Understanding Computer Security Compliance
Cybersecurity compliance involves adhering to a set of laws, regulations, and standards designed to protect digital assets and data. These frameworks ensure organizations implement adequate security controls, manage risks effectively, and maintain data integrity, confidentiality, and availability. Achieving compliance minimizes legal repercussions and strengthens an organization's overall security posture.
Why is Computer Security Compliance Important?
Computer security compliance is essential for organizations to protect themselves against cyber threats, data breaches, and other security risks. Non-compliance can result in severe consequences, including financial losses, damage to reputation, and loss of customer trust. By implementing computer security compliance measures, organizations can mitigate these risks and ensure the confidentiality, integrity, and availability of their data.
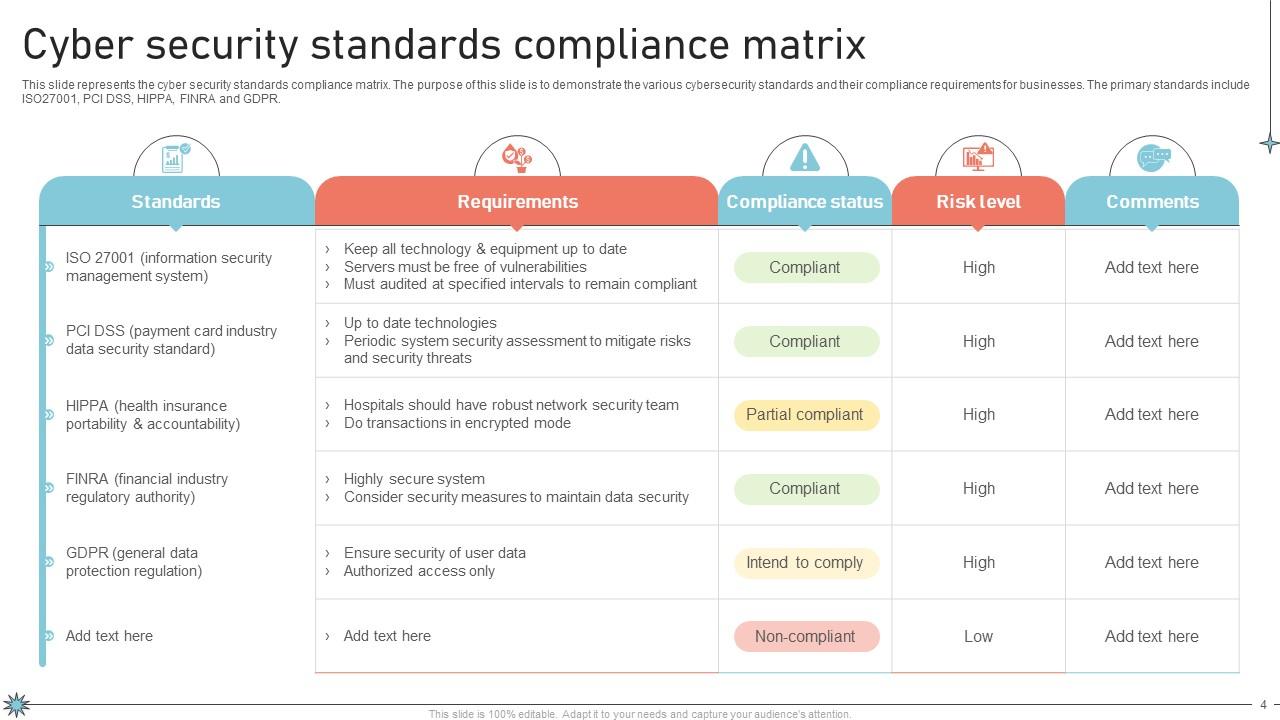
Key Computer Security Compliance Frameworks

- NIST Cybersecurity Framework: Provides a flexible and scalable framework for managing cybersecurity risks.
- Cybersecurity Act of Singapore: Establishes a legal framework for the oversight and maintenance of national cybersecurity.
- HIPAA Compliance: Ensures the protection of sensitive patient information in the healthcare industry.
- GDPR Compliance: Ensures the protection of personal data in the European Union.
