Ways to Secure Sensitive Data: Protecting Your digital Assets in the Modern Age
Sensitive data is a valuable asset for individuals and organizations alike. However, with the rise of cyber threats and data breaches, protecting this sensitive information has become a top priority. If you're looking for ways to secure sensitive data, you're in the right place.
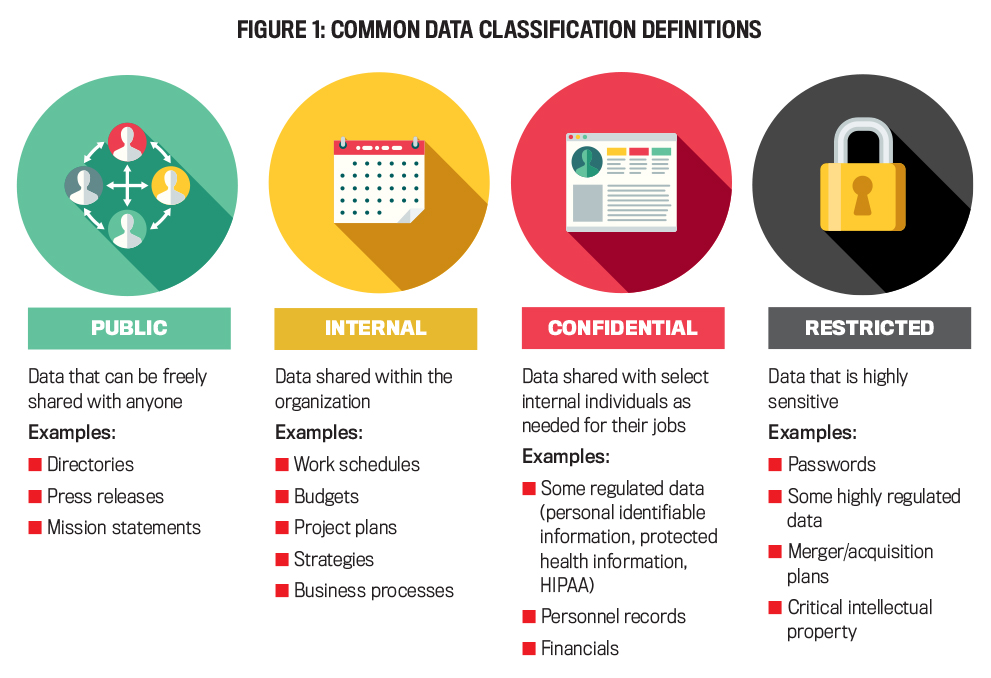
Sensitive data comes in many forms, from personal identifiable information (PII) to intellectual property. To secure sensitive data, you need to understand the common data security threats and best practices. Some of the most common threats include phishing attacks, ransomware, and data breaches. To combat these threats, you need to implement robust security measures, such as multi-factor authentication, access controls, and regular software updates.
The Importance of Data Security Policies

Data security policies are a critical component of any organization's data security strategy. These policies should outline the rules and procedures for handling sensitive data, including who has access to it, how it's stored, and how it's transmitted. Having a well-defined data security policy can help prevent data breaches and protect sensitive data.
Detection, Prevention, and Response
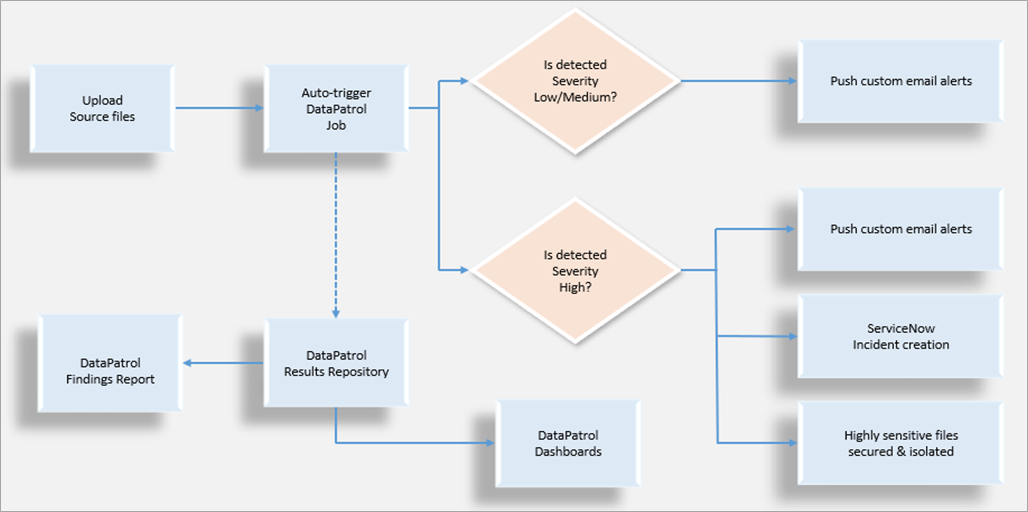
Another crucial aspect of securing sensitive data is detecting, preventing, and responding to potential threats. This includes implementing intrusion detection systems, antivirus software, and threat intelligence tools. You also need to have a plan in place for responding to data breaches, including notification procedures, containment strategies, and mitigation plans.

