File Integrity Monitoring Analysis: Safeguarding Digital Assets and Ensuring Cybersecurity
File integrity monitoring (FIM) is a critical security process that monitors and analyzes the integrity of critical assets for signs of tampering or corruption. It is an essential component in safeguarding digital assets and ensuring cybersecurity. In this article, we will delve into the world of file integrity monitoring, discussing its importance, benefits, and best practices in implementing a FIM solution.
What is File Integrity Monitoring?
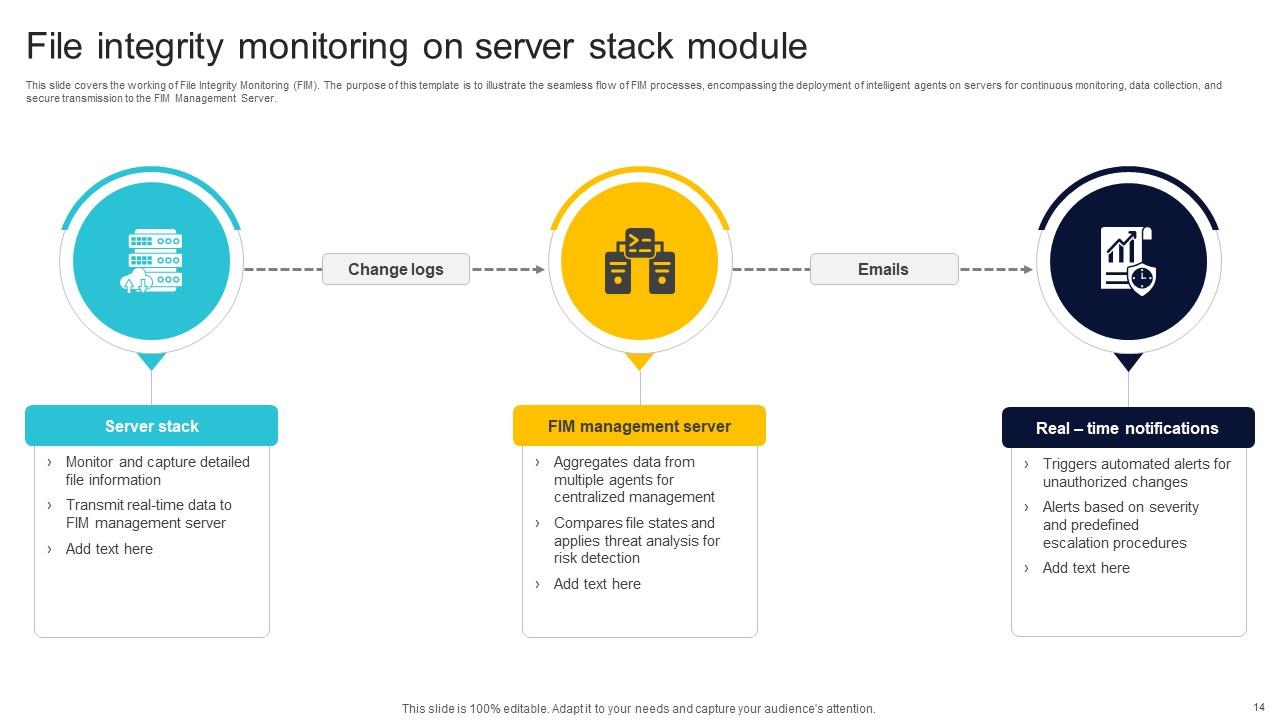