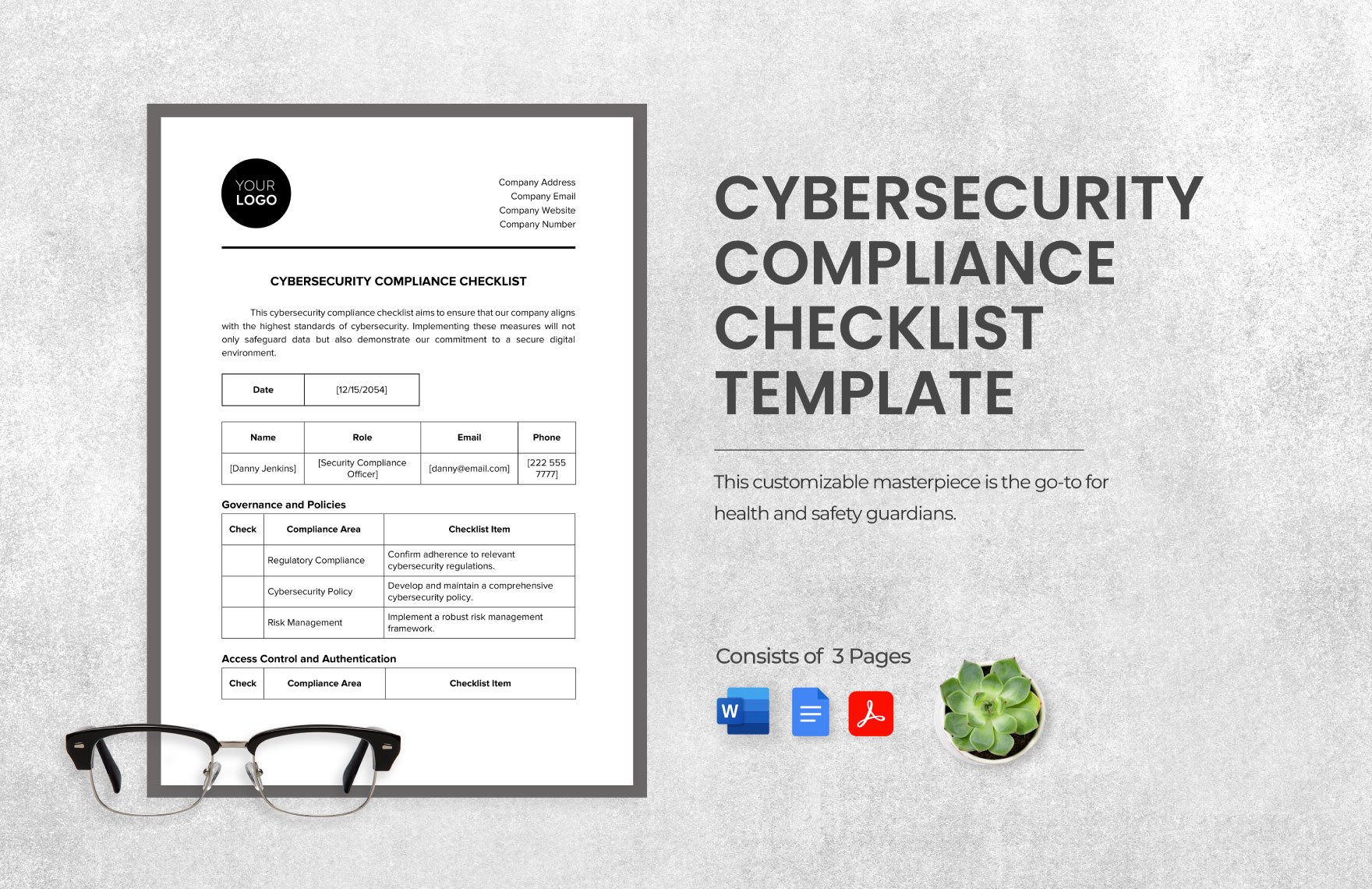
- Conduct a risk assessment to identify potential security risks.
- Implement security controls to mitigate identified risks.
- Develop and maintain incident response plans.
- Regularly monitor and audit security controls.
- Comply with relevant laws and regulations.
Tools and Resources for Computer Security Compliance
- Hyperproof: Provides expert guidance on implementing security controls and achieving audit readiness.
- Computer Security Resource Center (CSRC): Offers information on NIST's cybersecurity-related projects, publications, and events.
- ITL's Standards and Guidelines: Provide recommendations for managing the cost-effective security of non-national security-related information in federal systems.

Furthermore, visual representations like the one above help us fully grasp the concept of Computer Security Compliance.
Conclusion
Computer security compliance is a critical aspect of protecting digital assets and data. By understanding the importance of compliance, key frameworks, and steps to achieve compliance, organizations can mitigate security risks and maintain the trust of their customers. With the right tools and resources, organizations can ensure they are meeting the necessary security controls and minimizing non-compliance risks.
Additional Resources
- Microsoft Intune Device Compliance: Provides information on tenant-wide compliance policy settings and device compliance policies.
- Internet Crime Complaint Center (IC3): The central hub for reporting cyber-enabled crime.
- NIST's Final Post-Quantum Encryption Standards: Provides secure encryption standards for electronic information.