Ransomware Security Solutions: Protect Your Business from Cyber Threats
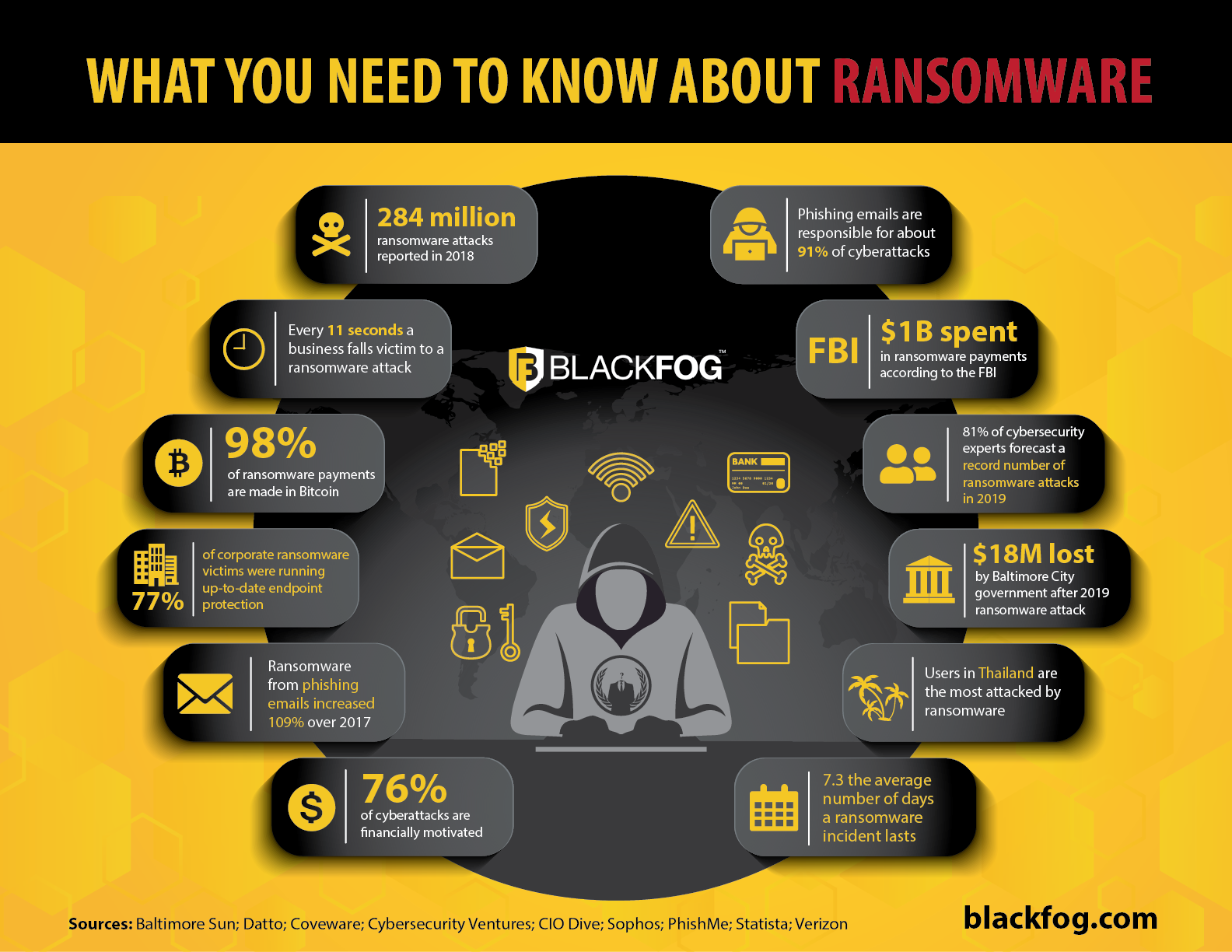
Ransomware attacks have become a growing concern for businesses of all sizes, causing significant financial losses and reputational damage. In this article, we will explore the importance of Ransomware Security Solutions and provide you with a comprehensive guide to protecting your business from these cyber threats.
What is Ransomware?