Top Ways to Secure Sensitive Data
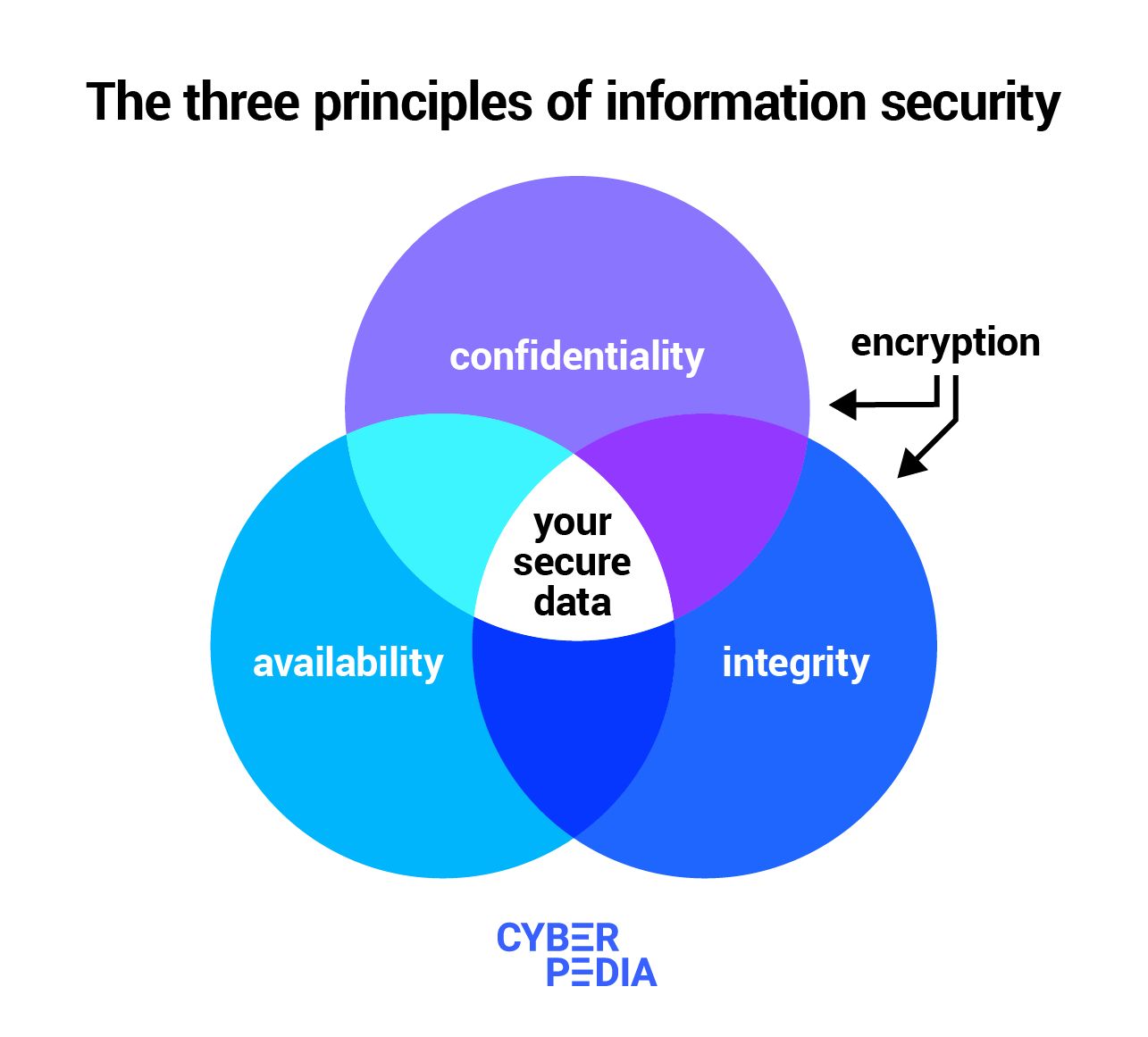
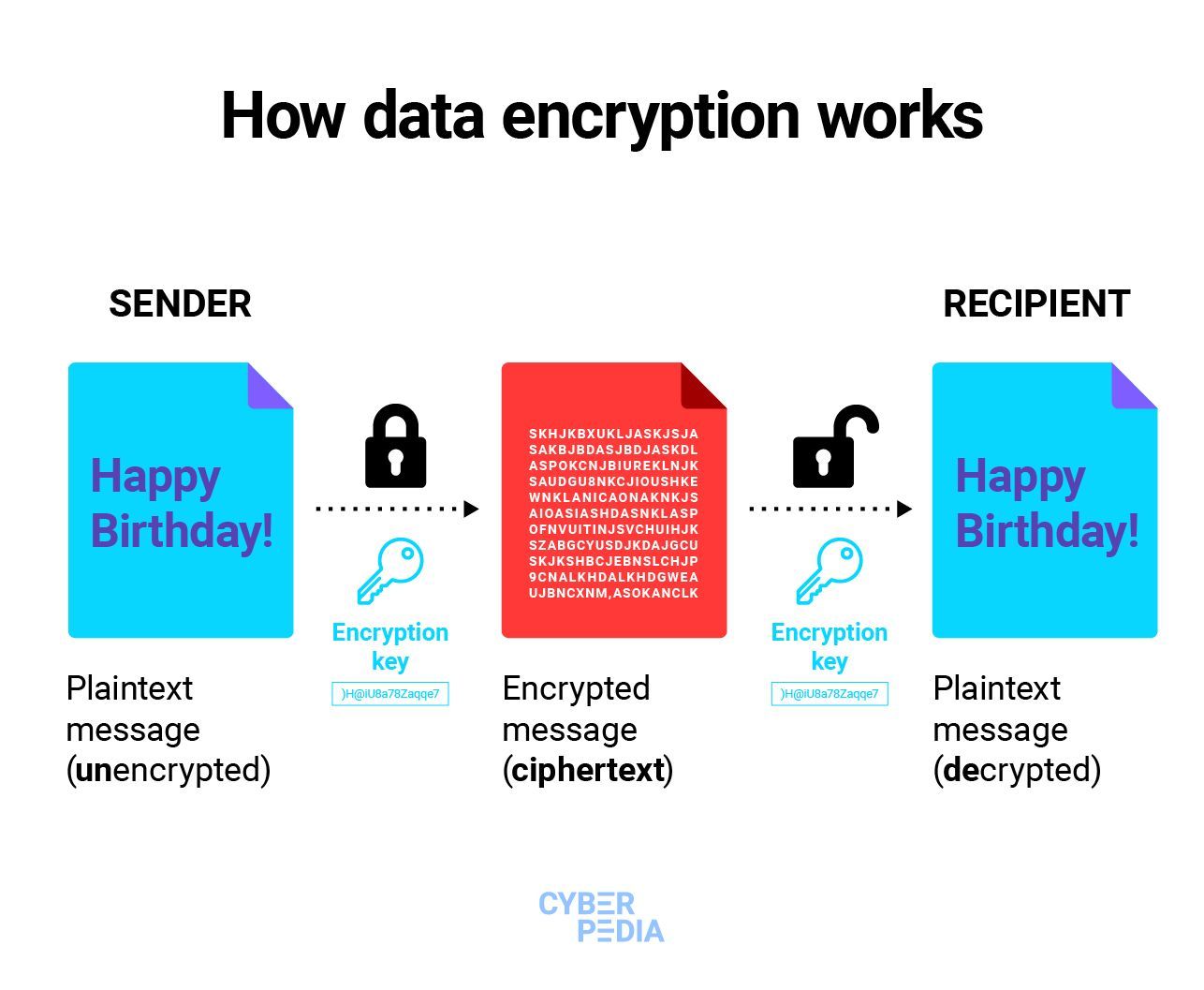
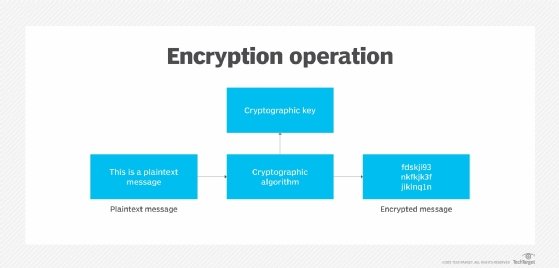
- Implement Encryption**: Encrypting sensitive data is a crucial step in securing it. This ensures that even if the data is stolen or accessed without authorization, it remains unreadable to unauthorized parties.