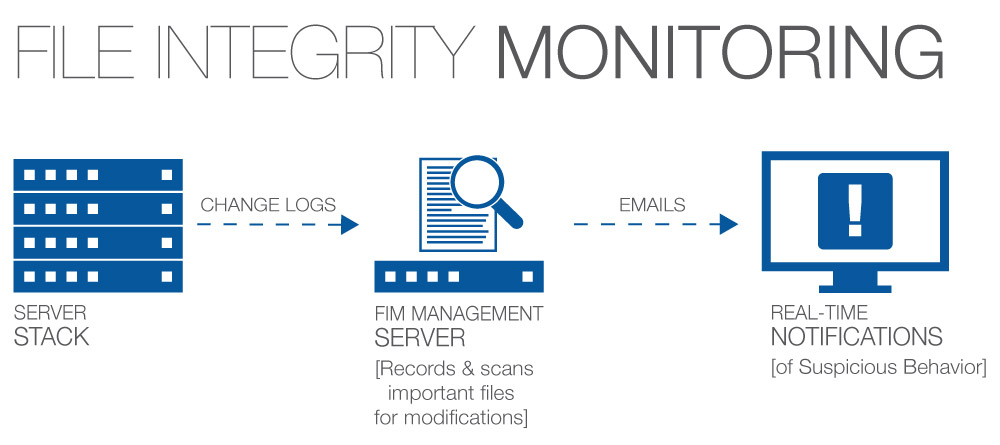
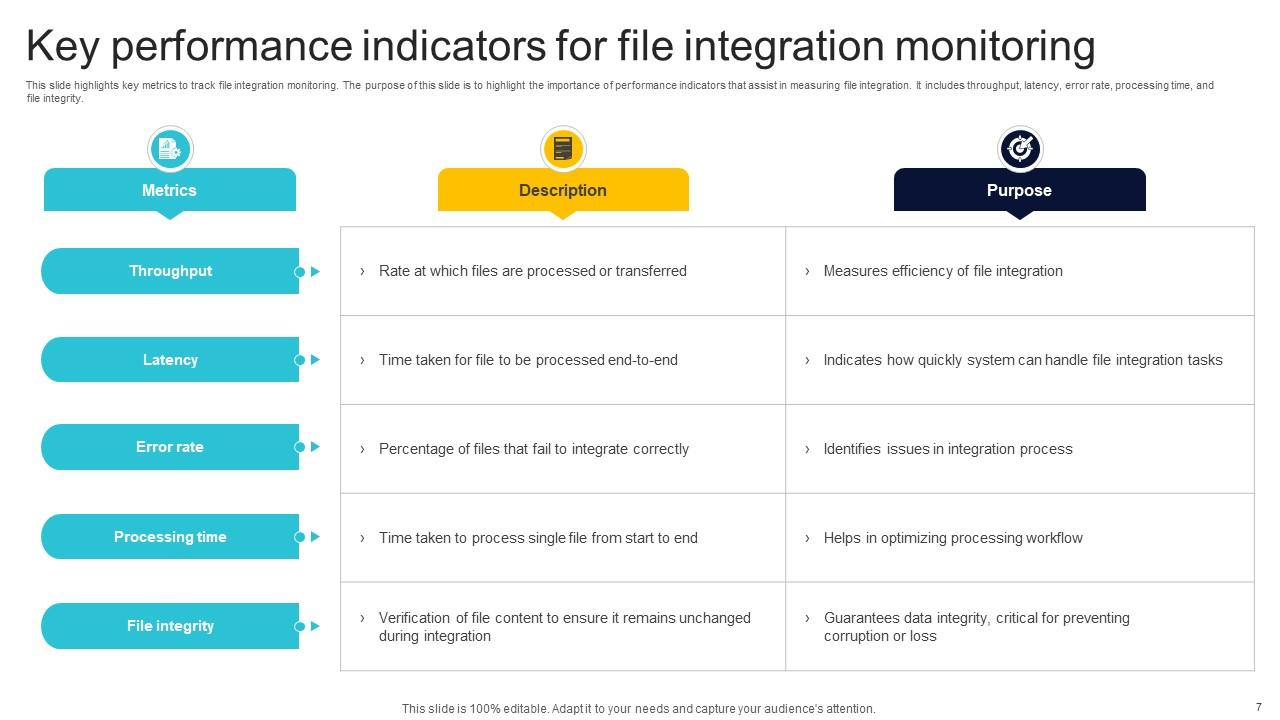
File integrity monitoring is a security process that monitors and detects file changes, alerting administrators to potential security breaches or compliance issues. It examines the integrity of sensitive files, registry keys, and folders within the host operating system, tracking logs and comparing the current version to a known baseline. This allows organizations to monitor, detect, and prevent unauthorized file changes, ensuring the integrity and security of their digital assets.
