Protecting Your Business from Unauthorized Data Access: A Comprehensive Guide
Unauthorized data access is a critical concern for businesses today. With the increasing use of technology and the internet, the risk of data breaches and unauthorized access has never been higher. In this article, we will explore how to protect data from unauthenticated access and provide you with the strategies and tools you need to safeguard your business's sensitive information.
The Risks of Unauthorized Data Access
What is Unauthorized Data Access?
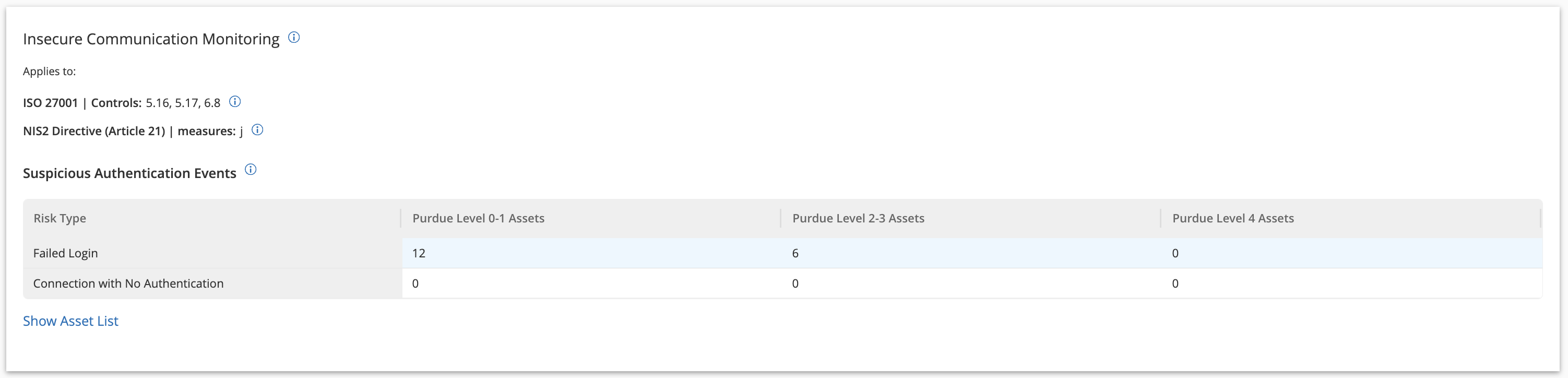
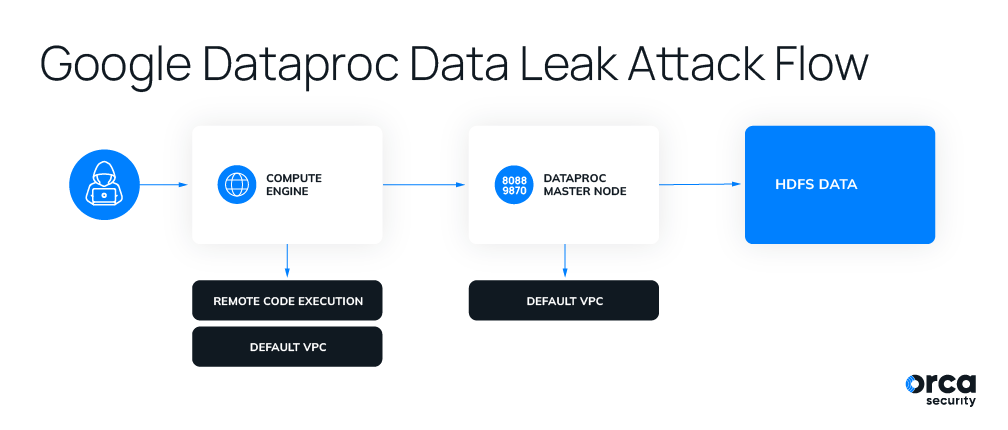
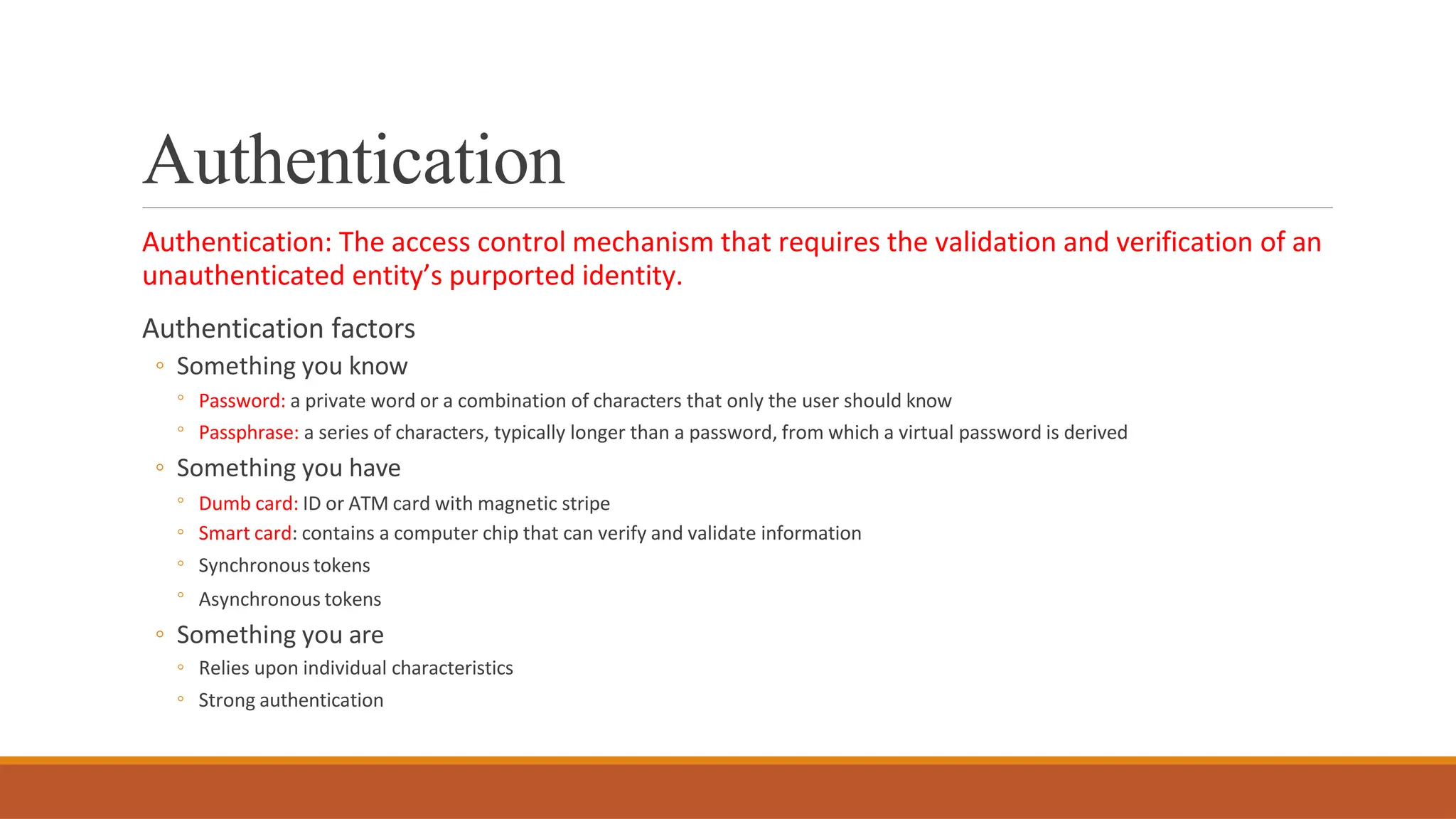
Unauthorized data access refers to the unauthorized access to a business's data, networks, endpoints, applications, or devices, without permission. It is closely related to authentication - a process that verifies a user's identity when they access a system. Broken, or misconfigured authentication can lead to unauthorized access, making it essential to implement robust authentication mechanisms to protect your business's data.

How to Protect Data from Unauthenticated Access
To protect your business's data from unauthorized access, you need to implement a layered approach to security. Here are some strategies and tools you can use:
- Implement strong passwords and multi-factor authentication to protect user accounts and prevent unauthorized access.