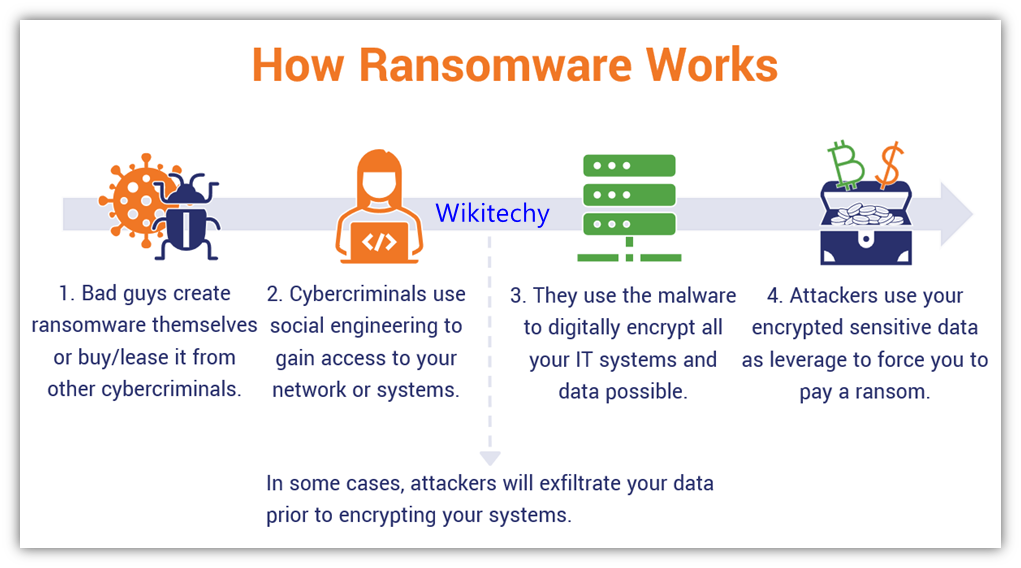
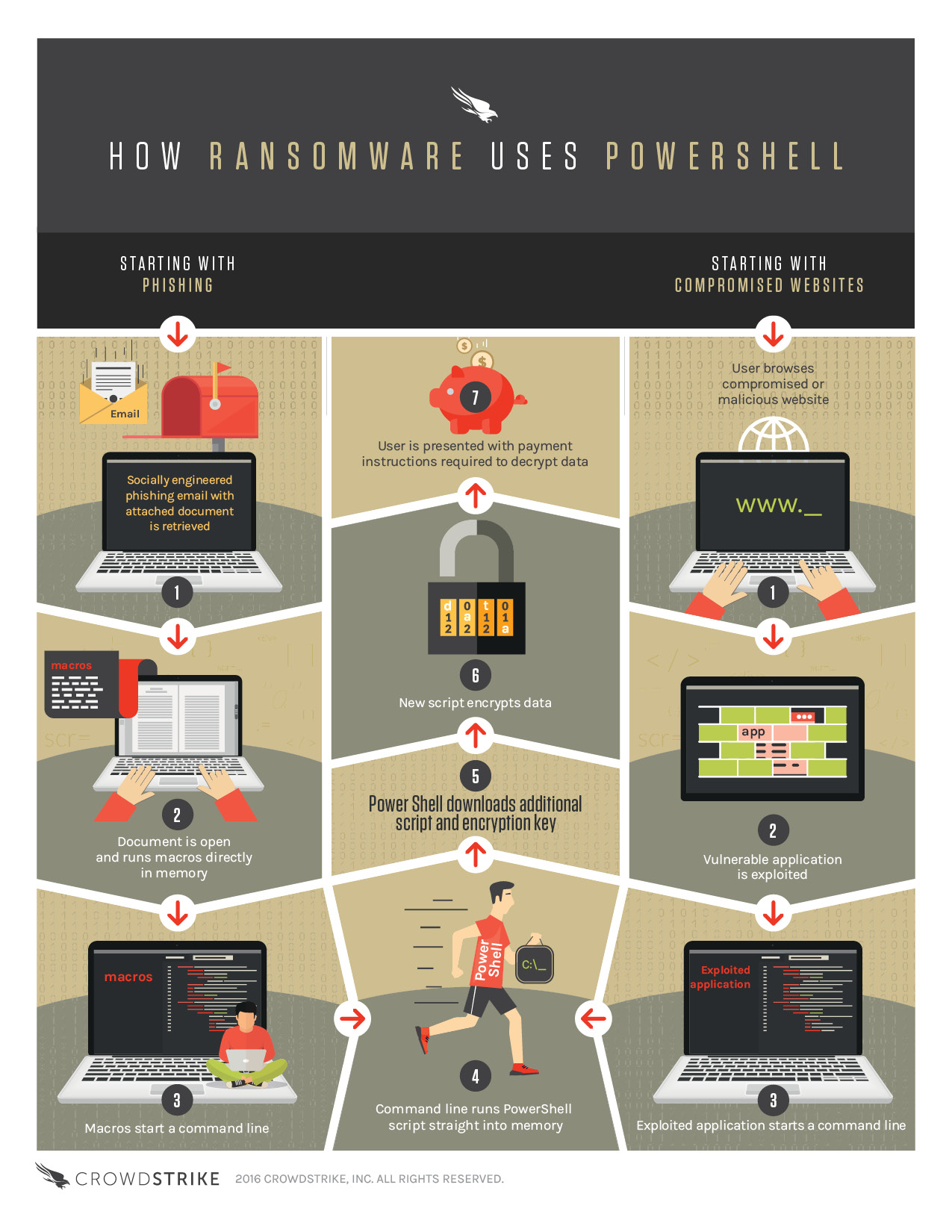
Ransomware is a type of malicious software that locks or encrypts your computer and mobile devices or electronic files, demanding a ransom in exchange for the decryption key or unlock code. This type of cyberattack is often launched through phishing emails, infected software downloads, or exploited vulnerabilities in your system.