Benefits of File Integrity Monitoring

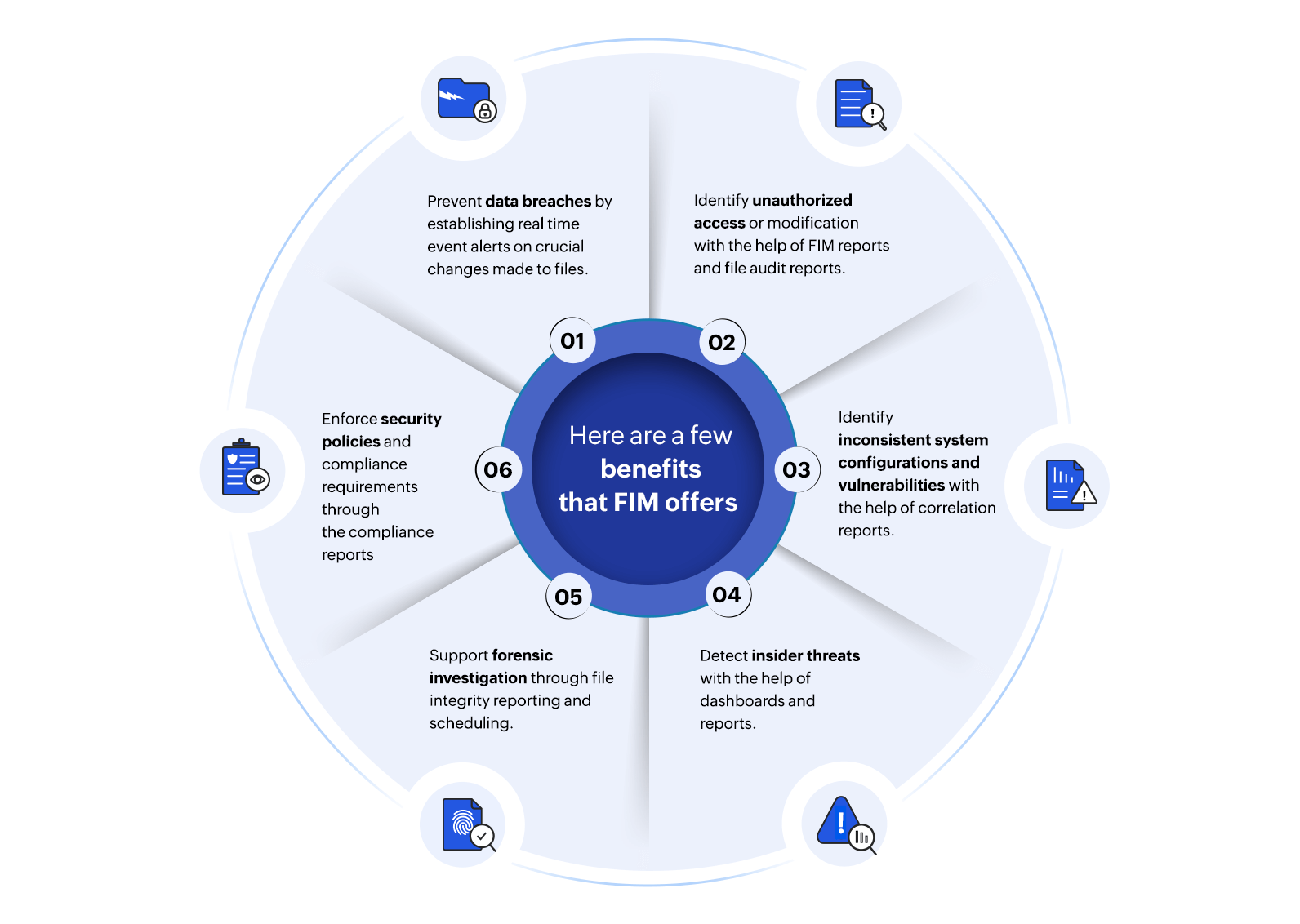
As we can see from the illustration, File Integrity Monitoring Analysis has many fascinating aspects to explore.
The benefits of file integrity monitoring are numerous, including:
- Meeting compliance requirements: File integrity monitoring helps organizations meet regulatory compliance standards such as PCI-DSS and ISO 17799.
- Early detection of security breaches: FIM detects unauthorized changes to files and systems, enabling early detection of security breaches.
- Enhanced security: File integrity monitoring strengthens an organization's security posture by detecting and preventing unauthorized file modifications.
- Improved incident response: FIM provides valuable information for incident response, enabling security teams to investigate and respond to security incidents more effectively.