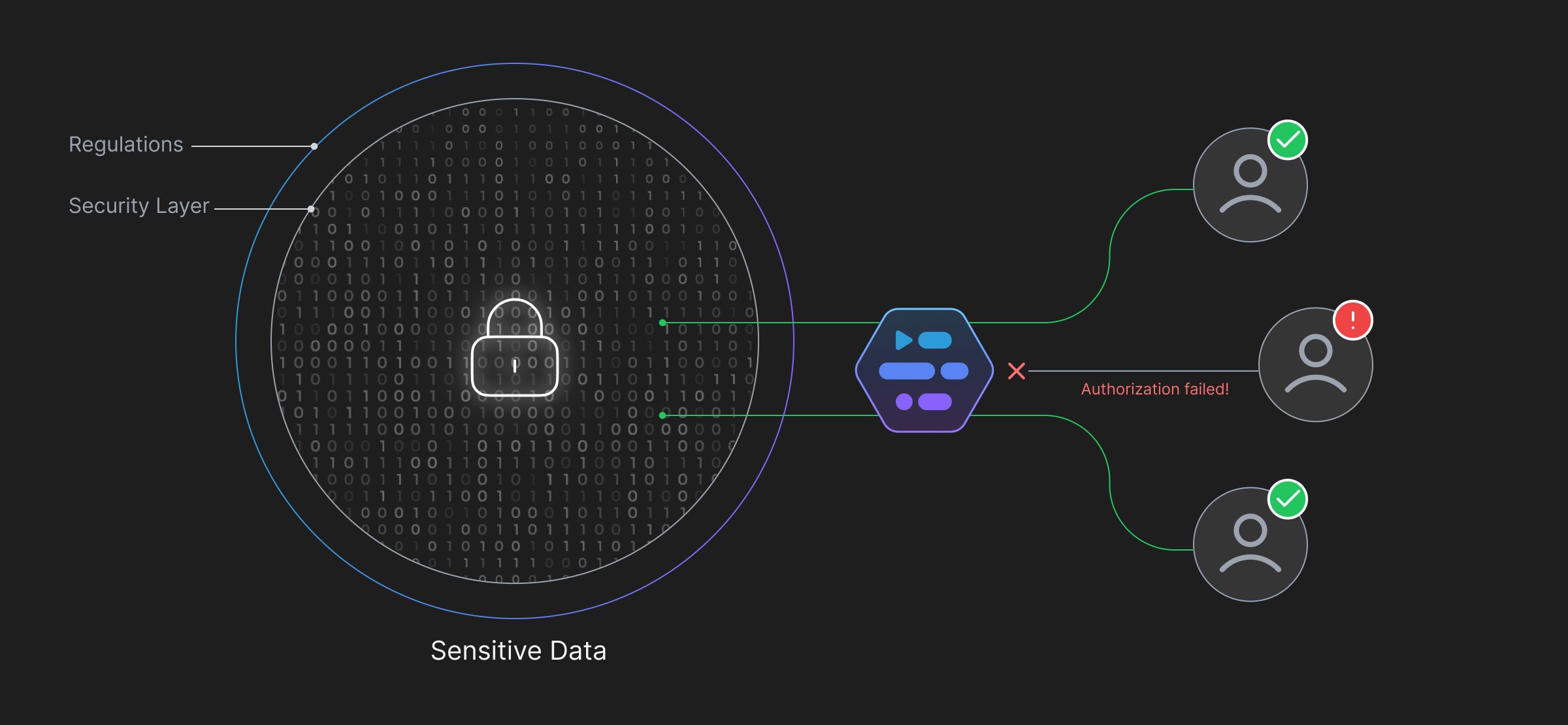
- Use Access Controls**: Access controls, such as role-based access control, need-to-know principles, and segregation of duties, can help limit who has access to sensitive data.
- Regularly Update Software**: Keeping software up to date can help patch vulnerabilities and prevent exploitation by cybercriminals.
- Conduct Regular Security Audits**: Conducting regular security audits can help identify vulnerabilities and weaknesses in your organization's data security posture.
- Implement Identity and Access Management (IAM) Systems**: IAM systems can help manage user identities and permissions, reducing the risk of unauthorized access to sensitive data.
