G Router Firewall Configuration: A Comprehensive Guide
The G router firewall configuration is a crucial aspect of maintaining a secure and stable network. In this article, we will delve into the world of G router firewall configuration, exploring its importance, benefits, and steps to configure it effectively.
Why Configure G Router Firewall?
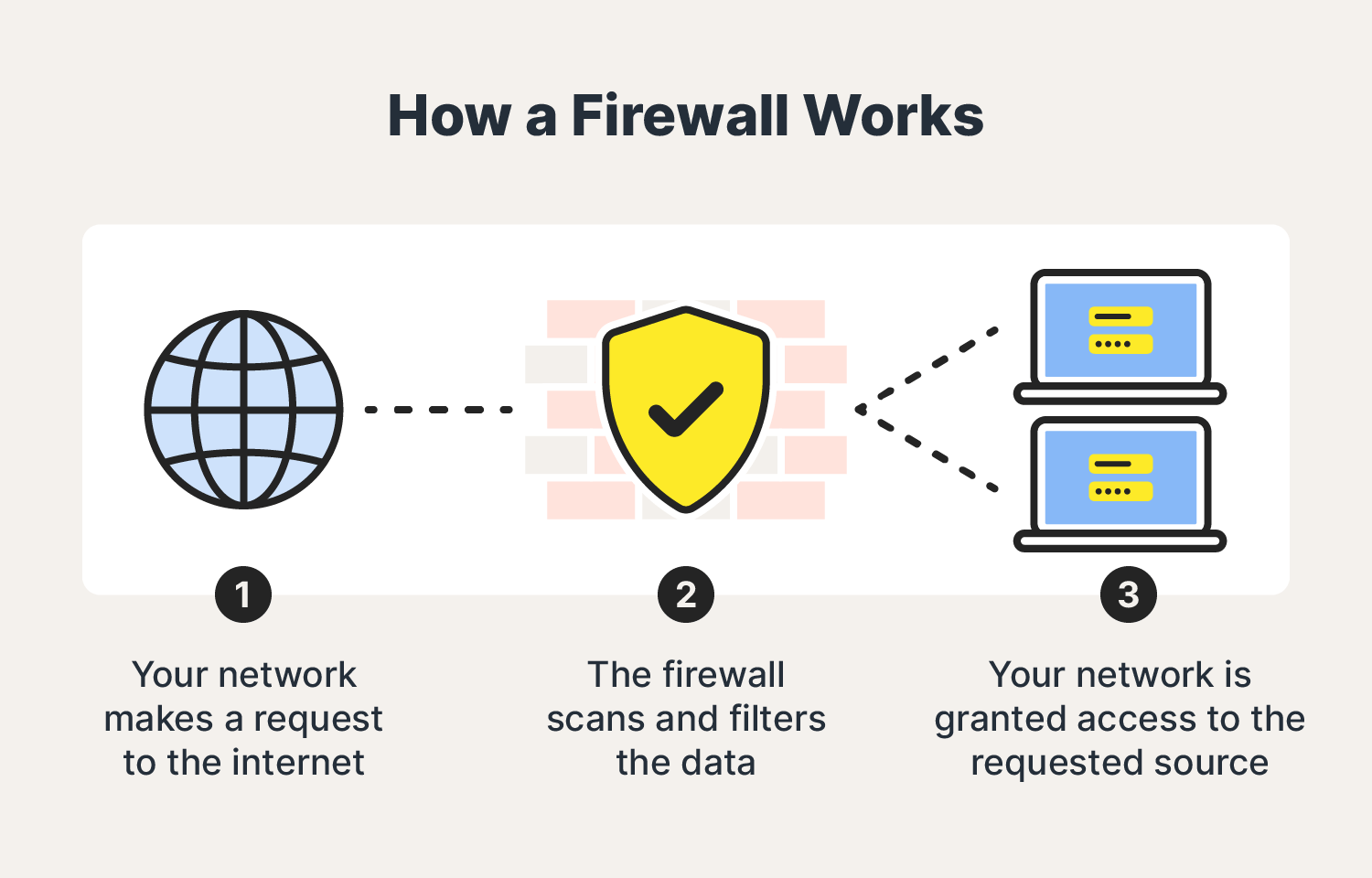
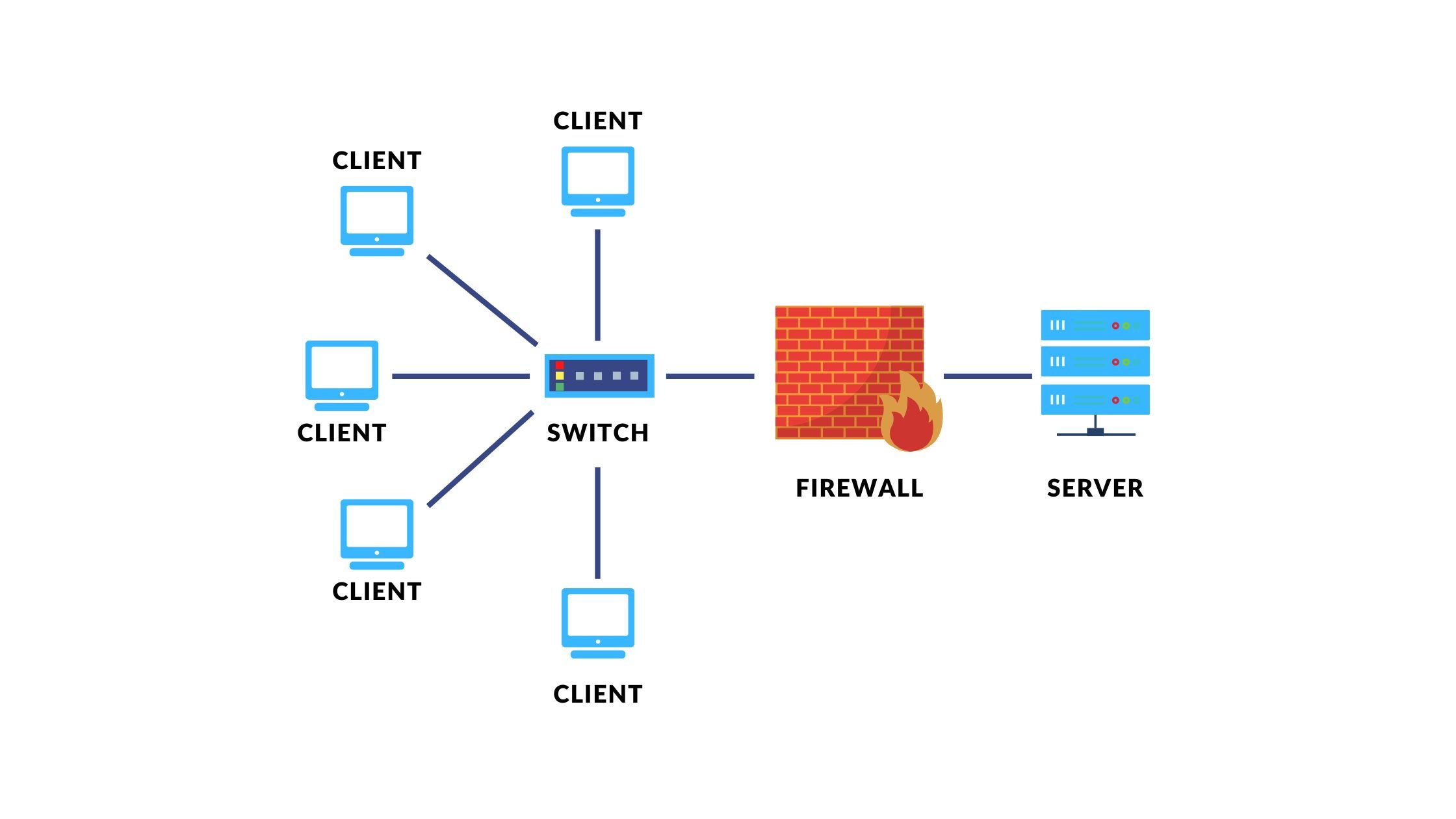
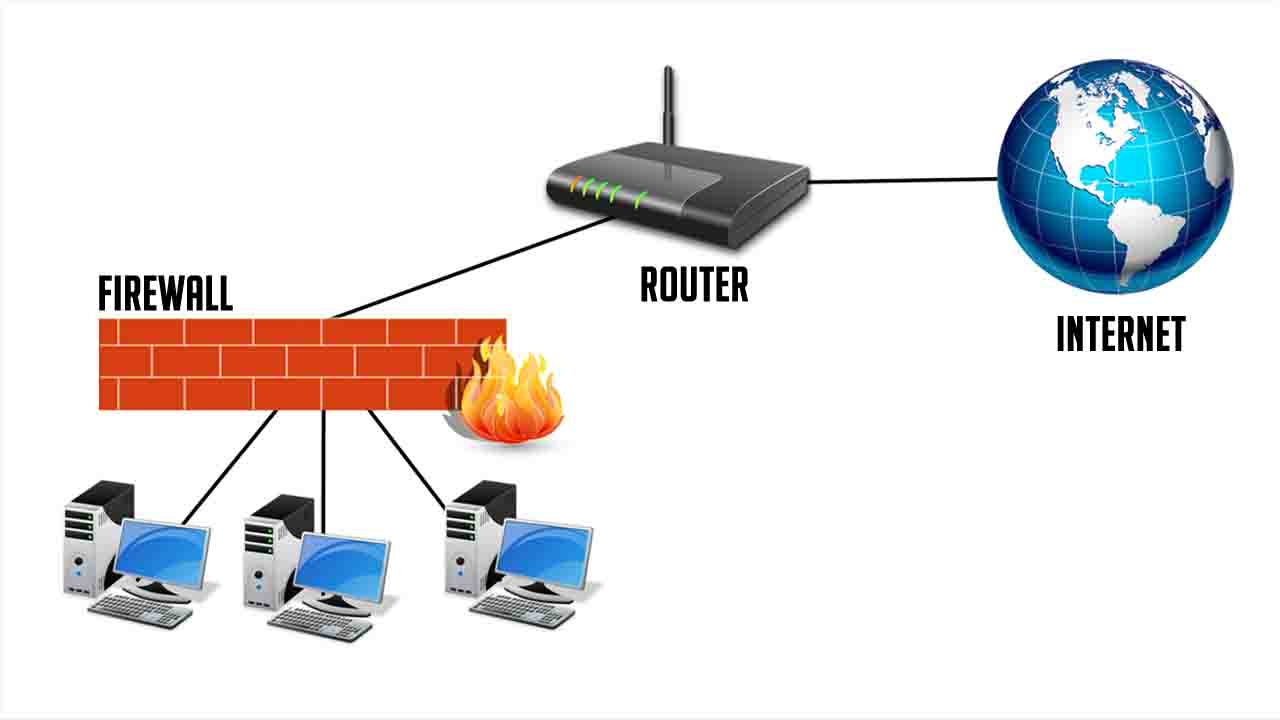
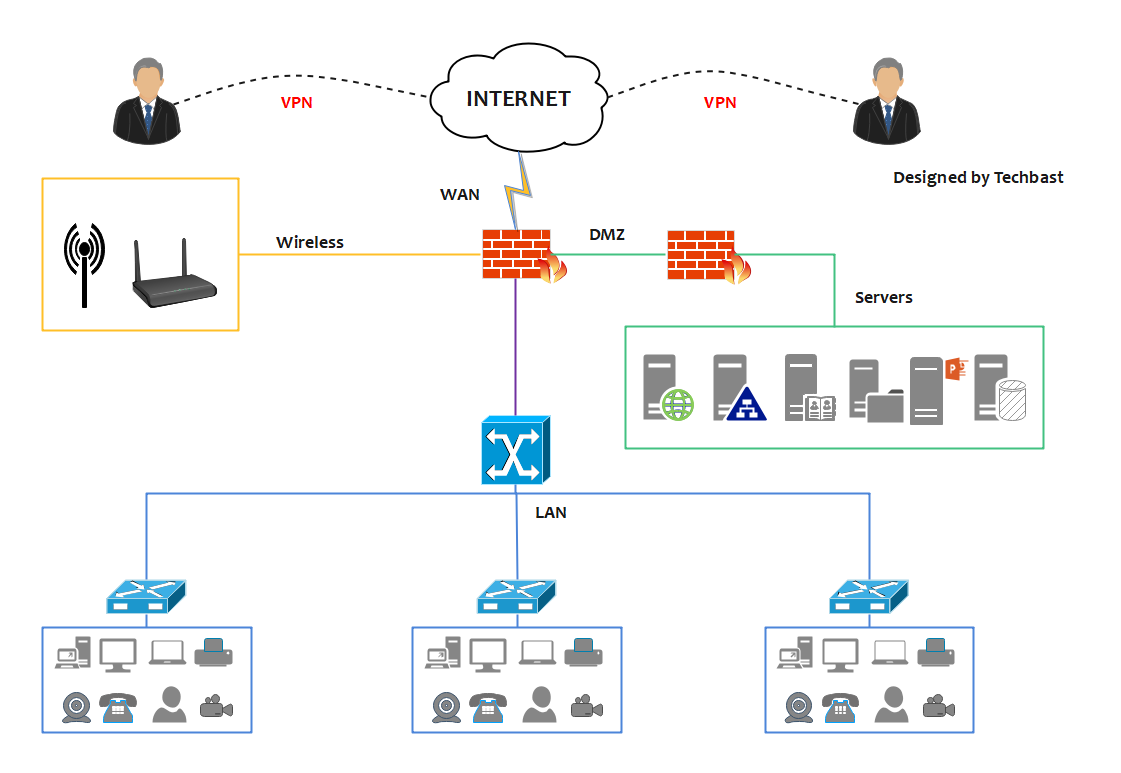
The G router firewall is a built-in security feature that helps protect your network from external