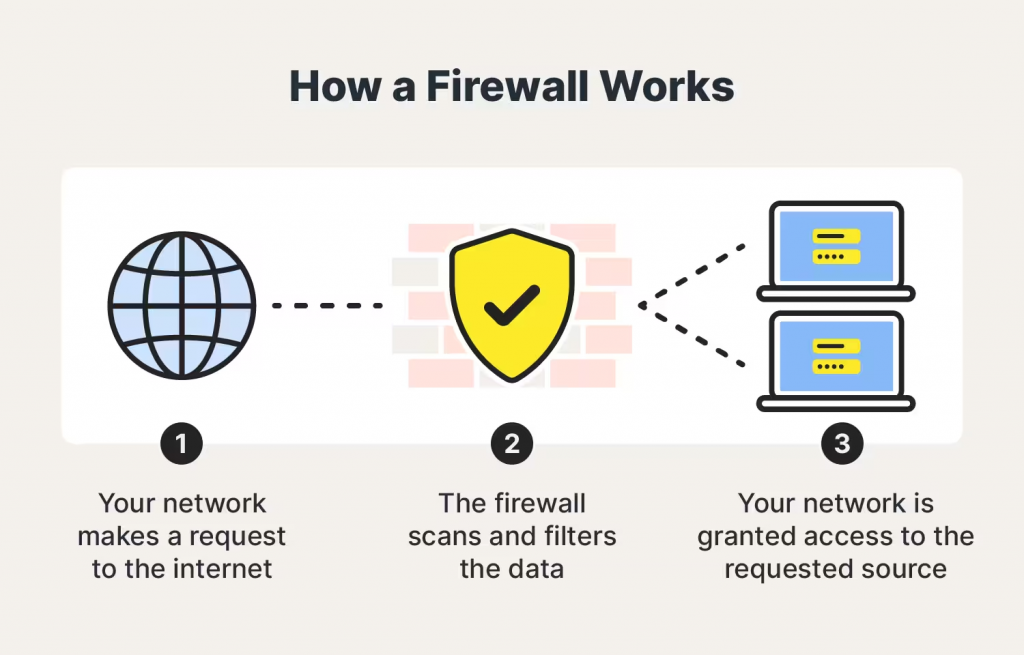
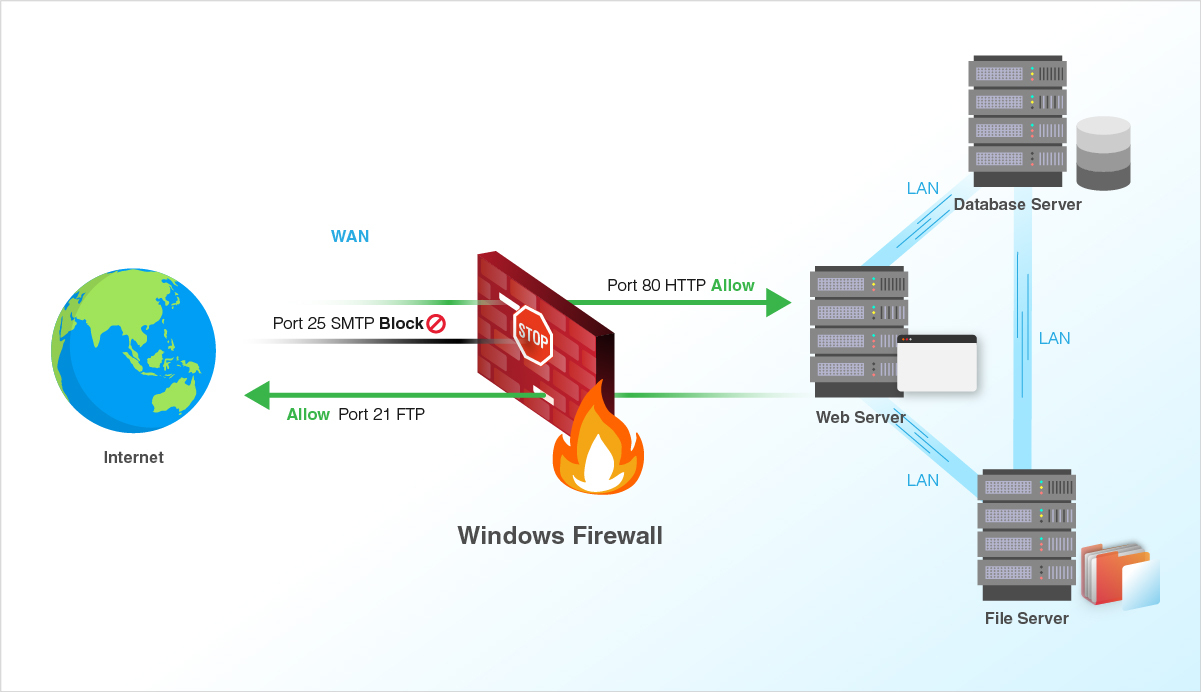
- Use firewalls to restrict access to sensitive data and networks.