Why Ransomware Security Solutions are Essential

Ransomware Security Solutions are designed to prevent, detect, and respond to ransomware attacks. These solutions can help protect your business from financial losses, reputational damage, and legal liabilities. By implementing effective Ransomware Security Solutions, you can ensure the integrity and availability of your data, as well as the security of your systems and networks.
Types of Ransomware Security Solutions
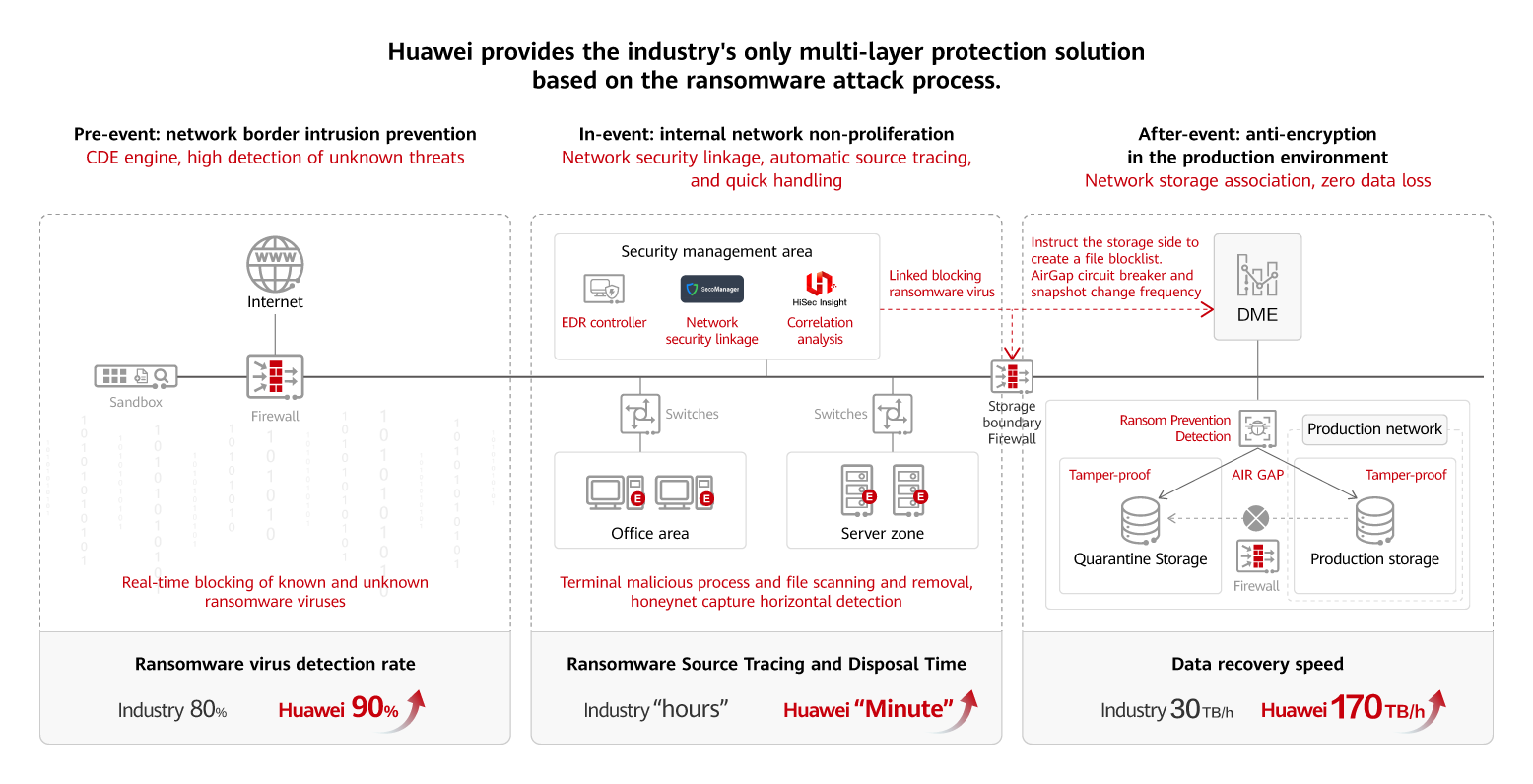
- Endpoint Security Solutions: These solutions protect individual computers and mobile devices from ransomware attacks, using real-time threat detection and response capabilities.
