, and other insider threats. This can help prevent negligent insider threats.

3. Use Data Loss Prevention (DLP) Tools
Use DLP tools to monitor and control sensitive data across the organization. This can help prevent data breaches and insider threats.
4. Implement Insider Threat Detection and Response
Implement insider threat detection and response capabilities to identify and respond to potential insider threats. This can help prevent and mitigate the impact of insider threats.
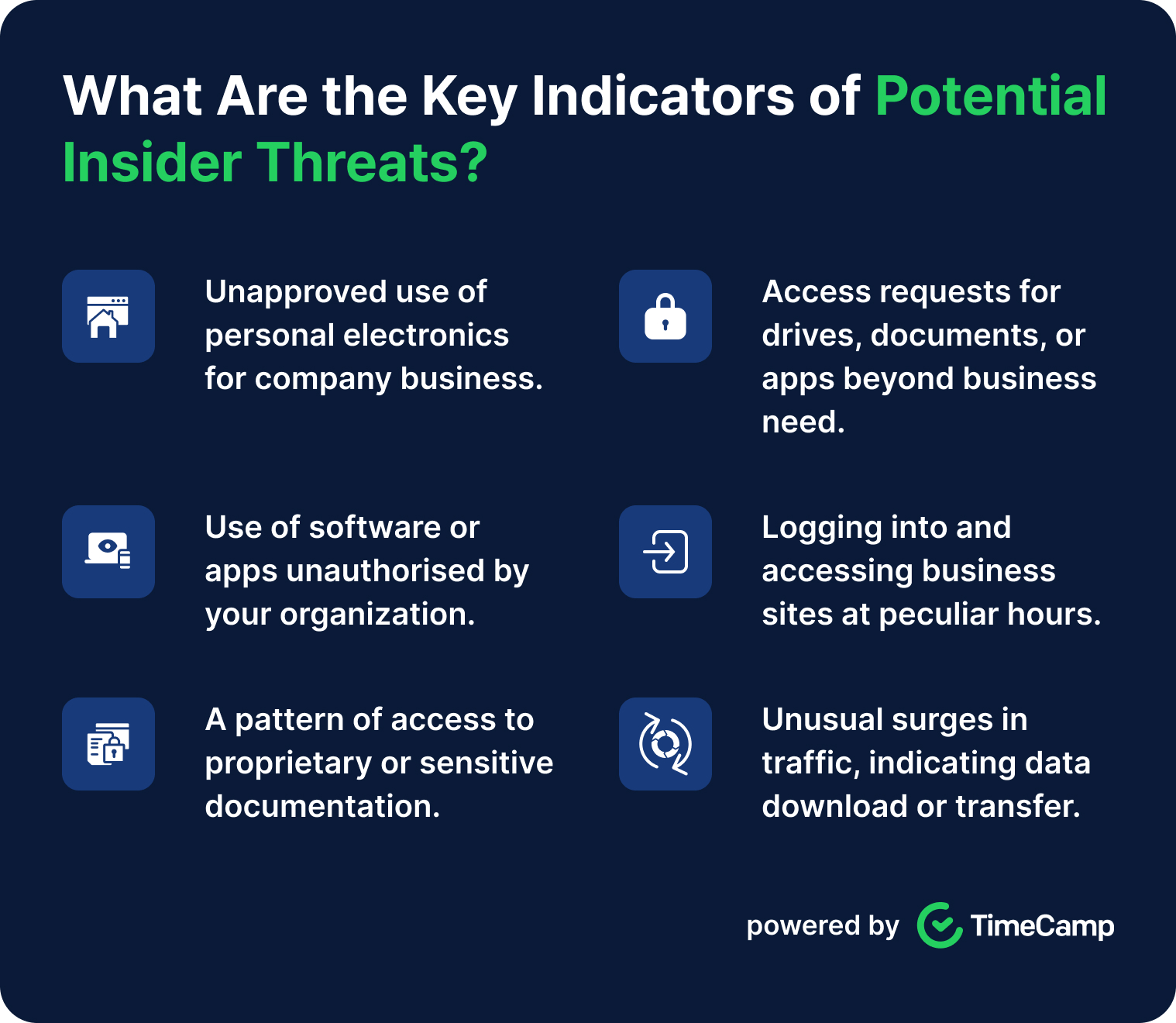
5. Monitor and Analyze User Behavior
Monitor and analyze user behavior to identify potential insider threats. This can help prevent and detect insider threats.

6. Conduct Regular Security Audits
Conduct regular security audits to identify and address security vulnerabilities and weaknesses.
Conclusion
Insider threats are a growing concern for organizations, and it's essential to have effective strategies in place to protect against these types of threats. By implementing a combination of technical, procedural, and administrative controls, organizations can reduce the risk of insider threats and protect sensitive data.
Additional Resources
For more information on protecting data from insider threats, check out the following resources:
- The Insider Threat Report 2019
- Data Loss Prevention (DLP) tools
- Insider threat detection and response capabilities
- Security training and awareness programs











![How to Identify & Monitor Insider Threat Indicators [A Guide] Picture of How to Identify & Monitor Insider Threat Indicators [A Guide]](https://www.slidegeeks.com/media/catalog/product/cache/1280x720/P/r/Process_Flow_For_Detecting_Insider_Threat_In_Cyber_Security_Mockup_PDF_Slide_1_1.jpg)