- Use Secure Data Storage and Transmission Mechanisms**: Using secure data storage and transmission mechanisms, such as secure file sharing platforms and encrypted email, can help protect sensitive data in transit and at rest.
- Monitor and Analyze Logs**: Monitoring and analyzing logs can help detect potential security threats and identify areas for improvement in your organization's data security posture.
- Implement Incident Response Plans**: Incident response plans can help your organization respond quickly and effectively in the event of a data breach or other security incident.
- Conduct Regular Training and Awareness Programs**: Conducting regular training and awareness programs can help educate employees on data security best practices and reduce the risk of human error.
- Use Data Loss Prevention (DLP) Solutions**: DLP solutions can help prevent data leaks and theft by monitoring and controlling sensitive data in motion and at rest.
- Implement Secure Web Application Firewall (WAF) Solutions**: WAF solutions can help protect web applications from common web attacks, such as SQL injection and cross-site scripting.
The Future of Data Security
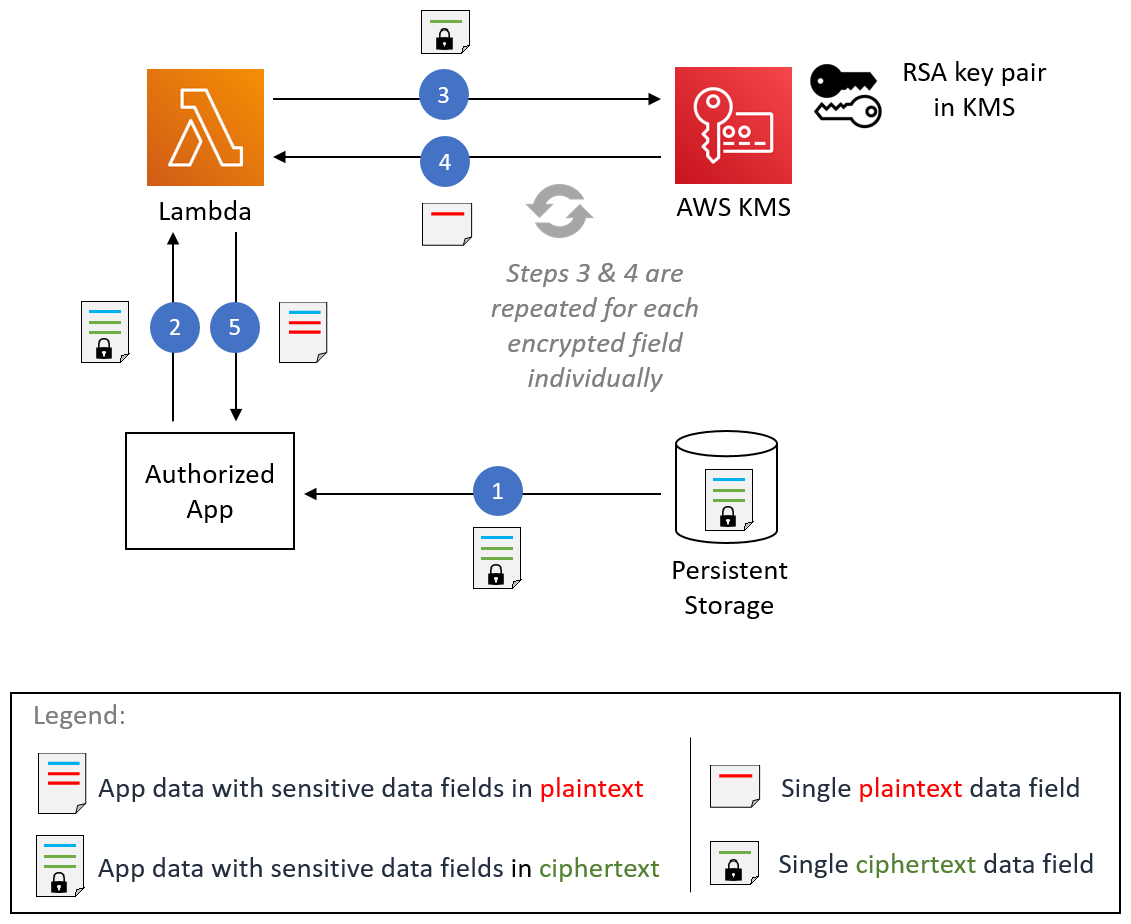
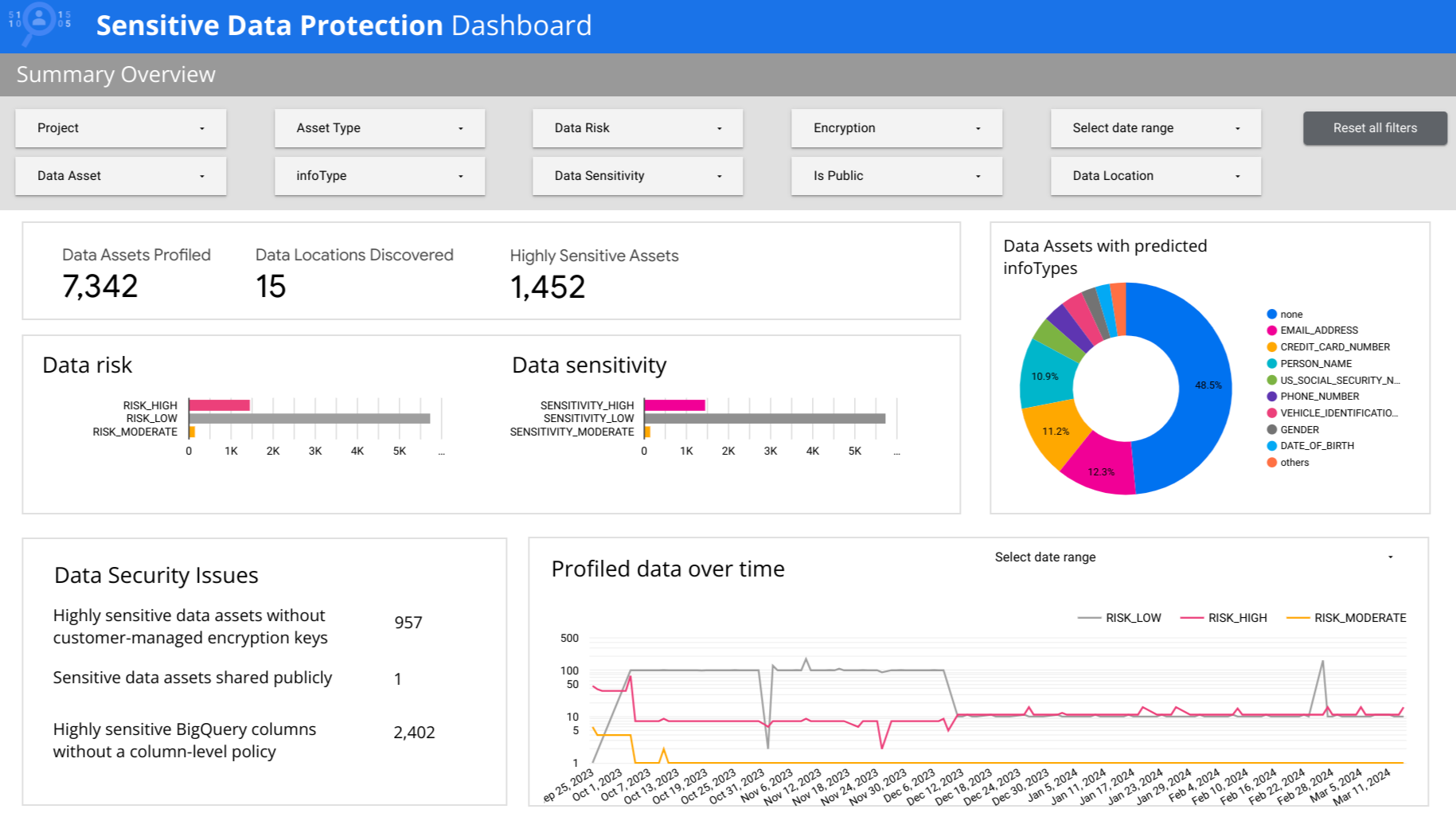
Furthermore, visual representations like the one above help us fully grasp the concept of Ways To Secure Sensitive Data.
The future of data security is exciting but also complex. With the rise of emerging technologies, such as artificial intelligence and blockchain, data security will become increasingly important. To stay ahead of the curve, organizations need to prioritize data security, invest in the latest technologies, and develop strategic partnerships with security experts.
Conclusion
Securing sensitive data is a top priority for individuals and organizations alike. By understanding the common data security threats and best practices, implementing robust security measures, and developing a comprehensive data security strategy, you can protect your sensitive data and prevent cyber threats. Remember, data security is a continuous process that requires ongoing effort and dedication. Stay vigilant, stay informed, and stay ahead of the game.