threats, such as hackers and malware. By configuring the firewall, you can control incoming and outgoing traffic, ensuring that only authorized devices and applications can access your network. This not only enhances network security but also improves overall performance and reliability.

Moving forward, it's essential to keep these visual contexts in mind when discussing G Router Firewall Configuration.
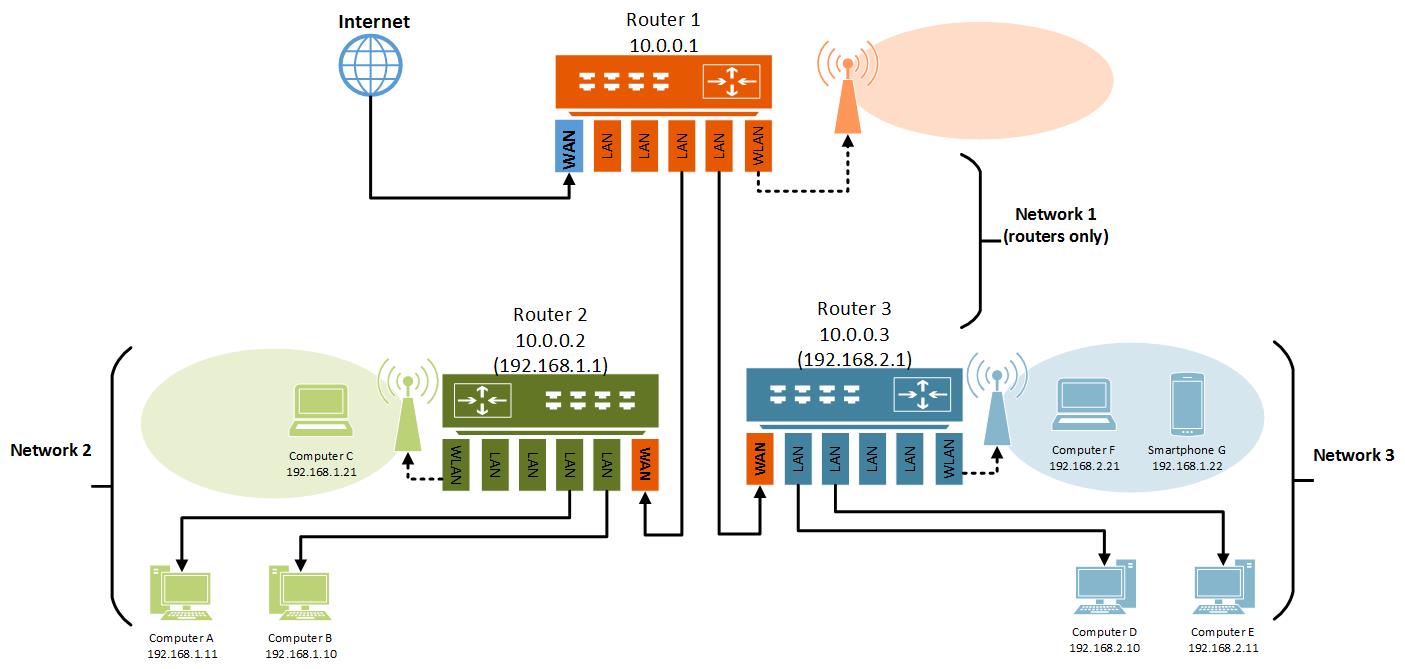
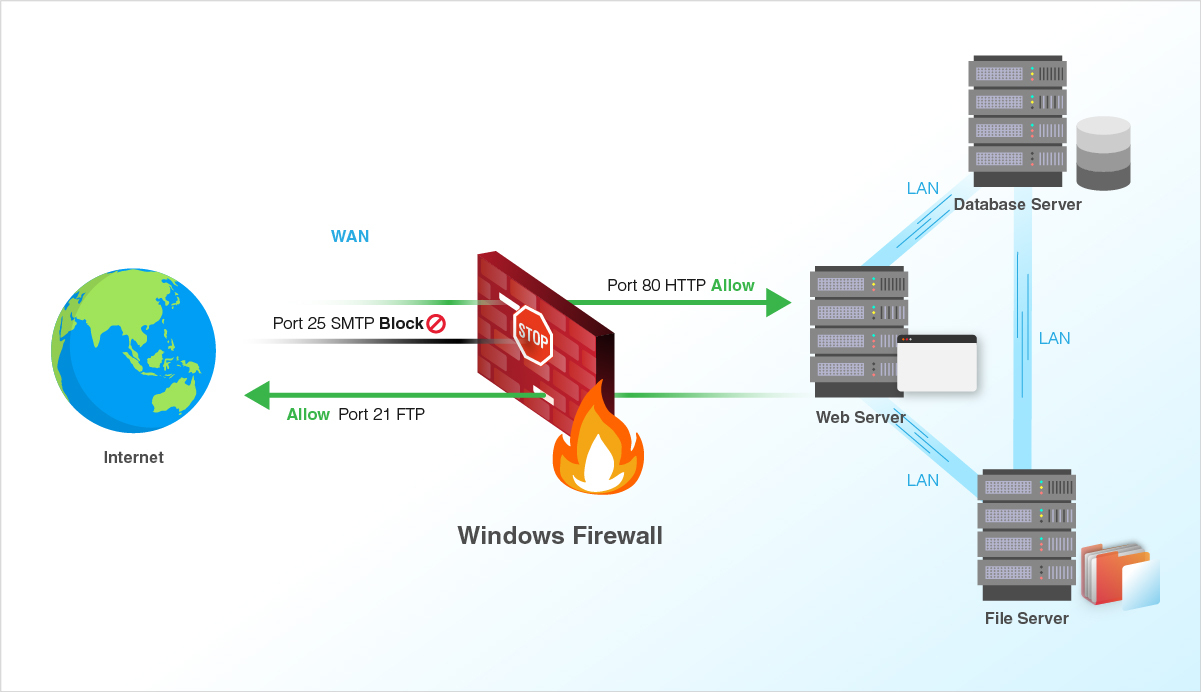
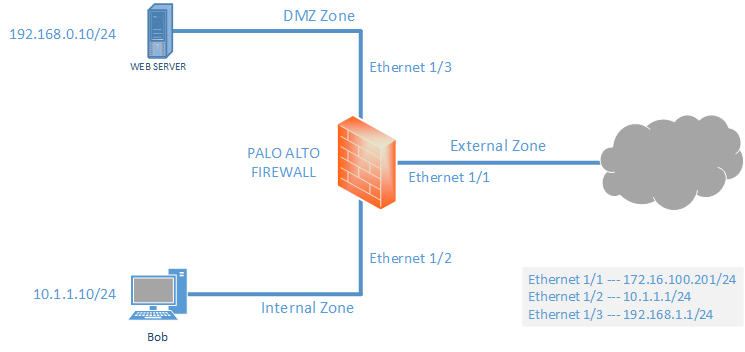
The G router firewall configuration involves setting up rules to control traffic flow. These rules are based on source and destination IP addresses, ports, and protocols. By creating these rules, you can allow or block specific traffic, depending on your network's requirements. The firewall configuration can be complex, but with the right guidance, you can set it up effectively.