- Deploy a reverse proxy with authentication to protect against unauthenticated access.
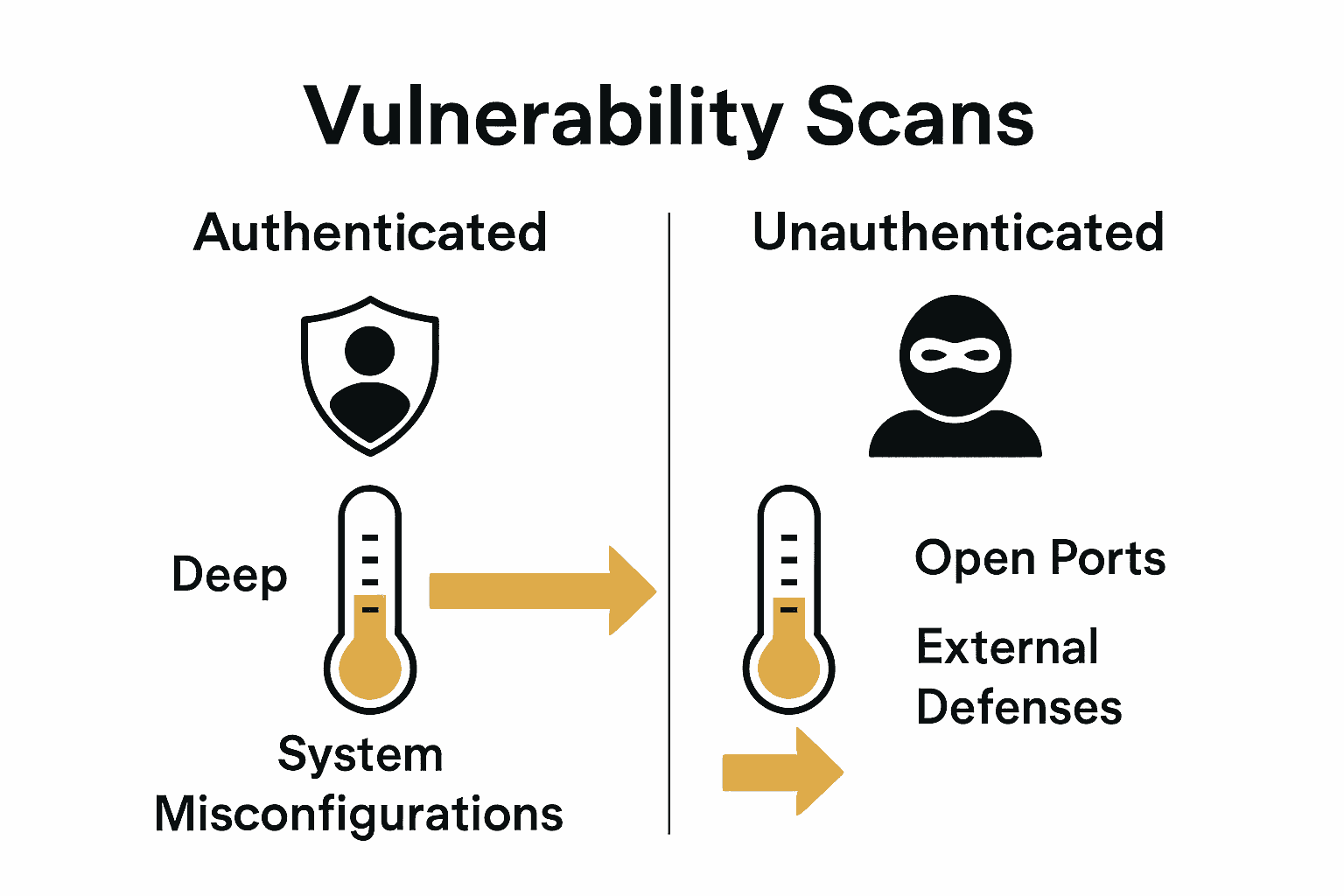
- Use application security testing tools to identify vulnerabilities and weaknesses in your applications.