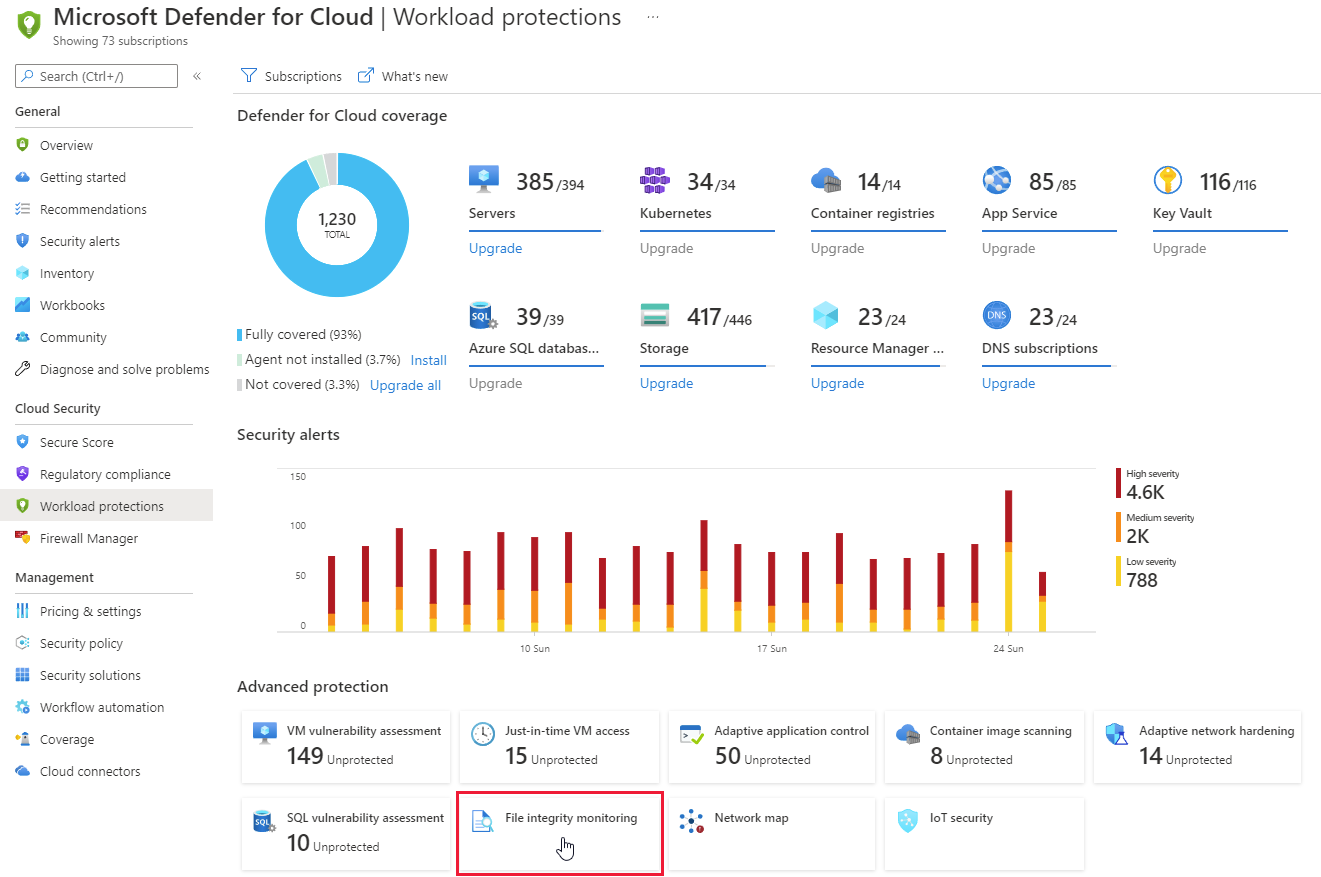
File Integrity Monitoring Tools and Solutions
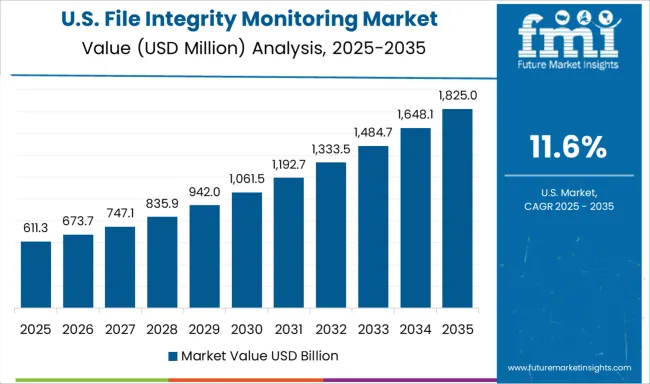
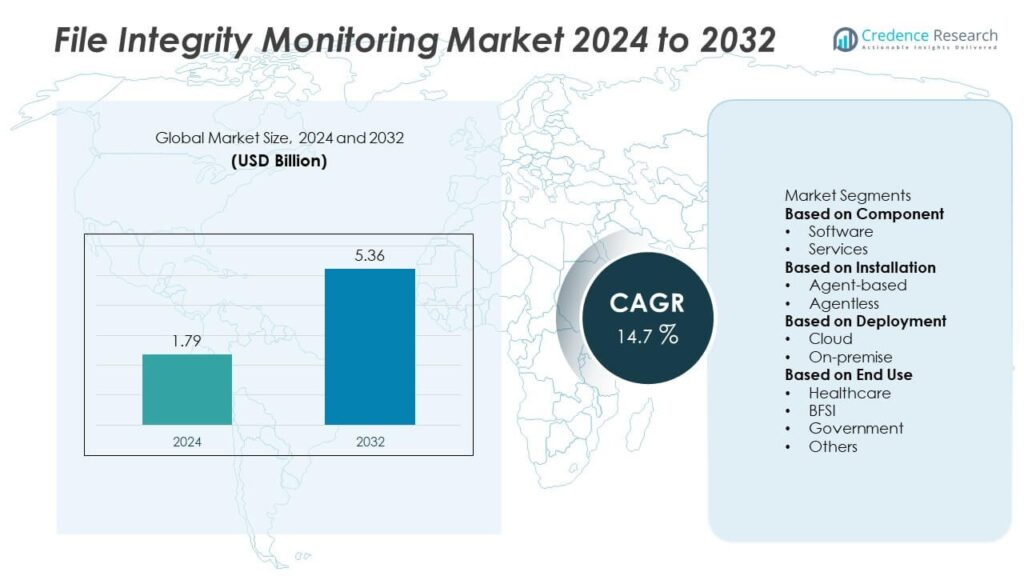
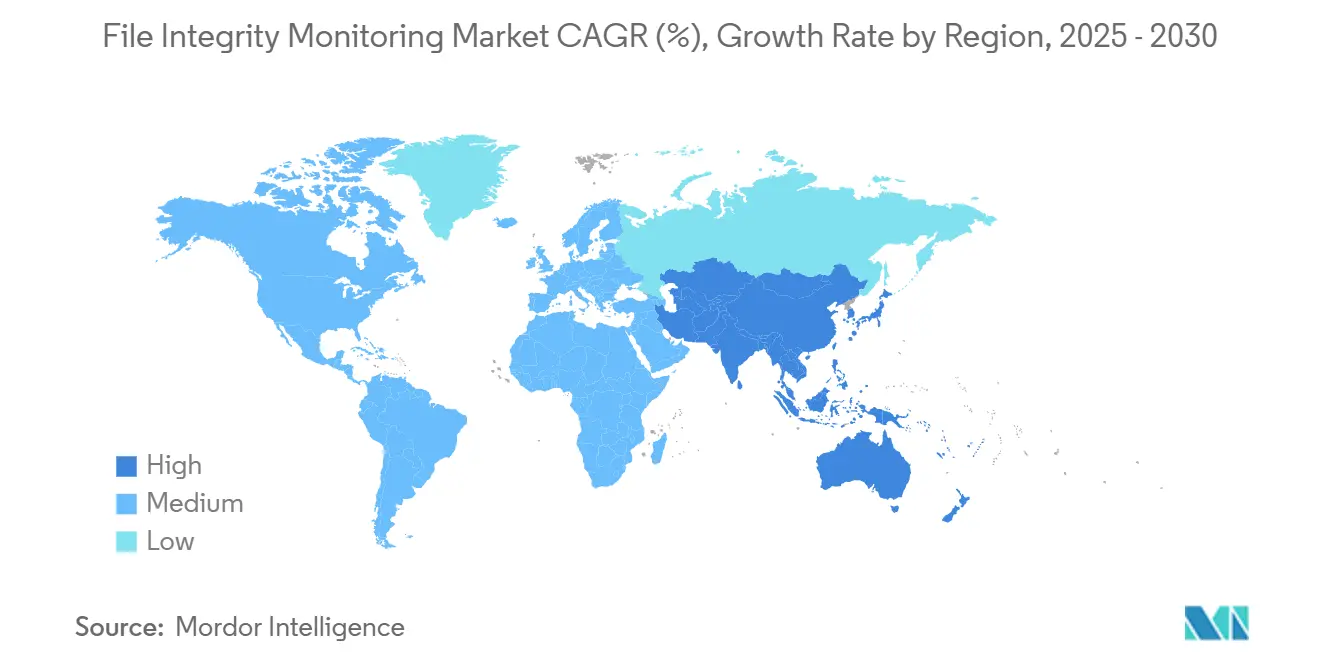
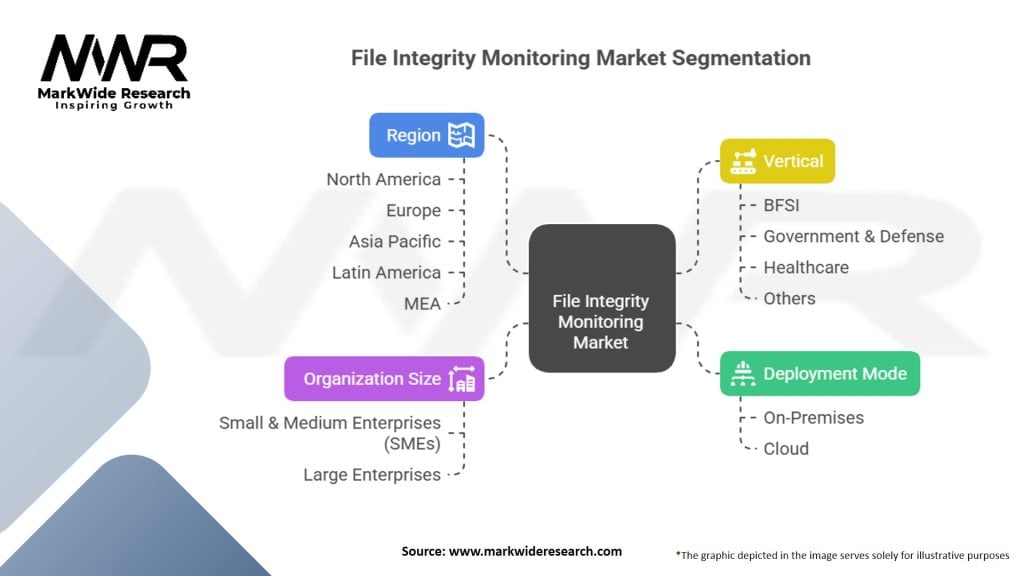
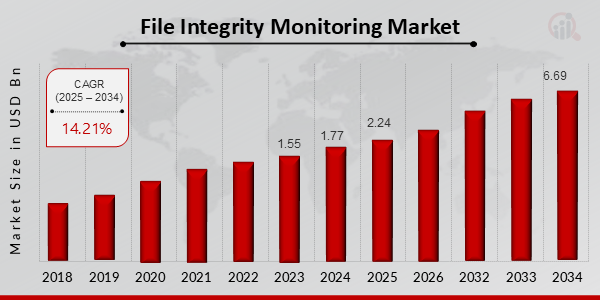
The file integrity monitoring market is experiencing robust growth, propelled by increasing cybersecurity threats and regulatory compliance requirements. Real-time monitoring solutions are crucial for detecting unauthorized changes, making software segment the top performer in the FIM market. Some leading file integrity monitoring tools and solutions include:
- Atomicorp FIM as a Service: A simple, low-cost way to detect unauthorized file changes, meet compliance requirements, and strengthen security posture.
- OSSEC: A free open-source file integrity monitoring solution that detects unauthorized file changes and meets compliance requirements.
- Microsoft Defender for Endpoint: A comprehensive security solution that includes file integrity monitoring and real-time threat detection.