Steps to Configure G Router Firewall
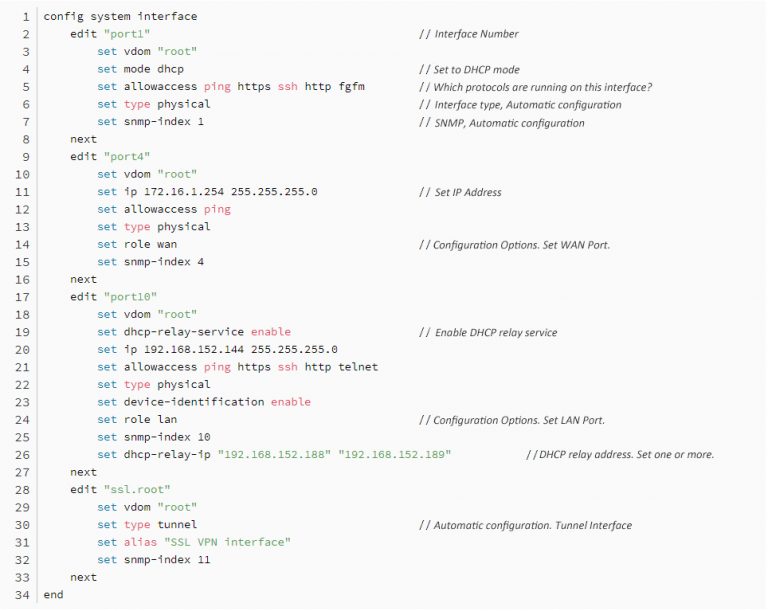
Sign into your GFiber account and access your router's settings. From here, you can navigate to the firewall configuration section.
Understand the different firewall tables, such as Filter, NAT, and Mangle. Each table serves a specific purpose, and you need to configure them accordingly.
Create rules to control incoming and outgoing traffic. You can allow or block specific traffic based on source and destination IP addresses, ports, and protocols.
Set up interface lists to manage traffic flow. These lists can help you simplify the configuration process and make it more manageable.
Test your firewall configuration to ensure it is working correctly. You can use tools like ping and traceroute to test connectivity.
Furthermore, visual representations like the one above help us fully grasp the concept of G Router Firewall Configuration.
Best Practices for G Router Firewall Configuration
Keep your firmware up to date to ensure you have the latest security patches and features.
Use strong passwords and enable WPA2 encryption to secure your wireless network.
Configure the firewall to allow only necessary traffic and block everything else.
Regularly review and update your firewall rules to ensure they are still effective.
Conclusion

Such details provide a deeper understanding and appreciation for G Router Firewall Configuration.
The G router firewall configuration is a critical aspect of network security. By following the steps outlined in this article, you can configure your firewall effectively and enjoy a more secure and stable network. Remember to keep your firmware up to date, use strong passwords, and regularly review and update your firewall rules to ensure your network remains secure.
Additional Resources
Cisco documentation on router security
OpenWrt documentation on firewall configuration
Shorewall documentation on firewall configuration
By following these resources and the steps outlined in this article, you can configure your G router firewall effectively and enjoy a more secure and stable network.


![[OpenWrt Wiki] Firewall Builder: Shorewall-lite [OpenWrt Wiki] Firewall Builder: Shorewall-lite - G Router Firewall Configuration](https://static.tp-link.com/resources/UploadFiles/Images/acimage012.jpg)








![[OpenWrt Wiki] IPv4 firewall examples Picture of [OpenWrt Wiki] IPv4 firewall examples](https://www.vpnunlimited.com/img/help/wifi-encryption_17219.jpg)

![[OpenWrt Wiki] Firewall configuration /etc/config/firewall [OpenWrt Wiki] Firewall configuration /etc/config/firewall - G Router Firewall Configuration](https://fiverr-res.cloudinary.com/images/t_main1,q_auto,f_auto,q_auto,f_auto/gigs2/343369801/original/665b41eb7a1e1c2114d95d8d3c086806d2edd180/configure-routers-firewalls-network-security-devices.png)