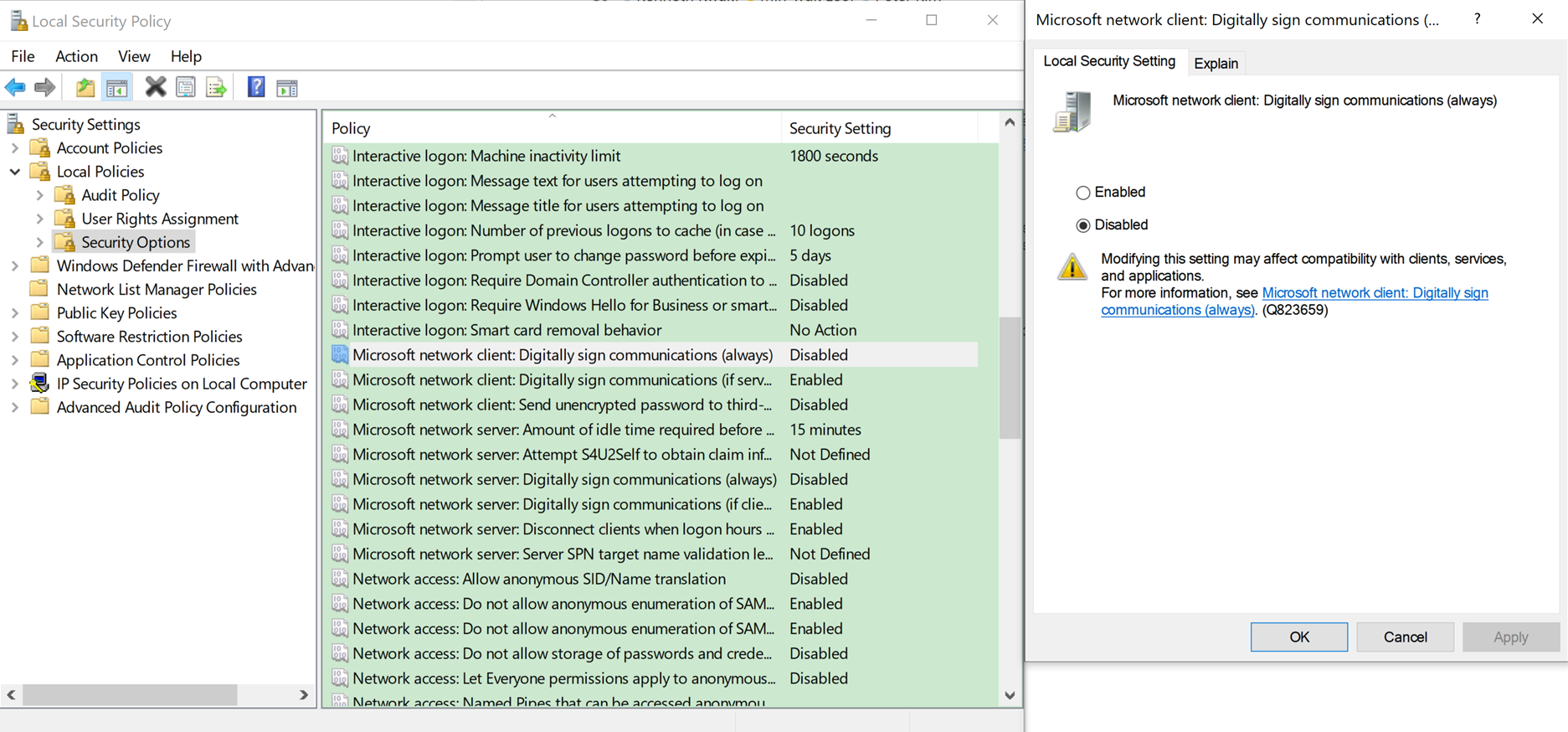
- Implement data encryption to protect sensitive data from unauthorized access.
- Regularly review and update access controls to prevent excess privileges from accumulating over time.
- Use endpoint security software to protect endpoints from unauthorized access and malware.
Key Takeaways

- Unauthorized data access can have devastating consequences for a business.
- Unauthorized data access refers to the unauthorized access to a business's data, networks, endpoints, applications, or devices, without permission.