Best Practices for Implementing File Integrity Monitoring
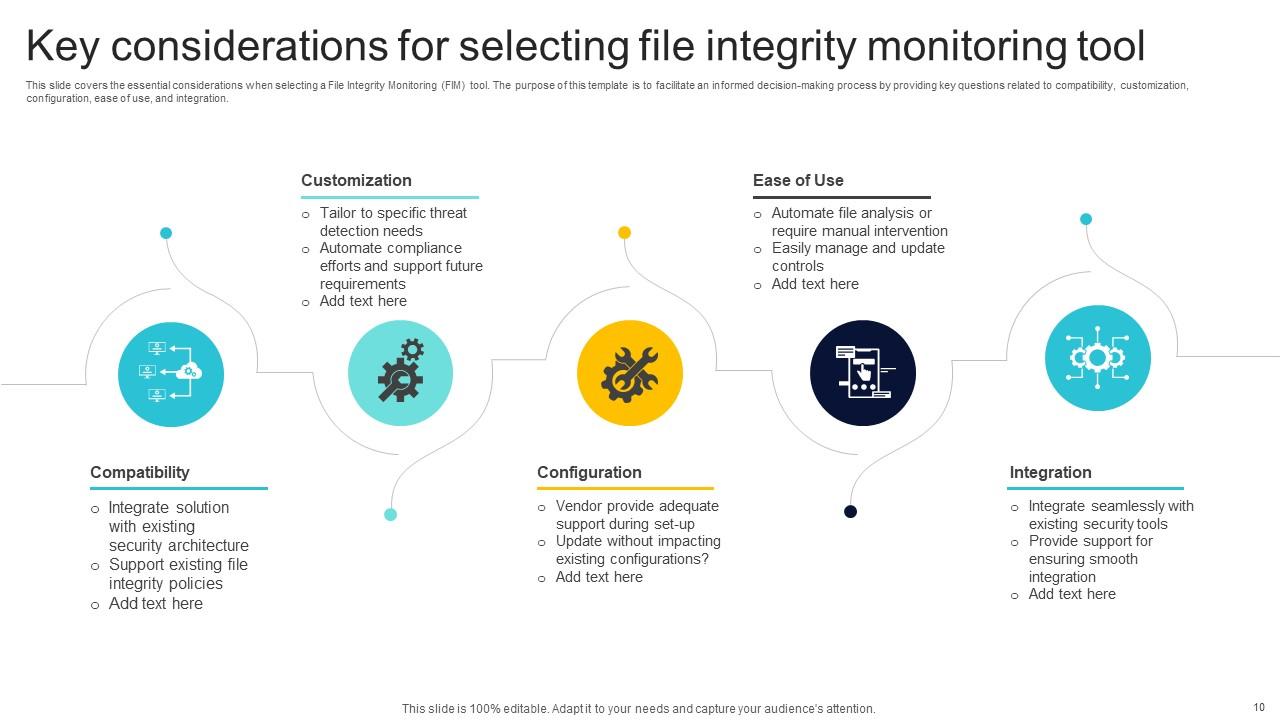
- Choose a reliable file integrity monitoring solution that meets your organization's security needs.
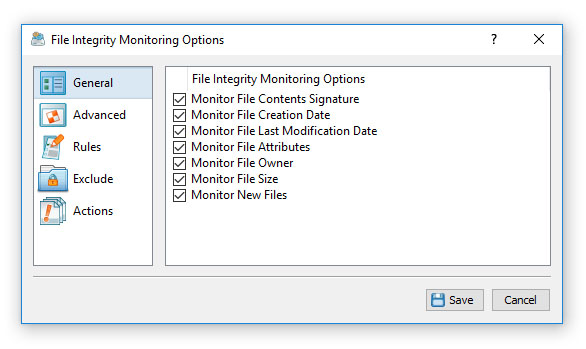
- Configure FIM to monitor critical files, folders, and registry keys.
- Regularly update and maintain the baseline to ensure accurate monitoring.
- Implement a backup and recovery plan to mitigate potential data loss.
- Monitor and analyze FIM data to identify potential security risks and incidents.
Conclusion
File integrity monitoring is a critical component in safeguarding digital assets and ensuring cybersecurity. It helps organizations meet compliance requirements, detect security breaches early, and strengthen their security posture. By understanding the importance and benefits of file integrity monitoring, best practices for implementing FIM, and leading tools and solutions, organizations can effectively protect their digital assets and maintain a secure and compliant environment.












![[시장보고서]파일 무결성 모니터링 시장 분석 및 예측 (-2035년) : 유형별, 제품 유형별, 서비스별, 기술별, 컴포넌트별 ... [시장보고서]파일 무결성 모니터링 시장 분석 및 예측 (-2035년) : 유형별, 제품 유형별, 서비스별, 기술별, 컴포넌트별 ... - File Integrity Monitoring Analysis](https://orthoplexsolutions.com/wp-content/uploads/2025/01/file_integrity_monitoring_2nd_section-scaled.webp)