- Network Security Solutions: These solutions protect your network from ransomware attacks, using firewalls, intrusion detection systems, and other network security tools.
- Data Security Solutions: These solutions protect your sensitive data from ransomware attacks, using encryption, access controls, and other data security tools.
- Cloud Security Solutions: These solutions protect your cloud-based data and applications from ransomware attacks, using cloud security tools and services.
- Real-time Threat Detection: Effective Ransomware Security Solutions use real-time threat detection capabilities to identify and block ransomware attacks.
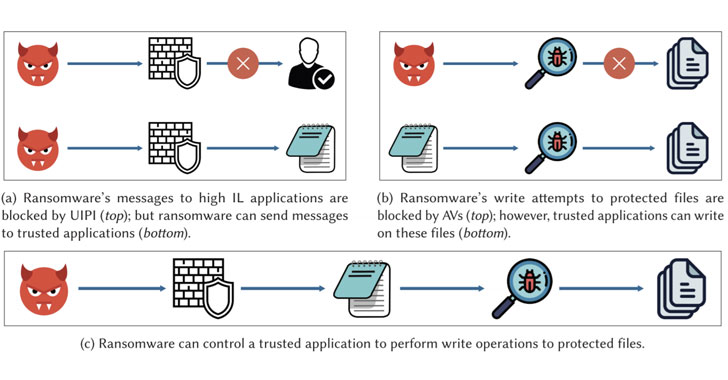
- Behavioral Analysis: These solutions use behavioral analysis to identify and prevent ransomware attacks based on their behavior.
- Encryption: Effective Ransomware Security Solutions use encryption to protect sensitive data from ransomware attacks.
- Access Controls: These solutions use access controls to restrict access to sensitive data and prevent unauthorized access.
- Regular Updates and Patches: Effective Ransomware Security Solutions receive regular updates and patches to stay ahead of emerging threats.
This particular example perfectly highlights why Ransomware Security Solutions is so captivating.
Best Practices for Implementing Ransomware Security Solutions
To ensure the effectiveness of your Ransomware Security Solutions, follow these best practices:
- Conduct Regular Security Audits: Conduct regular security audits to identify vulnerabilities and weaknesses in your systems and networks.
- Implement a Robust Incident Response Plan: Develop and implement a robust incident response plan to respond to ransomware attacks.
- Provide Employee Training: Provide regular employee training to educate them on ransomware threats and best practices for preventing attacks.
- Use Advanced Threat Protection: Use advanced threat protection tools to detect and prevent ransomware attacks.
Conclusion
Ransomware Security Solutions are essential for protecting your business from cyber threats. By understanding the types of ransomware security solutions available, their key features, and best practices for implementation, you can ensure the integrity and availability of your data, as well as the security of your systems and networks. Remember to conduct regular security audits, implement a robust incident response plan, provide employee training, and use advanced threat protection to stay ahead of emerging threats.






![[PLAY] - Ransomware Victim: All Real Estate Title Solutions Image showcasing [PLAY] - Ransomware Victim: All Real Estate Title Solutions](https://spin.ai/wp-content/uploads/2024/01/The-History-and-Evolution-of-Ransomware.jpg)
.jpg)

.webp)




![[QILIN] - Ransomware Victim: Kaemmerlen Solutions - RedPacket Security View of [QILIN] - Ransomware Victim: Kaemmerlen Solutions - RedPacket Security](https://i0.wp.com/www.novicus.com/wp-content/uploads/2016/11/ransom.jpg?fit=970%2C546&ssl=1)