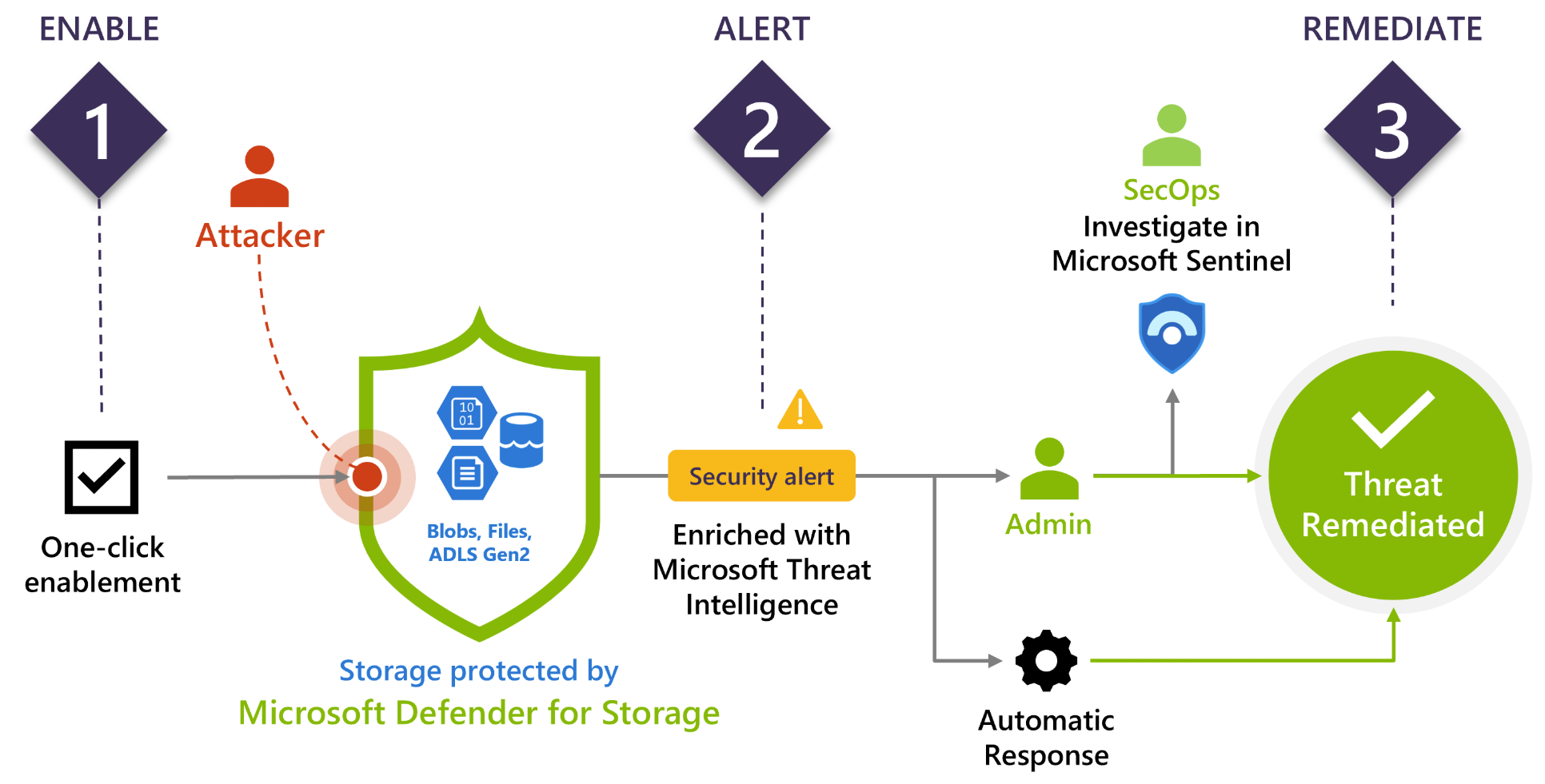
- Implementing strong authentication mechanisms, firewalls, and data encryption are essential strategies for protecting business data from unauthorized access.
- Regularly reviewing and updating access controls, and using application security testing tools and endpoint security software can help prevent unauthorized access and data breaches.
Conclusion
References
- Microsoft's guide to securing data with Zero Trust.
- UBSAN fingerprint caused by float overflow inside x86 SSE2 optimized function.
- Update now: Critical vulnerability allows hackers to compromise systems without credentials.
- TEE technology protects sensitive data in cloud computing.
Moving forward, it's essential to keep these visual contexts in mind when discussing How To Protect Data From Unauthenticated Access.
Additional Resources
For more information on how to protect your business's data from unauthorized access, check out the following resources:
- Microsoft's guide to securing data with Zero Trust.
- Ubiquiti's emergency updates for UniFi Network Application.
- StrongDM's comprehensive access management platform.
- Citrix's security updates to address critical flaws in NetScaler ADC and NetScaler Gateway.